Effective security is simple, open, and automated. In the last blog, I described several efforts by Cisco to pursue simplicity. Now let’s talk about how we are executing on the open part.
Openness is about playing well with others. As a kid I heard it from my parents, and now I find myself saying it to my kids. When kids play well together everyone is happier (including parents!), they get to play longer, and I see them building skills that will benefit them in the long run – working together, appreciating each other’s strengths, and learning from each other.
The same holds true for security.
Today’s threat landscape is vast and changes every day – beyond the ability of any single vendor to confront. That’s why many security organizations report vendor sprawl as a challenge, adding new capabilities to overcome the lack of integrated effectiveness in others. Most organizations who pursue a best of breed approach believe there is a significant people and effectiveness pay-off, but often the chosen solutions don’t play well together and result in a tough-to-manage “frankenstructure” for their operators. Some of them have even told me: “I probably wouldn’t have invested in C if A and B worked together.”
To truly be effective, security solutions must be built with openness in mind. Real openness fosters solutions that actually deliver on the promise of best of breed because they can interoperate. Customers can purchase technologies that solve incrementally more of their security problem and know that they will work together and strengthen defenses.
Cisco builds products designed to interoperate across your entire security infrastructure, not only across our portfolio. We are set on providing products that work well with others. Cisco has really accelerated its openness and multi-vendor integrations in the past couple of years, and I’m excited to share this progress with you.
We view open in three principal areas – open standards and API, open-source communities and our ecosystem of technical partners.
Open APIs, Standards, and Programmability
Open means that products include APIs to extend and automate their security services. Cisco offers more than a dozen APIs and integration points.
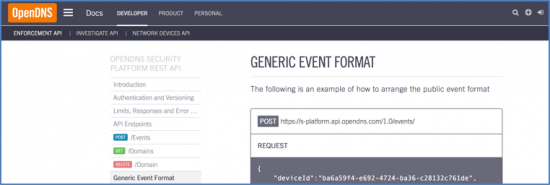
- Cisco Umbrella API – Part of the portfolio via our OpenDNS acquisition, Cisco Umbrella publishes APIs in the public domain. With these APIs, you can feed threat intelligence from any source to the Umbrella product to ensure consistent cloud-based enforcement across all protected devices.

- Cisco Firepower API Explorer – For strong network security integrations, Cisco Firepower, our next-generation firewall and threat appliance, offers multiple REST APIs. You can use multiple firewall technologies (from Cisco, other vendors, or even your own proprietary technology) and share, access, and manage policies across management platforms.

- OpenAppID – Use the LUA language to develop your own open application detection and application control to share with the community, or deploy on your Cisco Firepower or Snort.
- Cisco Threat Intelligence APIs – This pragmatic, operationalized threat intelligence service and data model shares known threat information and provides inputs to threat analysis.
- Cisco Platform Exchange Grid (pxGrid) SDK – A published, technical specification open to every company with relevant security technologies, even Cisco competitors. This framework enables multivendor, cross platform network system collaboration among parts of the IT infrastructure such as security monitoring and detection system, network policy platforms, asset and virtually configuration management, identity and access management platforms, and virtually any other IT operations platform.
- Security-group eXchange Protocol (SXP) – An open standard and one of several protocols that supports Cisco TrustSec. SXP is a control protocol for propagating IP-to-SGT (Security Group Tag) binding information across network devices that do not have the capability to tag packets needed to enable real-time network segmentation.
- eStreamer API – Stream richly detailed Firepower System events to external client applications. You can stream host, discovery, correlation, compliance white list, intrusion, user activity, file, malware, and connection data from a Firepower Management Center.
- Host Input API – Import data from vulnerability management solutions and other sources on your network, such as vulnerability assessment systems, to augment monitored host information in Cisco Firepower platforms.
- Remediation API – Create remediation that your Firepower Management Center can automatically launch when conditions on your network violate the associated correlation policy. A remediation is the response your custom software executes to mitigate the detected condition.
But openness is far more than just APIs.
Open Source Communities
Open source technologies and the communities that surround them allow the world’s greatest minds to come together for innovation. We backup our commitment to openness through leadership in open source communities, such as Snort, OpenAppID, PhishTank, ClamAV, SenderBase and SpamCop. Indeed, open source security is woven into the fabric of Cisco’s vision. Just in the last few months, our Threat Grid team has contributed a rules engine and a way to do rate limiting for multi-node web apps using Redis.
Let’s look quickly at our progress with just 2 of these communities.
- Snort – Snort is the global standard for open source intrusion detection and the foundational technology for Cisco’s network security portfolio. Aside from the OpenAppID rollout two years ago, we’ve been busy working on the next generation of Snort, providing a simpler configuration and an entirely new rule language. Snort shows no signs of slowing down, adding over 1,000 new users a week.
- pxGRID – The 42 member strong community enabled by pxGrid continues to grow quickly. There have been over 800 downloads of our SDK in the last year with 22 new non-Cisco integrations and many more under development. pxGrid is also published as “XMPP-Grid” and is standards-track in the IETF.
We continue to invest in community-based models that enable users to create, share, and implement novel solutions in this dynamic and rapidly changing world. This openness sets the stage for an ecosystem where, together, we accelerate innovation and security effectiveness. Stay tuned for more announcements on this in early 2017.
Security Ecosystem and Technical Partner Community
The Cisco Security Technical Alliance program assembles this ecosystem so you can get more from your existing security investments – better protection, faster detection and resolution of critical events, and lower TCO. We are open to over 120 security partners across all relevant security technology areas allowing our solutions to integrate with security components you have already deployed or plan to deploy– from SIEM to mobile device management to vulnerability management. Partners in the program integrate through open APIs, standards-track integrations like pxGrid, as well as point-to-point integration points. They benefit from interacting with a dedicated team that Cisco provides to help build and maintain integrations.
We won’t stop with the above. Openness lets us integrate security for more integrated threat defenses. At Cisco, we leverage open standards like IPFIX to share flow data from any layer-2 or layer-3 device. As an industry we see more use of common threat languages like STIX and TAXII for a consistent way to share threat information between security products for more effective, automated security. Practically, this means formerly disconnected products like next-gen firewall, email, identity, and web security will now efficiently share and consume threat information, pushing us closer toward our goal of seeing a threat with one product and being able to protect against it everywhere plus deliver an enriched data set for consumption by tools from other vendors.
The need to play well with others is much more than just a rule for the school yard or the back yard. It’s a watchword for one of the key elements of security effectiveness – openness. When products are built with openness in mind they make the entire ecosystem better and dramatically change the security landscape.
Can you say that your organization is leveraging all of the “open” capabilities already built-into the Cisco portfolio? Register for our Cisco Security Community and submit feedback on areas you’d like to see us innovate.
Stay tuned for the final part of the discussion when I’ll focus on how Cisco is incorporating automation into our portfolio of solutions to make security more effective and take the burden off of IT teams.