Microsoft has released their monthly set of security bulletins designed to address security vulnerabilities within their products. This month’s release sees a total of 14 bulletins released which address 58 CVEs. Four bulletins are rated “Critical” this month and address vulnerabilities in Internet Explorer, Graphics Component, Office, and Edge. The other ten bulletins are rated “Important” and address vulnerabilities within Remote Desktop Protocol (RDP), Server Message Block (SMB), XML Core Services, Mount Manager, System Center Operations Manager, UDDI Services, Command Line, WebDAV, Windows, and the .NET Framework. Continue reading “Microsoft Patch Tuesday – August 2015”
Video codecs remain an area of active research and development. The current generation video codec is H.264 – in widespread usage on the Internet. Cisco has actively worked towards making H.264 the foundation of real-time communications on the web. The next generation codecs are just beginning to emerge. There are two of note – Google’s proprietary VP9 codec, and the industry standard H.265 (HEVC) codec, which is the successor to H.264 (AVC).
Unfortunately, the patent licensing situation for H.265 has recently taken a turn for the worse. Two distinct patent licensing pools have formed so far, and many license holders are not represented in either. There is just one license pool for H.264. The total costs to license H.265 from these two pools is up to sixteen times more expensive than H.264, per unit. H.264 had an upper bound on yearly licensing costs, whereas H.265 has no such upper limit.
These licensing terms preclude usage of H.265 in any kind of open source or freely distributed software application, such as web browsers. They also preclude its usage in freemium products – like WebEx or Cisco Spark – which have versions that users can use for free. Thus, while H.265 is still a good fit for hardware products like our telepresence room systems, it is not something that can serve as a universal video codec across hardware and software. Thus, we believe the industry needs a high quality, next-generation codec that can be used everywhere. Continue reading “World, Meet Thor – a Project to Hammer Out a Royalty Free Video Codec”
Cisco UCS M-Series Modular Servers deliver exceptional value for online content delivery like gaming, web serving, transcoding, and HPC. Built around Cisco’s virtual interface card (VIC) technology and the policy-based management of UCS Manager, this new design brings the award-winning architecture and management of Cisco Unified Computing to the world of parallelized workloads.
Continue reading “Latest additions to the Cisco UCS M-Series Modular Server Portfolio”
In a few weeks Spring season will set in, and it’ll be a Ripper Down Under. For the Data Center technology geeks there is plenty of action in store to celebrate the onset of Aussie spring. I am talking about F5 Agility that is getting ready to rock Melbourne (Aug 18) and Sydney (Aug 20)

Just last week, I was at F5 Agility, Washington DC. It was an electrifying experience meeting customers and partners of Cisco and F5 and culminating in a powerful guest keynote by Colin Powell, the legendary American statesman and retired four-star general. Colin’s passion to help youth and transform the globe is totally extra-ordinary and most of us attendees were privileged to listen to him that day. That speech has super charged me to last for a long time, and in that mindset, let me switch context to F5 Agility, Melbourne Aug 18, and Sydney Aug 20. The agenda for both these events are identical. We have a packed set of activities from early morning till late evening. We are going to hear F5’s leaders, customers, and partners share how the latest solutions from F5 are transforming what’s possible for today’s organizations. In about a year’s time Cisco ACI and F5 partnership has demonstrated significant success in our joint solution momentum and customer adoption. I am pleased to invite you all to attend this premier industry event and get insights on how F5 and Cisco are bringing the power of cloud, data centers, converged systems, and as-a-Service together to enable fast, efficient, and secure application delivery in today’s challenging hybrid environments.

The keynote by Julian Eames, F5 EVP of Business Operations, centers on “Innovate, Expand and Deliver” and lays the foundation for your business to innovate new paths to success, expand through barriers to growth, and deliver the applications your customers need to succeed. Julian will take you a tour of current market trends, how F5 has grown under John McAdam’s tenure, the evolution of the F5 Platform from simple load balancer to ADC to support Cloud based business models, the growing importance of enterprise security, recent F5 acquisitions, and last but not the least the growing eco-system of Partners. I recommend getting started with Julian’s keynote.

Following the keynote, Cisco Exec Shashi Kiran is hosting the Plenary, Platinum Sponsor session titled “Deliver Application Agility with Cisco Application Centric Infrastructure (ACI)”, 10.30 am local time. What’s unique about this Breakout Session? You will get the opportunity to hear Shashi eloquently walk you through the role of Cisco ACI in today’s Application-Oriented Economy, also see a key partner join him on stage and share their success stories with ACI. Shashi will discuss how emerging applications are placing huge demands on Data Center Infrastructure and how grossly unprepared they are to meet the same. Shashi will then introduce Cisco ACI, an open, scalable, programmable SDN solution that helps address these infrastructure challenges. Shashi will illustrate how Cisco’s open architecture enables seamless integration of F5 into ACI’s policy framework and how the joint solution brings unprecedented agility and end-end L2-L7 accelerated application delivery.
Shashi is also doing the Plenary Panel Session in the evening jointly with F5 Execs and the Guest Customer speaker. The topic centers around global trends and themes around Cloud adoption and drivers, SDN, Security etc. This session will be invigorating and sets the stage for a lively evening solutions expo tour.
For the technically oriented among you, we also have a number of technical breakout sessions hosted by F5 and its Partners. These sessions cover Security, Cloud in detail along-with other emerging Data center topics.
That is not all. Cisco ACI brings you additional customer engagement opportunity in the solutions expo hall. We are featuring cool demos showcasing our joint solutions namely, ACI -F5 BIG-IP and ACI – BIG-IQ on both Aug 18 and 20, during the expo hours. Stop by the Cisco booth where product experts are available to engage in white-board sessions and to compliment the demos, we also run short duration presentations in the Cisco theatre at periodic intervals. Should you desire, we are happy to meet you in 1-1 meetings, so let us know how we can enrich your experience at the event
For all the hard work we all do at the event, there is plenty F5 offers to let us relax and enjoy. The networking event at the solutions expo in the evening (5 – 7 PM) provides drinks and prize draws in addition to an exciting showcase of state of art technology innovations and demos. Network with your fellow attendees while enjoying tasty food and drink, knowledgeable guides, and more are awaiting you.
I am eager to see you all in Australia next week. There are some useful links for you to check out before your visit on how Cisco ACI and F5 work together on the innovation front.
For more information, Visit www.cisco.com/go/acif5
Join our Community discussions on ACI and find out “What is your SDN Spirit Animal?”
Today’s guest blog comes to us courtesy of Tesora CEO, Ken Rugg.

The Cisco Intercloud is a pretty amazing demonstration of the power of OpenStack. It will have incredible worldwide reach with 350 data centers across 50 countries. Unlike Microsoft, Amazon, and Google, however, Cisco isn’t building all the data centers itself. Instead it is relying on its telecommunications service provider partners to provide most of that capacity with companies like Telefonica in Spain, Deutsche Telecom in Germany and Telstra in Australia.
Of course, as powerful as this kind of open cloud may be, it’s only going to be as successful as the applications and services that are built on top of it. This is another area where Cisco is pushing to become a leader, starting with a stable of 35 independent software vendors in areas such as big data, Internet of Things, and software development environments.
One important core Intercloud service will be Database as a Service (DBaaS). In this area, they will be deploying the core OpenStack Trove service to provide database capacity on-demand for many popular databases such as PostgreSQL, MySQL, and Cassandra.
If you’d like to learn more about how this service is being implemented and delivered, you should mark your calendar for OpenStack Trove Day, being held on August 25th in San Jose, CA. Dave Lively, Director Product Management for Cisco Cloud will present how Cisco is working with Tesora to deliver DBaaS to Intercloud customers as a native service.
The event is free and you can register here.
What happens when more than 100 entrepreneurs embark on a 72-hour bus journey to concept, design and pitch the next big tech thing?
With the right flow, pretty much anything they can imagine.
StartupBus is one of the most unusual startup competitions around. In a nutshell, the competition invites the best “Hackers” (programmers and coders), “Hustlers” (business and marketing minds) and “Hipsters” (designers and other creatives) to board a bus and form teams to conceptualize and design a tech-focused prototype or app with all of their hard work culminating in epic pitches to StartupBus judges and investors.
And they only have 72 hours to do it.
Earlier this summer, five buses in North America were a flurry of activity as “Buspreneurs” neglected sleep, overcame motion sickness, and tapped into strong competitive spirits to embrace the intense collaborative energy needed to perfect their pitches. The buses, originating from five regions (Mexico, Midwest, Northeast, Southeast and West Coast) headed to Nashville for Accelerate, the ultimate “unconference” where the Buspreneurs would make their pitches.
https://www.youtube.com/watch?v=IEa99OCOb44
Continue reading “What Happens When You Put Cisco Spark on a Bus?”
When we think of “cloud” we think of a vast collection of compute, network, and storage capabilities that resides somewhere high above us—a massive repository of functionality that can be accessed from anywhere and any device with enough bandwidth to handle the data flow.
With practically unlimited power and scalability, cloud technology has been a key enabler of the Internet. But the Internet of Things (IoT) demands something more. IoT is a broad collection of sensors, cameras, smartphones, computers, and machines—all connected to and communicating with applications, websites, social media, and other devices. To maximize value, much of the data generated by these “things” must be processed and analyzed in real time. For example, sensors and cameras in and around a large retail store may continuously collect data about customer volume and traffic flow. The store can derive some value from all this data by sending it back to the cloud to analyze long-term trends. But the value is multiplied if the system can process the data locally, in real time, and then act on it immediately by sending more cashiers to the check-out line just before a surge in customer traffic.
This sort of real-time, high-bandwidth application requires a new distributed cloud model that brings cloud networking, compute, and storage capabilities down to earth—to the very edge of the network. My friend Flavio Bonomi has worked tirelessly with both academia and other industry partners to advance the concept of fog, inspired by the way the San Francisco fog extends the cloud to the ground. Fog computing creates a platform—what we call a fog node—that provides a layer of compute, storage, and networking services between end devices “on the ground” and cloud computing data centers. Fog is not a separate architecture; it merely extends the existing cloud architecture to the edge of the network—as close to the source of the data as possible—to enable real-time data processing and analytics. Continue reading “Fog Computing: Bringing Cloud Capabilities Down to Earth”
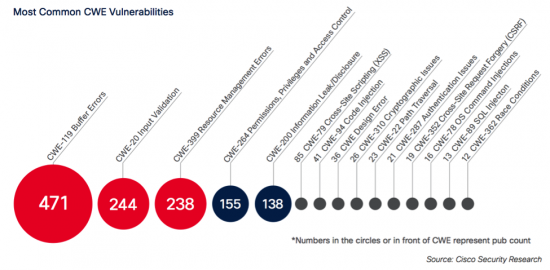
Coding errors in software products provide easy paths of entry for online criminals, who can exploit vulnerabilities to compromise systems or launch additional attacks and malware. As reported in the Cisco 2015 Midyear Security Report, certain types of coding errors consistently appear on lists of most common vulnerabilities. This raises an important question for vendors and security professionals: If the same coding errors are identified year in and year out, why aren’t these errors being mitigated?
Buffer errors, input validation, and resource errors are usually among the most common coding errors exploited by criminals, according to the list of Common Weakness Enumeration (CWE) threat categories. As we explain in the Midyear Security Report, the likely culprit is the lack of sufficient attention paid to security during the product development lifecycle. In many cases, vendors wait until products come to market, and only then resolve vulnerabilities. However, this process should be reversed. Vendors should build security safeguards and conduct vulnerability testing during product development, in order to lessen the chance that criminals can profit – and customers can suffer.
This post was authored by Mahdi Namazifar and Yuxi Pan
Once a piece of malware has been successfully installed on a vulnerable system one of the first orders of business is for the malware to reach out to the remote command-and-control (C&C) servers in order to receive further instructions, updates and/or to exfiltrate valuable user data. If the rendezvous points with the C&C servers are hardcoded in the malware the communication can be effectively cut off by blacklisting, which limits the malware’s further operation and the extent of their damage.
To avoid such static detection mechanisms recent attackers have been taking advantage of various Domain Generation Algorithms (DGA) in choosing and updating the domain names of their C&C servers. DGA embedded in the malware generate a large amount of pseudo-random domain names within a given period, most of which are nonexistent. With the same random seed, e.g. time of the day or most popular tweets of the day, the attackers can generate exactly the same list of domain names remotely, among which they will only register a few. The malware will contact some or all of the domains generated by the DGA, giving its opportunity to be able to connect to the C&C server. The sheer amount of nonexistent domains produced by the DGA on a daily basis presents a great burden for security specialists if blacklisting is still to be pursued.
Continue reading “Research Spotlight: Detecting Algorithmically Generated Domains”