This blog has been developed in association with Javed Asghar, Insieme Business Unit
The Cisco ACI Platform consists of the Cisco APIC controller and Nexus 9000 series switches connected in a spine/leaf topology in a CLOS architecture configuration. All management interfaces (REST API, web GUI and CLI) are authenticated in ACI using AAA services (LDAP, AD, RADIUS, TACACS+) and RBAC policies which maps users to roles and domain.
The ACI fabric is inherently secure because it uses a zero trust model and relies on many layers of security: Here are the highlights:
- All devices attached to the ACI fabric use a HW-based secure keystore:
– All certificates are unique, digitally signed and encrypted at manufacturing time
– The Cisco APIC controllers use Trusted Platform Module (TPM) HW crypto modules
– The Cisco Nexus 9000 series switches use Trust Anchor Module (TAM) to store digitally signed certificates - During ACI fabric bring-up or while adding a new device to an existing ACI fabric, all devices are authenticated based on their digitally signed certificates and identity information.
- Downloading and image bootup:
– All fabric switch images are digitally signed using RSA-2048 bit private keys
– When the image is loaded onto an ACI fabric device, the signed image must always be verified for its authenticity using hardware rooted Cisco Secure Boot
– Once the verification is complete “only then” the image can be loaded onto the device - The ACI fabric system architecture completely isolates management vlan, infrastructure vlan and all tenant data-plane traffic from each other. (The Cisco APIC communicates in the infrastructure VLAN (in-band))
- The infrastructure VLAN traffic is fully isolated from all tenant (data-plane) traffic and management vlan traffic.
- All messaging on infrastructure vlan used for bring-up, image management, configuration, monitoring and operation are encrypted using TLS 1.2.
- After a device is fully authenticated, the network admin inspects and approves the device into the ACI fabric.
These are various layers of security built into ACI’s architecture to prevent rogue/tampered device access into the ACI fabric.
Please stay tuned for a blog posting by Praveen Jain (ACI Engineering VP) which will cover the APIC and Fabric security is more detail in coming weeks
Praveen Jain’s recent blogs:
New Innovations for L4-7 Network Services Integration with Cisco’s ACI Approach
Micro-segmentation: Enhancing Security and Operational Simplicity with Cisco ACI
Network Security Considerations
Additional Information:
The Cisco Application Policy Infrastructure Controller
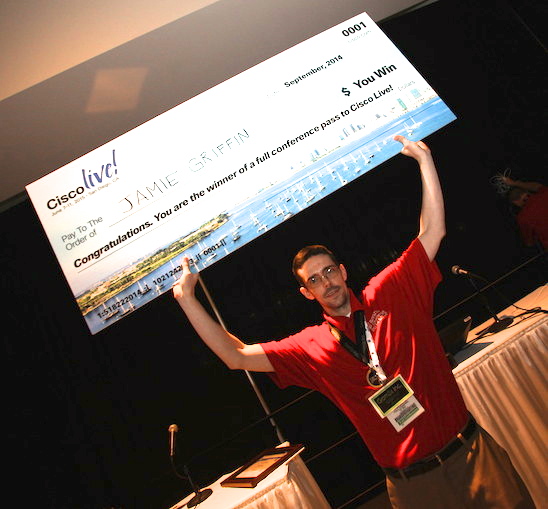 s become an event that I look forward to each year. I have participated for 2 years now and plan to return for a third at this year’s Cable-Tec Expo in New Orleans. It’s a great opportunity to test your own skills, meet industry colleagues, and enjoy some friendly competition.
s become an event that I look forward to each year. I have participated for 2 years now and plan to return for a third at this year’s Cable-Tec Expo in New Orleans. It’s a great opportunity to test your own skills, meet industry colleagues, and enjoy some friendly competition.
 Written by Ian Mc Garry, CMX Software Engineer
Written by Ian Mc Garry, CMX Software Engineer 

