Mobile security is a top concern for IT and business leaders. This guest authored blog series with Dimension Data explores how organizational leaders can work together to mitigate concern and implement clearly defined policies to achieve mobility goals. We are pleased to introduce our guest author Darryl Wilson, Director, Enterprise Mobility for Dimension Data Americas, as the first in this series – Darryl will address how a balanced approach to security can yield better business results.


By Guest Contributor Darryl Wilson
Director, Enterprise Mobility for Dimension Data Americas
Darryl Wilson has more than 15 years of experience overseeing large scale network communications projects both from a technical delivery and pre-sales perspective. Wilson’s areas of expertise include unified communications, network performance, troubleshooting and optimization.
The evolution to a mobile-centric workforce has been relatively short, thanks to an explosion of innovation and emerging mobile and cloud technologies. Just a few years ago, BYOD was a hot topic of conversation and mobile device management (MDM) solutions offered a simple way to secure an influx of devices and users.
However, today we are seeing that the tactical implementation of MDM solutions is not enough to control a multi-device, multi-vendor, and multi-OS mobility landscape. In fact, most of the companies I work with are using solutions that have not been optimized or customized for today’s ever-changing mobile world. In addition, security concerns have left many organizations feeling like they need to choose between control and truly reaping the business value mobility offers.
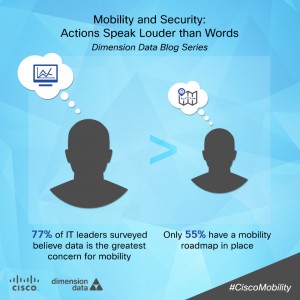
For example, in a recent Dimension Data Secure Mobility Survey Report, 79% say mobility is a top priority for their organization. However, the report indicates that a much smaller segment of those IT leaders’ actions back it up. Seventy-seven percent of those surveyed believe data is the greatest concern pertaining to mobility, yet only 55% have a mobility roadmap in place. If securing company data and successfully implementing a mobile policy is of such importance, why aren’t more IT leaders taking strategic action?
From Thinking to Doing: Implementing the Right Action for Secure Mobility
While the figure above points to the fact that many business and IT leaders understand secure mobility is a priority, many still need to shift their thinking to deploy the right kind of action.
For starters, enterprises must embrace a holistic and balanced approach to secure mobility. It is an area that touches all the towers within IT – from users to devices – and today’s approach can no longer be siloed or looked at through a very narrow lens, such as thinking that an MDM solution is all that is needed.
Organizations that are truly seeing business change are implementing a secure mobility strategy within the framework of an end-user computing strategy. That is to say, their approach to mobility and security is optimized to deliver efficiency to the end-user, regardless of where they are or what device they are using. Security controls must be continually adapted to accommodate this roaming endpoint.
A Secure Mobility Strategy
According to a 2013 Dimension Data Network Barometer Report, 67% of all devices, all of which are on mature networks, carry at least one known security vulnerability – which adds an increasing amount of complexity and opportunity for intrusion. To mitigate these security risks, well-defined network policies must be put in place to secure mobile workers and the infrastructure.
Throughout this four-part blog series, we will discuss considerations for implementing security policies, why embracing secure mobility must come from the top-down, and what this all means for the future of mobility. As mobility evolves, organizations need to act quickly and continually investigate what’s going on in the marketplace to ensure the secure mobility strategy is in line with business goals and objectives. In this case, strategic action speaks louder than words.
For more information about secure approaches to mobility, visit Cisco’s Navigating Security Threats in a Mobile World and join the conversation by following @Cisco_Mobility on Twitter, #FutureOfMobility.
Additional Resources:
- See more findings in the Dimension Data Secure Mobility Survey Report
- Read How Secure is Your Mobile Worker? by Cisco’s Kathy Trahan
- Download a copy of Cisco’s 2014 Annual Security Report
- Review Forrester’s Total Economic Impact on Secure Access Study, commissioned by Cisco






LiveEnsure is multi factor (device, location, knowledge, and behaviour) SaaS authentication solution that delivers mobile security without using passwords, cookies, dongles, tokens, etc. The simple integration with sites and frictionless use for consumers allows an enterprise to scale it’s cloud business without compromising security. The “roaming end point” mentioned in the article and the adaptability and integration across all devices is easily resolved by LiveEnsure.