New troubling cyberattacks are in the news almost daily. No one is immune. Have you checked your credit score lately? I just finished freezing mine. A national credit bureau breach is the latest wide-ranging theft of data to hit the news.
You are probably wondering: “Is my network secure and what would happen if we were infiltrated?” When I heard news of WannaCry ransomware blanketing all forms of mainstream media on May 12th, heck, as a security professional, even I was worried about losing all of the financial and personal data stored on my home network. When hackers weaponized seemingly innocuous IP cameras with the Mirai botnet, we were all alerted to the growing number of seemingly safe devices ingenious cyber terrorists can exploit. And to top it all off, a new type of threat has emerged: destruction of service (DeOS) attacks. No longer are criminals just trying to extort Bitcoins, they are selling their services to literally ruin targeted systems, potentially for paid industrial espionage or to further political ideals. The Nyetya attack was a highly publicized example of DeOS. Utilizing unpatched Microsoft vulnerabilities, criminals infiltrated systems to render them unusable, with no intention of collecting ransom or restoring data.
Multilayered, Architectural Approach to Network Security
Trying to protect your network from all manner of creative malware is a never-ending battle. Each new attack finds new vulnerabilities or gullible web-surfers to exploit. Not only do you want to avoid paying a ransom, but you could potentially lose your entire business infrastructure. When you add the latest security miracle cure to your infrastructure only to compound management complexity without improving protection, it is time for a new approach. New attack vectors are constantly being innovated by those in the business of cybercrime. Patching together solutions is no longer enough. To stay ahead of the bad guys, you need a multilayered, architectural approach to security that will not only block known threats and malware from entering your network, but a comprehensive solution that quickly identifies and contains unknown threats that sneak in when unsuspecting employees click on a phishing email or attachment they shouldn’t have…
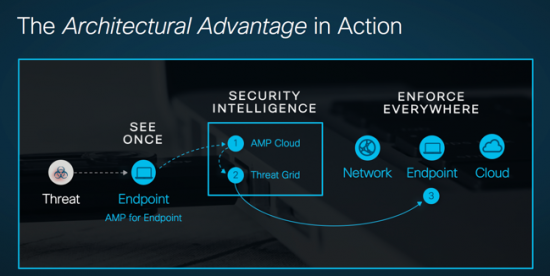
The Cisco security architecture does just that. It integrates security across the network, endpoints, cloud/DNS and email for a more effective security posture that sees a threat once and protects against it everywhere. It uniquely starts with the Cisco’s Intuitive Network as its security foundation. To the Digital Network Architecture, we add best-in-class, independently-tested security components that know what bad stuff to block, and how to share critical security data among each element within the architecture to stop threats fast. Essential to staying on top of the up-to-the-minute global threat landscape is our Talos threat research organization. Talos collects, investigates, and disseminates the latest threat intelligence to each security component in your network so they can block and contain threats that evade front-line defenses before they can cause major damage. Our mean time to detection is just 3.5 hours compared with the industry average of 100 days!
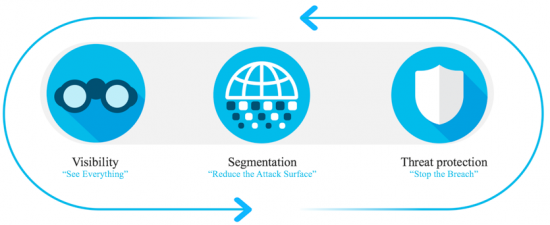
The crucial first line of defense is protecting your internet edge with Firepower next-generation firewalls to “see everything” entering your network. Firepower NGFWs deliver complete visibility of users, devices, connections, applications, workloads and processes operating in your network. Next, we reduce the attack surface with “segmentation” to prevent attackers from moving laterally to sensitive areas in your network with application whitelisting and micro-segmentation. And most importantly, Cisco’s Firepower NGFWs provide industry-leading “threat protection” that is 99% effective at detecting and blocking known attacks including the most potent, ransomware-packing malware. For unknown attacks, our AMP anti-malware component quickly detects and responds to unexpected behavior before hackers can steal data or disrupt operations. With our architectural approach to network security and products designed to fit and work together, we stop more threats outright, lower costs with faster IT and security responses.
With Cisco’s multi-layered architectural approach to security, you can rest easy with the most effective defense: security everywhere across your entire IT infrastructure. Learn more about our security portfolio here: https://www.cisco.com/c/en/us/products/security/portfolio.html





