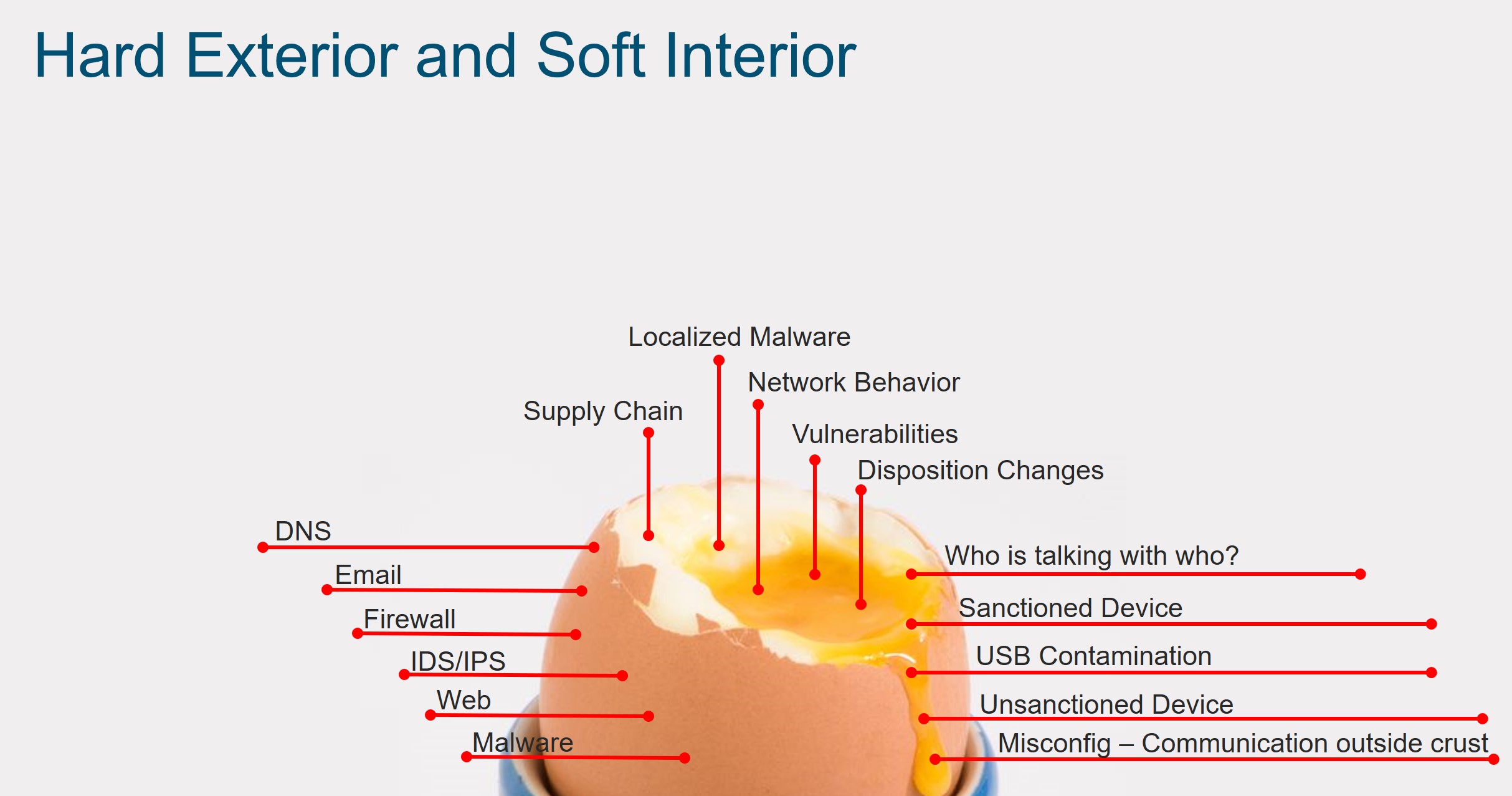
Mid- to large-sized enterprises have for many years built the operational technology (OT) environment like an egg – a hard exterior protected by traditional security elements such as firewalls, IDS/IPS, and malware detection (if you are lucky), but a soft interior leaving critical operational assets at risk against advanced threats and non-existent visibility.
As companies continue to digitize, more and more devices are getting added to the network. Therefore, visibility into the operational network has become critical in order to maintain secured operations. The image below highlights some of the things you may want to consider when it comes to securing the operational environment in today’s threat landscape.
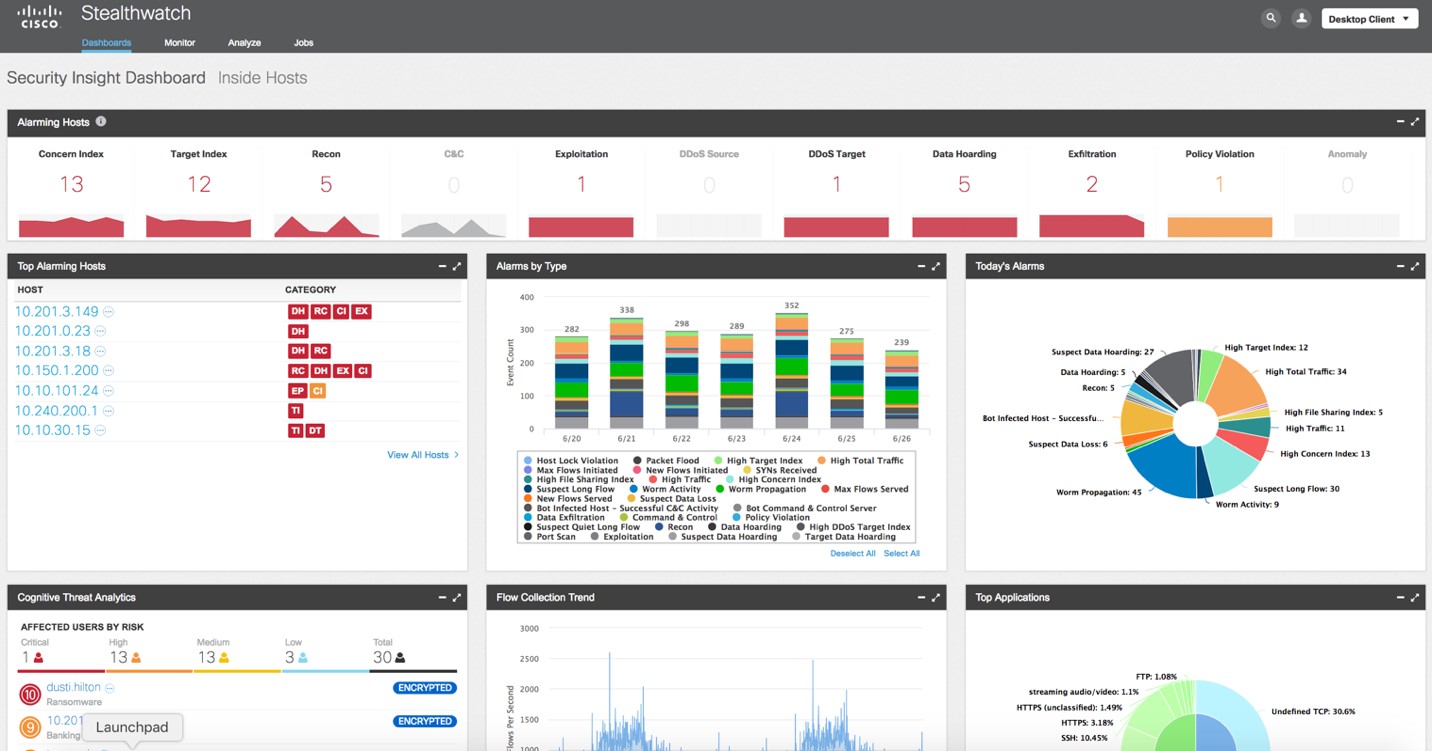
Cisco Stealthwatch overcomes the visibility and security analytics challenges by maximizing existing investments in your network infrastructure. It collects the rich network telemetry (NetFlow, sFlow, etc.), and performs a baseline of the network environment using behavioral analytics and multilayered machine learning to detect what is abnormal. We will discuss this in more detail but first let’s discuss the challenges most organizations are faced with today.
A hard exterior may include one, many, or all of the following items: firewalls, intrusion detection/prevention systems, content protection, DNS based controls, malware inspection, and email. These controls and inspection points may exist at the edge of the operational environment and/or within the business network. In the past, this was able to reduce a significant amount of risk to the operational environment but in today’s world it’s no longer enough. A soft interior presents a variety of risks which may include:
- Supply Chain: The firmware you downloaded was compromised by a bad actor – would you be able to determine or alarm on subtle behavioral changes to the network indicating something of interest?
- Normal Operations: Do you truly understand how the network operates 24x7x365 and are you able to detect changes based on new behaviors? These changes may be related to a security event but also may be based on a misconfiguration.
- Localized Malware: Malware introduced to systems from field technicians, contractors, USB keys, etc. Would you be able to detect the changes to the network behavior based on this new threat?
- Protection Agents such as anti-virus: Not all of your assets within the operational environment will support agents and/or the vendor will not allow agents onto systems and if installed, the vendor may revoke support. The network provides an opportunity to detect anomalous and/or bad behaviors without an agent
- Confidence in the control: Are you certain the controls in place are working 100% of the time. What about the fat finger syndrome when adding a control? Are systems talking to systems they should not be? The network can provide this much needed insight
- Compliance/Audit: Today, the audit process may include examining multiple access control lists and requires multiple teams highlighting if a control exists and if the communication to the environment meets the compliance requirement. Does this really ensure that the control was accurate throughout the year or only during the audit? The network can provide you the ability to go back throughout the year and prove the control was in place and no unauthorized communication took place
These are some simple examples of some of the challenges and risks when deploying a hard exterior only. As the operational environment continues to evolve and IP becomes more prevalent deeper within the operational environment, there is an opportunity to gain greater visibility leveraging network telemetry data; something that your operational environment may produce today. Note: not all telemetry data is the same but leveraging a technology that supports multiple network telemetry is advantageous to the consumer allowing for greater coverage.
Some of the benefits of leveraging the network not only include visibility into the operational process but also assists in troubleshooting the environment. I have captured a few of the business outcomes we have seen in customers’ environments as a result of deploying Cisco’s Stealthwatch solution.
- Host group zoning (or creating a logical boundary) within the operational environment to alarm on communications activity that violated the logical trust boundary. Business outcome: risks to the environment identified earlier in the process to maintain secure and trusted operations
- Anomaly detection discovered a compromised camera port-scanning the network. Business outcome: significantly reduced the time to detect and allowed the team to mitigate the threat sooner. No business operation disruption
- Problematic wireless access point on the factory floor that was occasionally flooding the plant floor with goofy packets. Business outcome: issue was mitigated sooner, which ensured that the integrity of the network was maintained
- Connectivity aberrations in the distribution network – abnormal but not necessarily an attack. Business outcome: optimized the network ensuring maximum operational uptime before the incident was realized within the operational environment
- Systems chatting with things that were supposed to be retired. Business outcome: removal of retired assets reducing the potential threat vector from the environment and optimization of the environment
- A spike in traffic that was not an attack itself but an indicator of change that may have disrupted the operational network if left unexamined. Business outcome: quickly identified the issue which allowed the right team to be engaged to mitigate the spike in traffic. This also removed the concern around a potential security breach optimizing resource allocation and reduced mean time to repair.
Cisco Stealthwatch provides deep visibility leveraging metadata (telemetry) from the network providing security at scale. It also integrates with other solutions to do full packet capture in areas where this is required. Stealthwatch can ingest any kind of telemetry from across the extended network including end-points, branch, data center, and cloud. Behavioral-based analytics, machine learning, and global threat intelligence that is 100% out-of-band is a recipe for success both in IT and OT environments!
In my next blog, I’ll expand on how to continue to add security within what was once a soft interior leveraging Cisco’s integrated architectural approach to security.
To learn more about Cisco Stealthwatch, go to https://www.cisco.com/go/stealthwatch






It's really wonderful article about the security and thanks for sharing wonderful article with us.