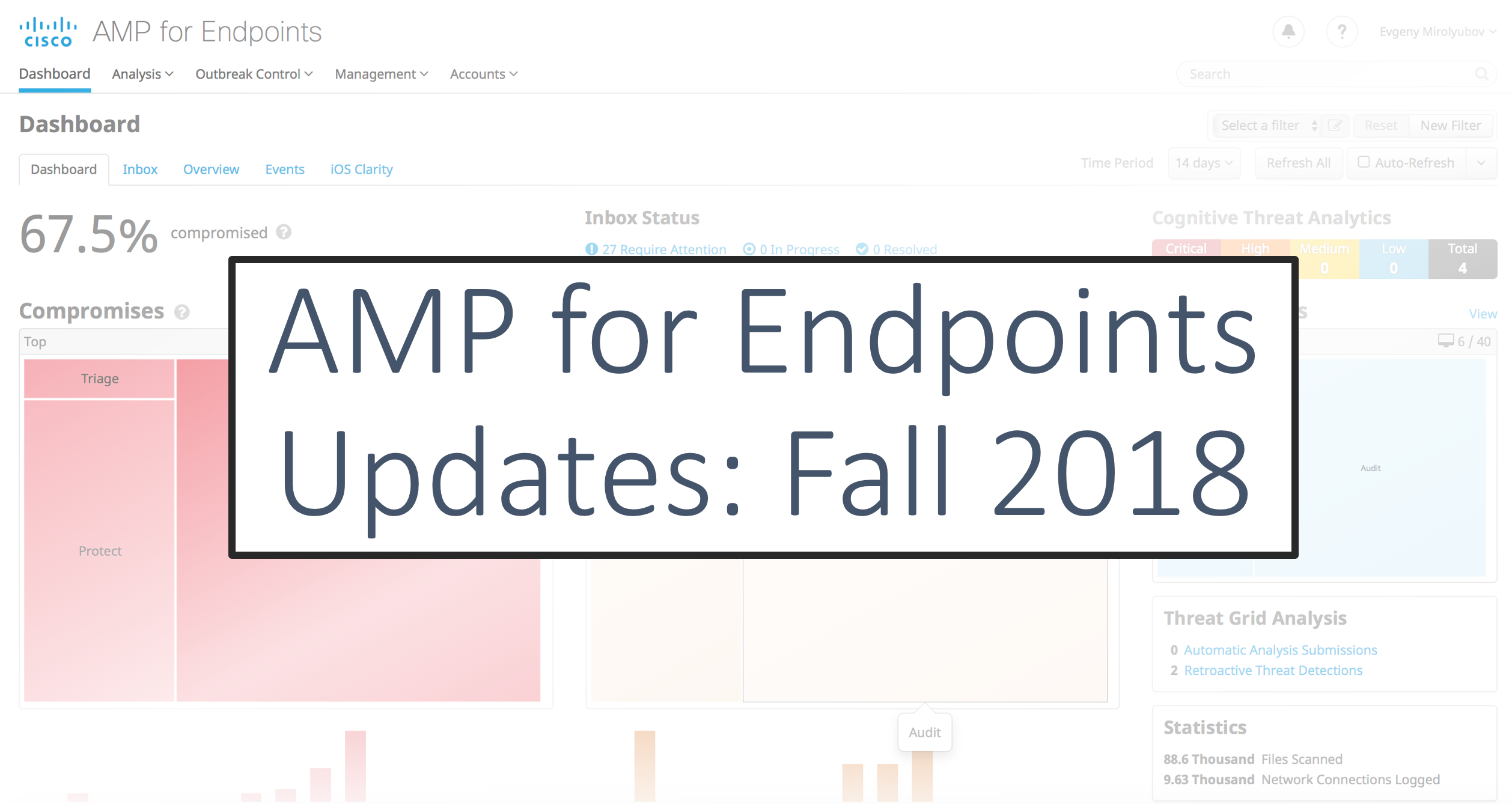
Compromise Assessment vs Threat Hunting
While table top exercises are always a hot commodity for our customers, proactive threat hunting and compromise assessments are becoming increasingly popular through our Cisco Incident Response Readiness & Retainer service.