This blog is continuation of the previous blog on using Cisco Secure Network Analytics. In this part, we cover leveraging public Cisco Talos blogs and third-party threat intelligence data with Cisco Secure Network Analytics. Be sure to read the first part as this part makes references back to Host Group and Custom Security Event instructions covered in the original blog.
Cisco Talos Blogs
The talented researchers at Cisco Talos regularly publish blogs on threats and vulnerabilities. These blogs break down the tactics, techniques and procedures (TTPs) used by threat actors. Talos’ research publications often include sample source code, phishing emails, reverse engineering of malicious binaries, tools, scripts, command and control methodology, attacker infrastructure, file hashes, domains and IP addresses used in malicious operations. The indicators of compromise (IOCs) are published on GitHub as JSON and plain text files. We can use these blogs and GitHub files to build Custom Security Events in Cisco Secure Network Analytics.
Let’s look at a blog: MoonPeak malware from North Korean actors unveils new details on attacker infrastructure. This blog focuses on a state-sponsored group from North Korea. The group leverages an open-source remote access trojan (RAT) from a family being called MoonPeak.

Scroll through the article and pay attention to the level of detail provided. Near the very bottom of the blog notice the section titled IOCs.
Click on the link to the GitHub repository. You will be taken to the Cisco Talos GitHub repository where you will find the IOCs are available as JSON and plain text files, and are sorted by the month the blog was published in. Feel free to explore other files, months, and years to get familiar with the indicators regularly provided.
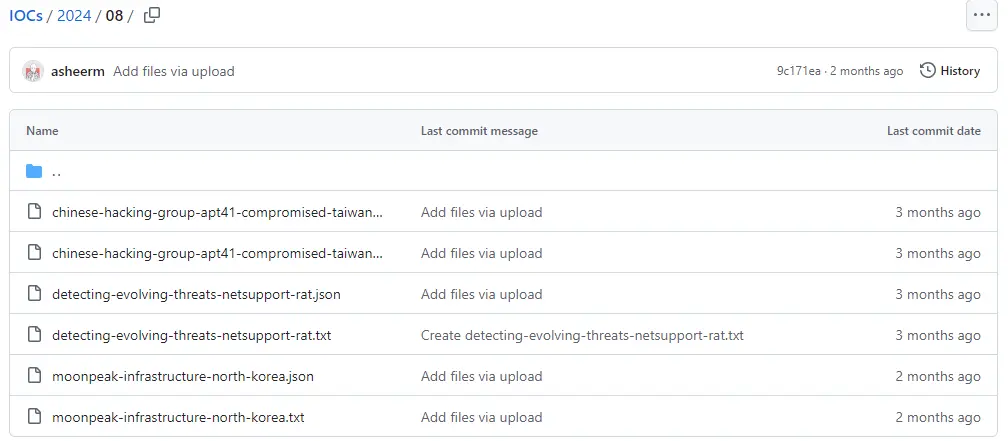
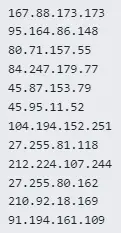
Click on the file “moonpeak-infrastructure-north-korea.txt” or follow the direct link. Scroll down to line 35 of the file where the Network IOCs begin. This list contains twelve IP addresses we are interested in. Noticed that the IP addresses and domains have been defanged with square brackets around the dots so you cannot accidentally click on them.
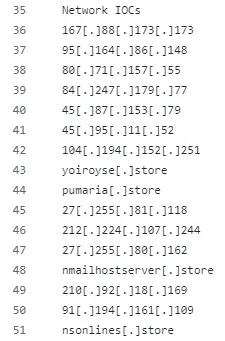
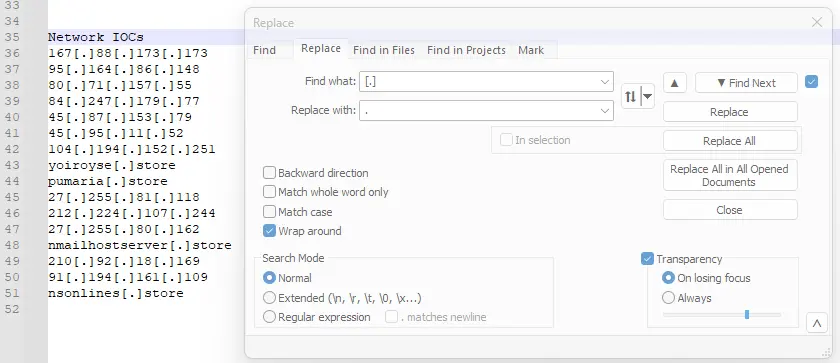
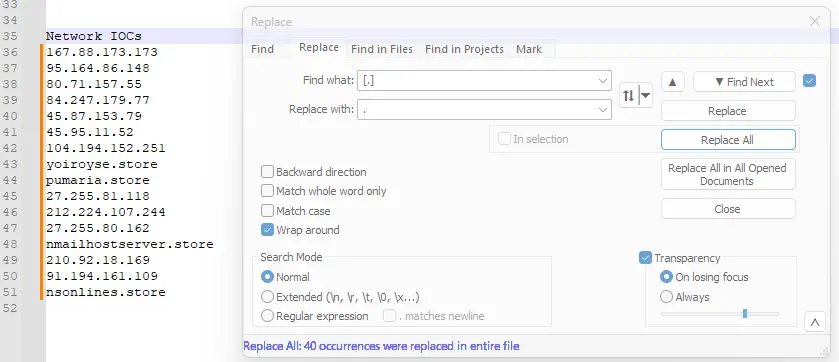
You can either manually delete the square brackets or use the find and replace functionality in your favorite text editor to do the job. I prefer to use Notepad++ when dealing with text files. I set the “Find and Replace” to look for the square brackets around the dot and replace all instances with a dot.
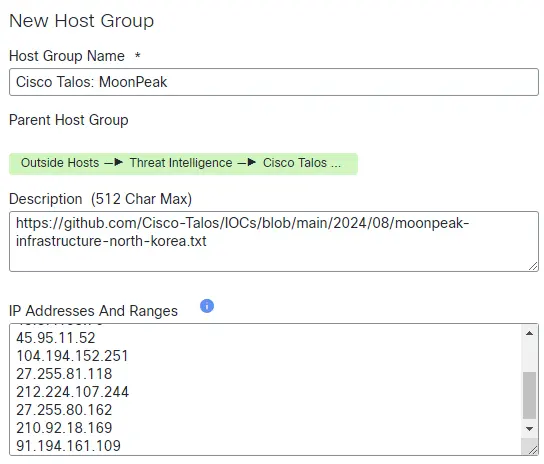
Delete the domains from the list and copy and paste these IP addresses into a New Host Group using the techniques described in the first part of this blog.
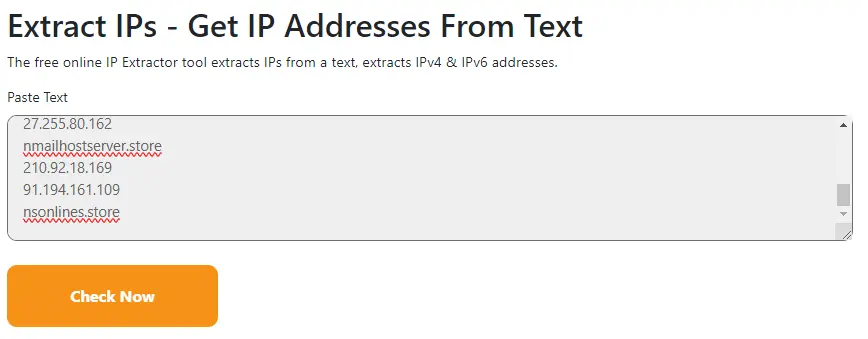
You may also consider using a tool to extract IP addresses from text. I really like iplocation IP Extractor. You can paste in a block of text with IPv4 and IPv6 IP addresses and it will extract them so they can be easily reviewed and pasted into a host group. The IPs you paste into this tool cannot be defanged. It requires full and correct IP addresses to work.
Always consider the sensitivity of the information you provide to public tools before using them. You should consider a locally hosted tool for sensitive information
Third-party threat intelligence
If you participate in any Information Sharing and Analysis Centers (ISACs), subscribe to commercial feeds or regularly utilize bulletins and blogs geared towards your industry, you can also utilize their indicators in Cisco Secure Network Analytics. They work the same way we handled internal threat intelligence in the first part of this blog or Cisco Talos blogs shown above. Be careful when scraping threat intelligence to be sure you are only including indicators you intend to use. For example, if you are scraping an entire bulletin that contains IP addresses you are interested in, make sure you don’t accidentally copy an IP address from an adjacent and unrelated entry.
You can paste a block of IP addresses into a New Host Group or use a tool to pull them out of a block of text and then paste them. Be careful if your source defangs IP addresses, as this is very common. You can use the same techniques I illustrated for the Cisco Talos GitHub entries above.
Host group parent/child relationships
A good practice for building parent and child host groups is to create a new parent host group for any distinct sources. Then create a child host group for each new report. This allows you to easily track back both to the original source or the threat intelligence and identify which campaign or threat actor is involved. I like to include a link to the source in the host group description. This is especially helpful if you are utilizing multiple threat intelligence sources for your security controls. Organize your host groups in a manner that makes the most sense to you.
You can either create a new Custom Security Event (see the first part of this blog) for each child host group with a distinct name or create one Custom Security Event for the parent host group with a generic name. Either case will have you covered, and the host group name in the alarm will help you quickly identify the source of threat intelligence.
Other Considerations
You always want to perform a Flow Search (Investigate -> Flow Search) first before building any Custom Security Events. This will prevent you from flooding yourself with alerts if you accidentally include the wrong IP address or are already regularly communicating with an IP address you intend to include in a new host group.
We’d love to hear what you think. Ask a Question, Comment Below, and Stay Connected with Cisco Secure on social!
Cisco Security Social Channels





