Zero trust is misnamed
There’s been many management approaches that include the “Zero” term. In shipping, there was “Zero Inventory”. In manufacturing, there was “Zero Defects”. In environmental planning, there’s “Zero Waste”. So, it’s not surprising that the security industry has adopted “Zero Trust” or its “Zero Trust Networking” (ZTN) and “Zero Trust eXtended” (ZTX) variants as it’s buzzword. I bet you will see this term plastered on vendors booths at RSA Conference this year. But without trust, how would your digital business get things done? Gartner’s Neil MacDonald makes the argument that “zero trust is misnamed” in his latest report, “Zero Trust Is an Initial Step on the Roadmap to CARTA” (click here to read it now). Whether it’s Forrester ZTX or Gartner CARTA, both approaches allow businesses to operate in a risk-appropriate manner by enabling better access security decisions.
Use cases that matter
Before we jump into any comparisons, let’s explore some use cases to illustrate why it matters to your business. One example is your CEO accessing Microsoft Office 365—maybe even with her unmanaged iPhone. How do you know that she didn’t get phished and an attacker is logging in with her stolen credentials? Is her device’s screen-lock turned on, OS and browser up to date, and not jailbroken? Another example is your HVAC system accessing the campus network. Were you aware that the OT team installed this without telling IT? Do you know if it meets your IoT requirements or if it’s communicating with things it should not? And don’t forget about your in-house app with containerized workloads accessing each other across a hybrid cloud data center infrastructure. Did your DevOps team document how it’s supposed to communicate or how its services stay up to date? Unlikely, so how do you learn this as it changes over time? It’s now harder than ever for IT teams to enforce access decisions everywhere. But is the answer just denying your CEO, HVAC and app from working? Of course not. Yet “Zero Trust” essentially says to begin with an initial security posture that has no implicit trust between different entities, aka. default deny. If you’re a CISO, does zero trust clearly explain to other business execs why new security investments are needed?
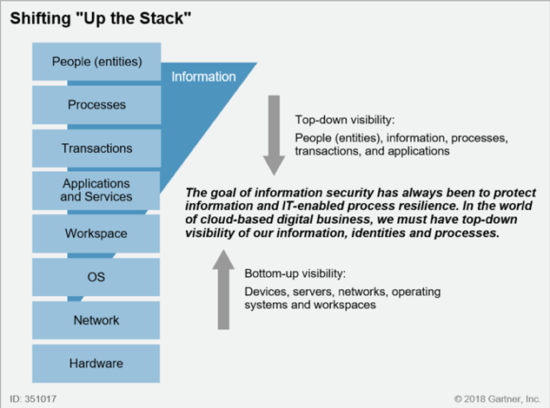
Shift to lean trust
Zero trust also says to “always verify”. So, we could verify the CEO’s identity. And we could assess her iPhone’s hygiene. Or we could check the compliance of the HVAC system’s profile. And we could baseline workloads’ communication behaviors. One could say that these verifications and assessments are rebuilding trust at a higher level of the IT stack. Not based on network IPs, but establishing user-device, IoT or workload trust. So, it does seem like “zero trust” is a misnamed term. Gartner’s CARTA (Continuous Adaptive Risk and Trust Assessment) framework argues that the goal is “lean trust”. MacDonald says to better enable new digital business, cloud and mobile initiatives that we need to continuously assess the combination of risk and trust throughout the duration of a network interaction and beyond the network to all infosec processes.
Be practical
Whether you tell your boardroom that you’re going to adopt zero trust or lean trust, you need to decide how and where to start your multi-year journey. Forrester’s Zero Trust eXtended concept includes every security technology—those designed to eliminate or establish trust as well as those to prevent or detect threats. So, it opens the flood gates to dozens of vendors positioning nearly every product to help you adopt zero trust. Cisco agrees that zero trust is a useful security concept but extending it to all aspects of security makes adopting the approach less practical and prescriptive. MacDonald instead recommends starting two specific projects in 2019—one granting more access protection for users and devices and another delivering more attack protection for workloads and apps. These projects are known as software-defined perimeters to let the good guys in and microsegmentation to keep the bad guys out, respectively.
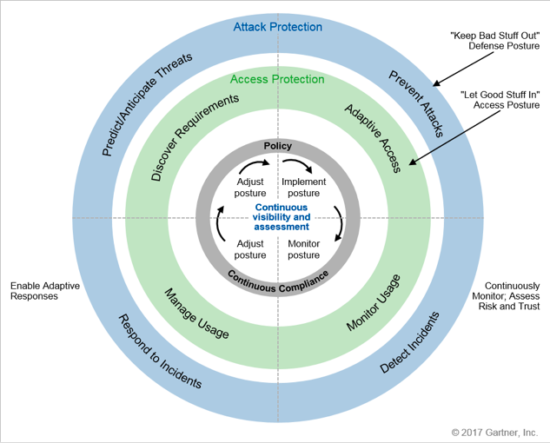
Maintain balance
In the CARTA framework, MacDonald splits his “Adaptive Security Architecture” (circa 2014) into two balanced access and attack protection approaches with four stages each. This aligns more closely with how Cisco recommends that customers complement the threat-centric security solutions (already deployed or being considered), such as NGFW and SIG, with newer trust-centric security solutions, such as MFA and SDP (see acronym definitions below). Across Cisco’s portfolio, we feel it’s more practical and prescriptive to focus on the subset of services and products that align to the app and network access-focused tenets of CARTA or Zero Trust. We call these trust-centric solutions Cisco Trusted Access. And Cisco is adding continuous verification capabilities across this portfolio to establish a CARTA-inspired “lean trust” level for users and their devices, headless IoT devices, and app workloads. Cisco’s integrated portfolio will ensure that dynamic context gained from your threat-centric solutions adapt trusted access based on your risk tolerance levels. Thereby, eliminating silos across your multi-domain security policy.
Start here
Cisco recommends trying Duo for free to get started on your zero trust journey with multi-factor authentication to achieve lean trust for users and their devices in just weeks. Then, using the same technology platform to implement a software-defined perimeter for app access in 2019.
Learn more
Gartner, Zero Trust Is an Initial Step on the Roadmap to CARTA, Neil MacDonald, 10 December 2018
Market acronyms
NGFW = Next-generation firewall
SIG = Secure internet gateway
MFA = Multi-factor authentication
SDP = Software-defined perimeter






Insightful, made me think. Look forward to the next one