Organizations these days face the daunting challenge of effectively prioritizing and responding to security risks and incidents. The combination of Cisco Secure Endpoint and Cisco Vulnerability Management form a powerful automated solution, enabling you to detect, prioritize and manage endpoint vulnerabilities, beginning with the most severe ones. There are two integrations available to help address critical aspects of security, both pre- and post-incident, which not only enhance incident response, but also fortify preventative measures.
Post-Incident: Accelerated Response with Risk-Based Context
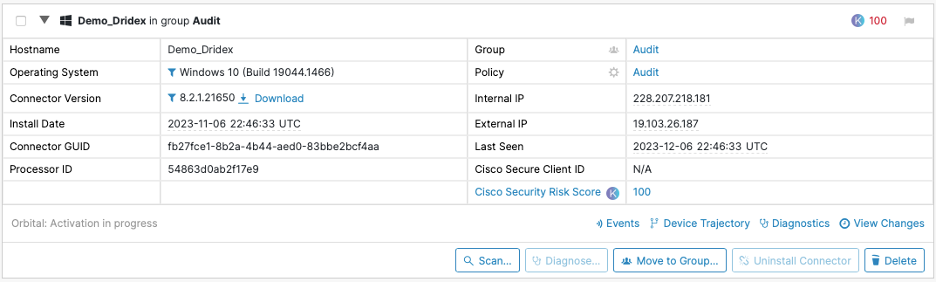
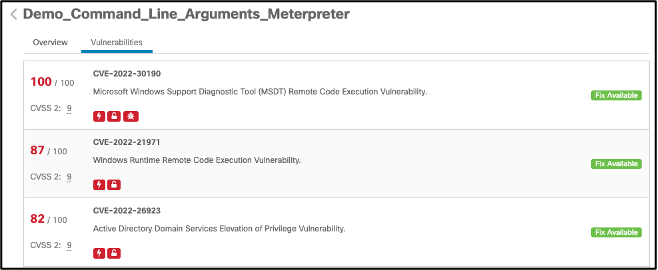
The first integration focuses on managing security incidents post-occurrence with risk-based context. At the heart of this integration is the Cisco Security Risk Score, powered by Cisco Vulnerability Management. It leverages the organization’s endpoint data and telemetry, enriched with vulnerability threat intelligence, and is analyzed through advanced data science algorithms like machine learning and predictive modeling. The outcome? A quantifiable, granular risk score for every vulnerability, aiding in prioritizing and addressing the most critical issues directly from the Secure Endpoint Console. The Cisco Security Risk Score is prominently displayed in the Secure Endpoint UI, providing scanner-less visibility into vulnerabilities in key operating systems.
Users of Cisco Secure Endpoint Advantage or Premier will automatically gain access to the Cisco Security Risk Score for each CVE on managed endpoints; allowing them to leverage real-world threat intelligence as part of their incident investigation. By integrating the Cisco Security Risk Score into the Secure Endpoint Console, SOC analysts will easily be able to identify the riskiest endpoints in their environment and drill down to understand the vulnerabilities that are driving that risk. Once the riskiest endpoints are identified, you’ll be able to accelerate your incident response by prioritizing action on the most critical vulnerabilities.
Pre-Incident: A Holistic Risk-Based Approach
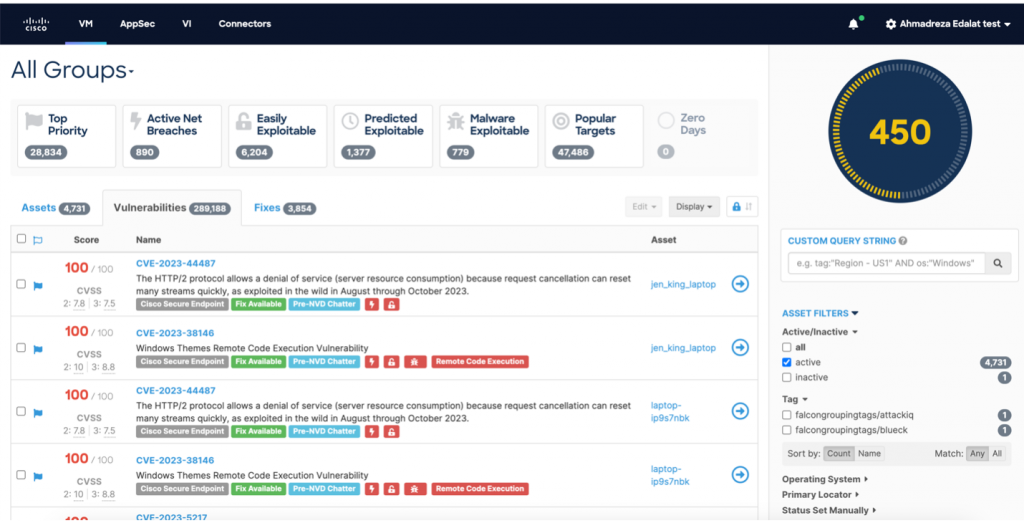
Moving to a more proactive stance, our new integration between Cisco Secure Endpoint and Cisco Vulnerability Management extends beyond a Security Operations use case to allow IT Operations and vulnerability management analysts to gain access to a risk-based vulnerability management platform. This integration allows users of both solutions to detect endpoint vulnerabilities and prioritize those posing the most risk for efficient remediation. With Cisco Secure Endpoint, users can hunt for hidden threats, detect stealthy malware, and perform advanced investigations with global threat intelligence from Cisco Talos. Cisco Vulnerability Management can then ingest the Cisco Secure Endpoint data, leveraging a dedicated data connector, and prioritize the vulnerabilities based on real-world attacker activity and business context. This allows organizations to significantly reduce their risk exposure without increasing their resource investment in remediation capacity.
The integration of these two solutions allows users to fully embrace a risk-based approach to endpoint vulnerability management. This integration unlocks several key use cases such as:
- Detecting and understanding vulnerabilities on endpoints,
- Centralizing vulnerability data from Cisco Secure Endpoint and other security data sources through 50+ available data connectors,
- Prioritizing vulnerabilities based on exploitation risk and asset context,
- Implementing remediation workflows and enabling IT to self-serve to efficiently reduce risk,
- Measuring and reporting on risk posture, industry benchmarks, and progress made.
- Remediation Analytics & Scoring, Zero-Day intelligence powered by Cisco Talos, and Vulnerability Intelligence API and UI with the Cisco Vulnerability Management Premier tier
The integration of these two solutions takes vulnerability management to a new level, providing a comprehensive, risk-based approach to cybersecurity.
See It in Action
The integration of Cisco Secure Endpoint and Cisco Vulnerability Management is more than just a solution on paper – it’s a practical, real-world tool that can enhance your cybersecurity measures. Don’t just take our word for it, see it for yourself. We’ve created a recorded demo showcasing the combined power of these two products.
To learn more about how Cisco Vulnerability Management can enhance your organization’s cybersecurity efforts, visit https://www.cisco.com/site/us/en/products/security/vulnerability-management/index.html
We’d love to hear what you think. Ask a Question, Comment Below, and Stay Connected with Cisco Security on social!
Cisco Security Social Channels





