Cisco Secure Firewall is an exceptionally robust firewall solution with innovative features such as Snort IPS, URL filtering, and malware defense. This comprehensive offering simplifies threat protection by enforcing consistent security policies across physical, private and public cloud environments.
Furthermore, it grants extensive visibility into your network infrastructure, swiftly identifying the origin and activity of potential threats. Armed with this knowledge, you can promptly stop attacks before they disrupt your operations.
In addition to traditional firewall capabilities, it provides features as:
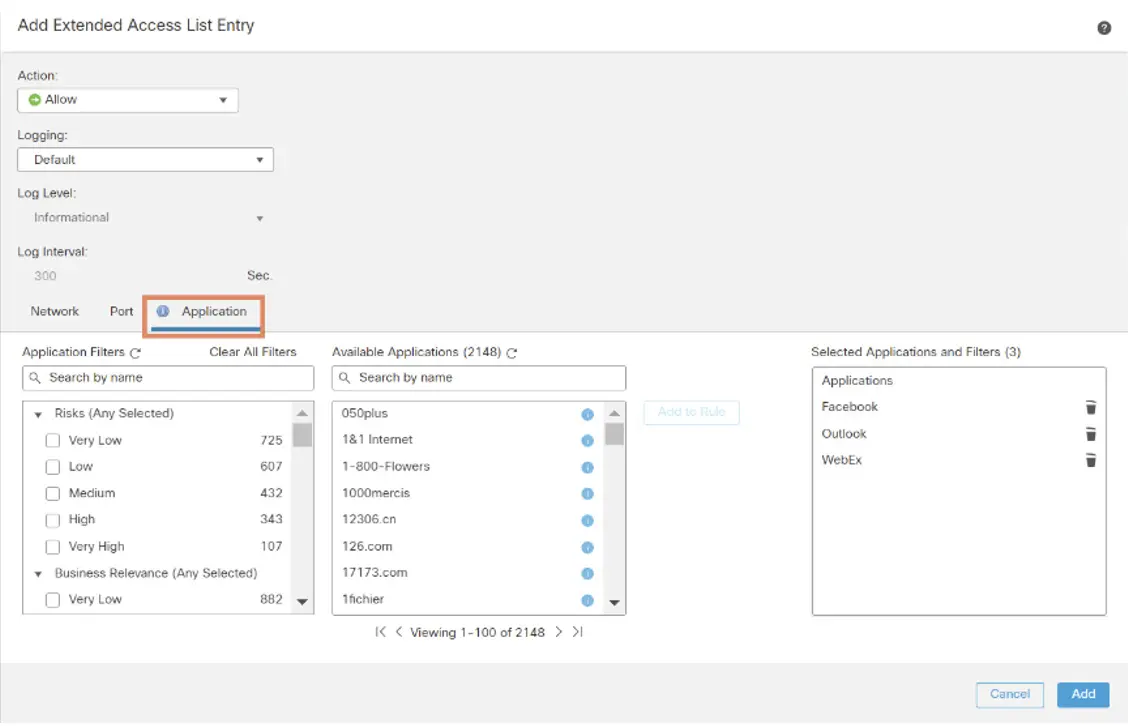
- Application visibility and control
- User identity awareness and control
- Intrusion prevention and intrusion detection
- SSL/TLS decryption
- Reputation based blocking
- File and malware protection
- Virtual Private Network (VPN)
To further secure network deployments, Cisco Secure Firewall provides additional security capabilities in its later releases such as:
- Encrypted Visibility Engine (EVE) that enhances encrypted traffic inspection without the need to implement full main-in-the-middle (MITM) decryption.
- Elephant Flow Detection to detect and remediate elephant flows (flows that are typically larger than 1 GB/10 seconds) and avoid high CPU utilization and packet drops.
- Cisco Secure Dynamic Attribute Connector (CSDAC) that brings agility and intelligence into your security policy management by leveraging tags and labels for policy configuration rather than traditional IP/network-based policy configuration.
Firewall in a branch?
For many, the question is whether a firewall is needed at the branch location? What am I protecting? Remember, security is only as strong as your weakest link. When we talk about security, we are securing users, applications, and data. Aren’t all three in a branch?
Polymorphic, multi-vector attacks target branches and move laterally into the organizational network.
Branches are places where you expect customers to spend time, like banks, car showrooms, coffee shops, etc. Branches are where contractors, vendors, guests, customers and your own staff — including the Administrator — can visit with the least privileges. Branches are usually the less secured locations, allowing threat actors to penetrate. So, it is imperative that we look at a branch from the same business objective as the most important asset.
This begs the question of connecting the branches to corporate networks securely. Think of how complex it is when deploying multiple devices, one for connectivity and another for security. You would want to get connectivity and security with minimal effort and preferably on a single platform.
That’s where, Cisco Firewall comes in. With its robust firewall capabilities, now we have added simplified and secure WAN capabilities into the platform.
Overview of SD-WAN capabilities
As organizations expand their operations across multiple branch locations, ensuring secure and streamlined connectivity becomes paramount. Deploying a secure branch network infrastructure involves complex configuration and management processes, which can be time-consuming and prone to security vulnerabilities if not handled properly. However, organizations can overcome these challenges by leveraging a secure firewall solution for simplified and secure branch deployment.
The idea is to simplify secure branch deployment using a robust firewall solution. By integrating a secure firewall as a foundational component of the branch network architecture, organizations can establish a strong security baseline while simplifying the deployment process. This approach enables organizations to enforce unified security policies, optimize traffic routing and ensure resilient connectivity.
Some of the SD-WAN capabilities supported on the Cisco Secure Firewall are:
Zero-Touch Provisioning
Imagine what you go through during the initial setup of a device. Sometimes, you must pre-configure the device in an office and send it to sites for deployment. Other times, you must send a skilled engineer to bring the device up in the field. Both these options mean an additional step before you bring up the device, adding more time. This could delay deployments by a few days. Multiply that with the number of devices. Phew! Cumbersome and time consuming, isn’t it?
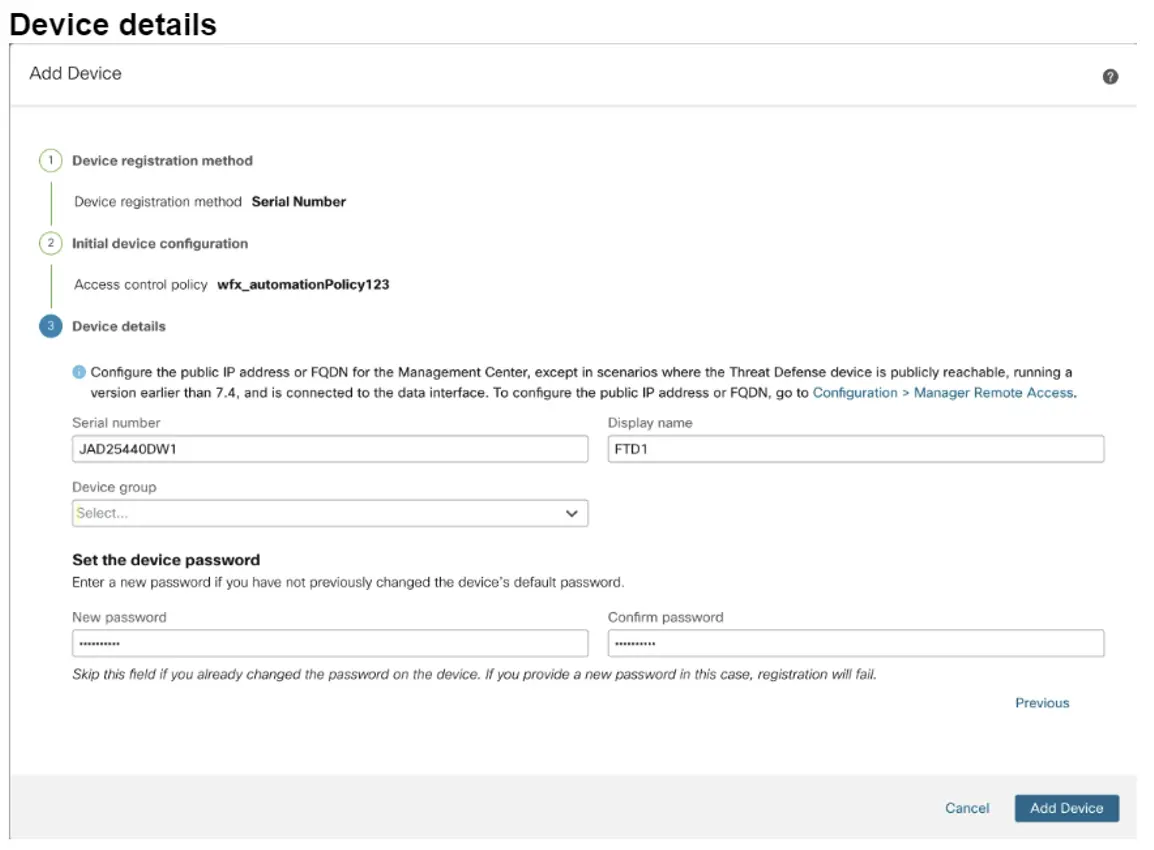
Zero-Touch Provisioning lets you register devices to the management center by serial number without having to perform any initial setup on the device. All you must do is add the serial numbers in the Management center. When the device is plugged and powered on, it contacts the cloud onboarding, and the management center claims the device. The management center integrates with the Cisco Security Cloud and Cisco Defense Orchestrator (CDO) for this functionality.
Pre-provisioning using Device Templates
Device templates enable deployment of multiple branch devices with pre-provisioned initial device configurations. Added with zero-touch provisioning, you can now apply configuration in bulk to multiple devices, apply configuration changes to multiple devices with different interface configurations during bring up. In addition, you can also clone configuration parameters from existing devices.
Imagine, you have added devices in the management center using serial numbers and have assigned a template for branch devices and — Bingo! — the device is up and running with the configurations you need, all in a few clicks.
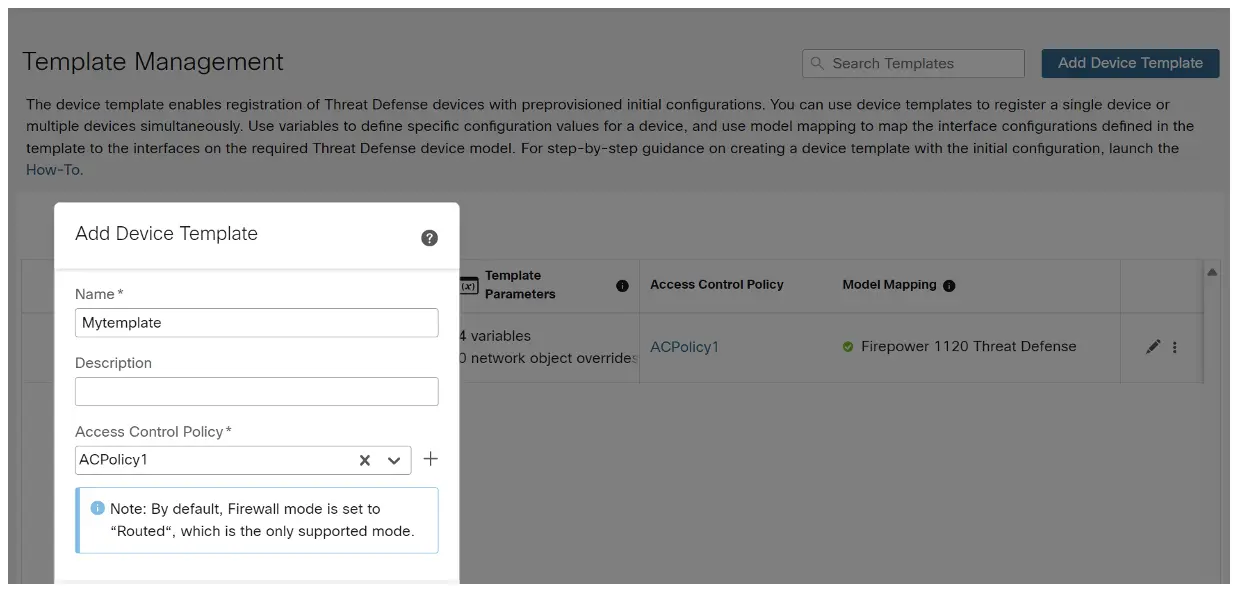
More details about the templates could be found here: Zero touch provisioning with Cisco Firewall Management Center Templates – Cisco Blogs.
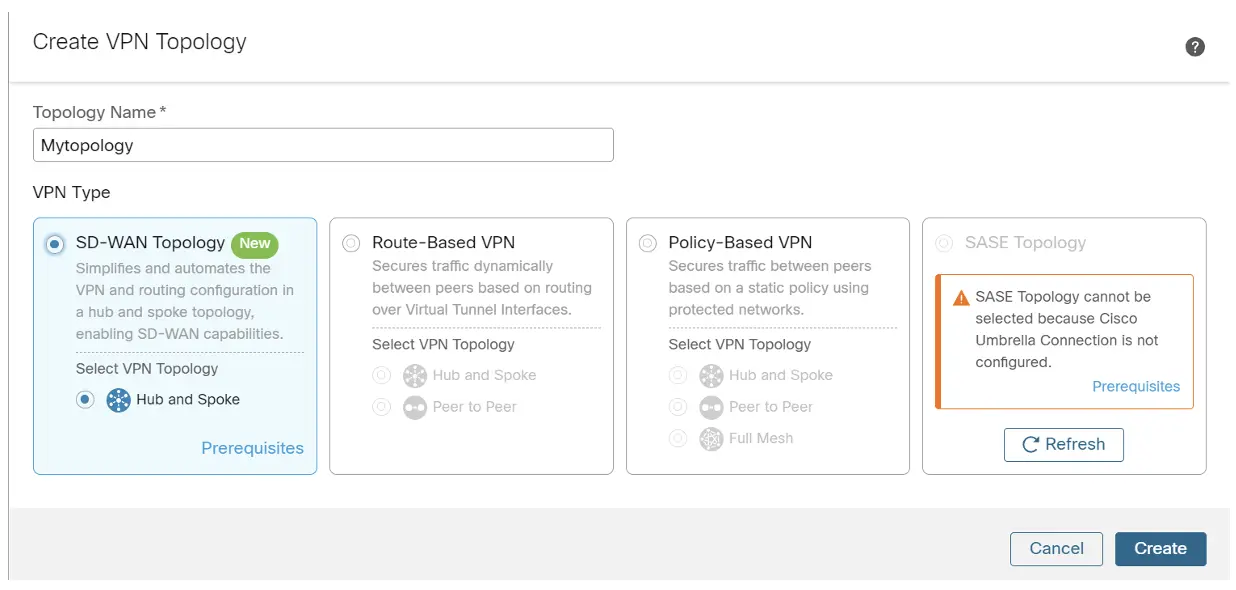
SD-WAN Wizard
Imagine configuring tunnels, setting up hubs and spokes, adding interface and routing parameters to allow branches to connect to each other. Sounds complex and time consuming, doesn’t it?
Not really. The Firewall Management Center allows you to easily configure VPN tunnels between your centralized headquarters (hubs) and remote branch sites (spokes) using the new SD-WAN wizard in a few clicks.
Why the wizard?
- Simplifies and automates the VPN and routing configuration of your SD-WAN overlay network
- Requires minimal user input
- Easily adds multiple branches at a time
- Provides easy dual ISP configurations
- Enables network scaling
Application based routing for best path decisions
Now that you have set up your WAN connectivity, the next step in the process is to avail yourself of the benefits of SD-WAN. Create and apply policies to let your device steer the applications using relevant metrics like delay, Jitter, Loss and MOS.
For example, your voice applications might be sensitive to Jitter. Video applications might be sensitive to delays, etc.
Depending on the application, you can now create a policy that is relevant based on metrics applicable for the traffic. Metrics are determined using HTTP every 30 seconds.
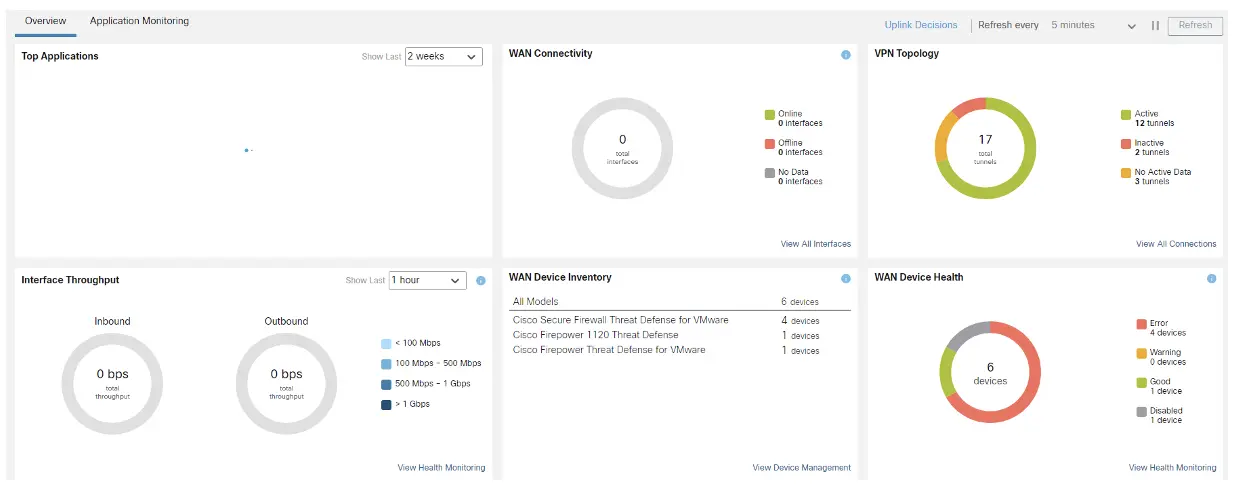
The SD-WAN Summary Dashboard
Now that you have devices up and running, all you need to do is watch the dashboard to monitor devices, WAN, and applications. This Dashboard gives a view of top applications running on your branch, any WAN connectivity issues, device issues or interface issues.
Conclusion
With a focus on tighter integration of Networking and security as well as simpler consumption and operation, Cisco Firewall helps customers save CAPEX and OPEX with a single user interface and operating system on a single platform.
References
We’d love to hear what you think. Ask a Question, Comment Below, and Stay Connected with Cisco Secure on social!
Cisco Security Social Channels





