Brute force attacks have existed long before the Internet. As a cryptanalytic attack, it started being used as an attempt to access encrypted data when there were no other options available. With the rise of the Internet, this type of attack was quickly adopted. In a nutshell, a brute force attack consists of systematically trying different credentials until the correct combination is found. It’s like trying to open a combination lock by going through all possible combinations: eventually, it will pop open.
The main disadvantage of brute force attacks is that they usually take a long time. Also, attempting every user name and password combination against a certain system is now easy to detect. A variant of this method, known as dictionary attack, is able to increase the speed considerably. Instead of systematically trying every possible user name and password combination, dictionary attacks only try those combinations that are more likely to succeed. This type of attack usually relies on known lists of commonly used user names and passwords.
Cybercriminals are constantly looking for cheap, disposable infrastructure to host malware, transient command-and-control servers, or temporary resources for their activities. Distributed brute force attacks are one of their cheapest options: the attack is simple and still works. In this blog post, we explain how content management systems (CMS) are widely targeted, how malware uses brute force attacks against them, and how it’s possible to detect them using behavioral analytics.
WordPress is the most popular target
Brute force attacks are common against web services. Any website is a potential target. However, criminal actors usually choose the most popular to increase their chances of success. WordPress is one of their favorite targets. WordPress is a CMS used to create websites. It’s easy to set up, is built on open source, and provides a simple way of managing the content and look of the website. This platform is so popular that out of one million top websites on the Internet, over 75% are created using WordPress. Being such a strong market leader makes WordPress an attractive target for attackers. One popular type of attack is password brute force.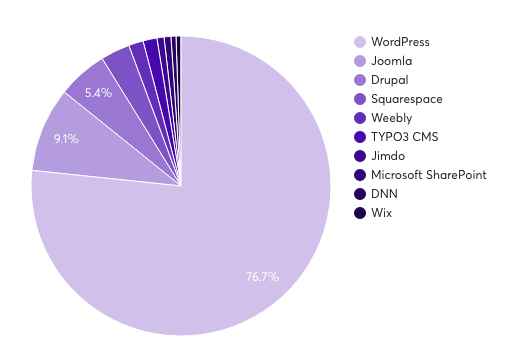
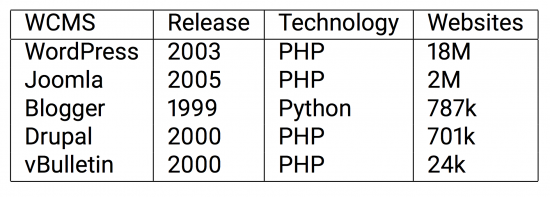
Figure 1: WordPress shares over 76% of the market. More than 18M websites on the Internet use WordPress.
The goal of this attack is to obtain valid credentials for the WordPress site and use them to access the admin panel. Access to the admin panel means that the attacker gains complete control over the website. Compromised WordPress sites can be used for different purposes: deface, steal credentials, host malicious files, inject malicious code to the pages, or make the website part of a specific malware infrastructure. For example, the Angler Exploit Kit, which was the biggest exploit kit on the market last year, used compromised WordPress websites to infect visitors with malware. We described the case of a hijacked WordPress website being a part of an Angler infrastructure in a previous blog.
Nowadays, malicious actors use their botnets to perform distributed brute force attacks against the CMS. In this scenario, every infected computer forms part of the attack. There are two types of brute force attacks that can take place. We refer to them as vertical and horizontal brute force attacks.
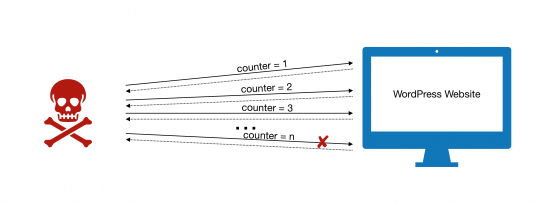
In the vertical brute force attack, every bot attempts a full dictionary attack against a single website. This type of brute forcing can be easily detected and blocked using a simple counter for user login attempts. This attack is illustrated in Figures 2.1 and 2.2.
Figure 2.1 – In a standard brute force attack, an infected user systematically tries different user name and password combinations. Simple methods can easily detect this attack by counting the number of attempts and block users after a certain number of attempts is reached.
Figure 2.2 – In a distributed and vertical brute force attack, each infected user targets a specific website and systematically tries every credential provided by the bot master. The detection of this attack is the same as explained in Figure 2.1.
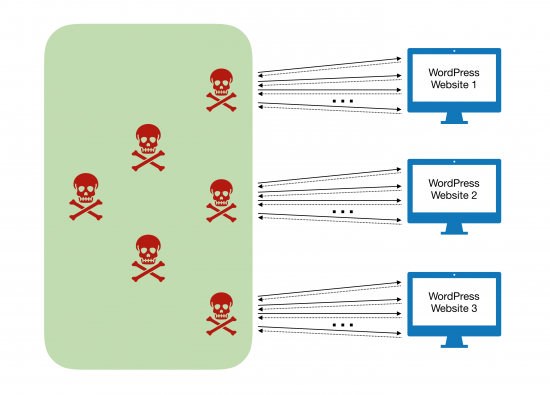
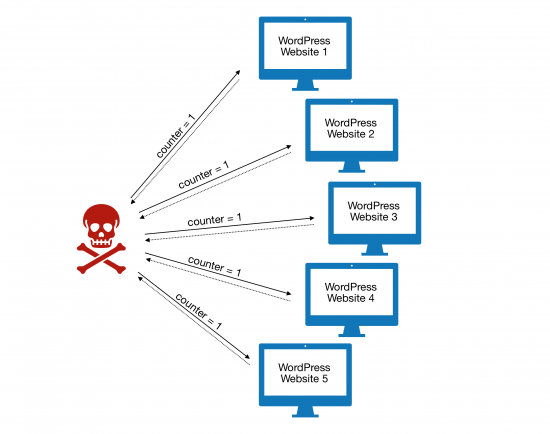
In the horizontal brute force attack, the bot master handles the dictionary used for the attack. Each bot receives a small subset of it, attempting a few user name and password combinations against a single website. From the victim perspective, it receives a few attempts by different hosts. No single bot exceeds the maximum number of login attempts, so triggers no alarm. This type of brute force attack is harder to detect and mitigate. This attack is illustrated in Figures 3.1 and 3.2.
Figure 3.1 – In a horizontal brute force attack, an infected host attempts a single user name and password combination per WordPress website. This makes detection much harder as simple counters do not trigger an alarm in this scenario.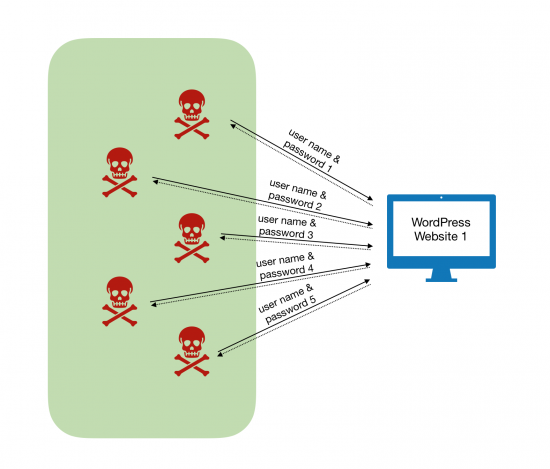
Figure 3.2 – In a distributed and horizontal brute force attack, every infected host tries a different user name and password combination. All the individual bots, coordinated by the bot master, cover the full dictionary attack together.
Brute force attacks that originate from a company network can have negative repercussions; they could damage reputation of the company network or cause the company to be blacklisted due to the malicious activity. An endpoint infected with this type of malware is likely to also be infected by other more severe threats. This type of infection should be quickly contained and mitigated.
Brute Force Attacks Still Work
While WordPress is the most targeted platform, it’s not the only one. Joomla, Blogger, and Drupal are other CMS platforms that have also been targeted by malicious actors in the past. Attackers continue to rely on these methods, and the reason is simple: brute force attacks still work.
Figure 4: Summary of Web Content Management Systems (WCMS) by popularity
The past decade has seen quite a number of different botnets performing different types of brute force attacks. The two more prominent botnets are Mayhem and Sathurbot. Mayhem was first reported in 2014 by researchers working under the handle of MalwareMustDie. Sathurbot, a modular botnet, first appeared in 2013 and there have been several versions since then. Both threats are still active today, years after they first appeared.
Brute Force Detection Using Behavioral Analytics
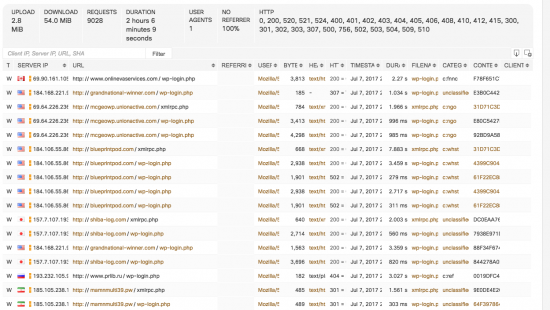
Cisco Cognitive Threat Analytics is able to detect both types of WordPress distributed brute force attacks. As explained in our previous blog, Cognitive Threat Analytics works with HTTP/S proxy logs. To detect these types of attacks, we create a model for each user which reflects his activities on different websites. The behavioral patterns of a normal user are different from a user infected with malware. Most importantly, an ordinary user makes only a limited number of login requests to WordPress sites, if any. When a user gets infected with a malware such as Mayhem or Sathurbot, the infected computer automatically generates a huge number of WordPress login requests as part of the ongoing brute force attack. Our models reflect that. Cognitive Threat Analytics is also able to detect horizontal brute force attacks by modeling user behavior across different websites.
Figure 5 shows a real user performing a brute force attack as observed by Cognitive Threat Analytics. You can see that the attack lasted for two hours, making 9,028 WordPress login requests. You can also see that the malware performs on average three login attempts per website before moving on to the next website. This is a clear example of a distributed and horizontal brute force attack.
Figure 5: Horizontal brute force attack by an infected user as observed by Cognitive Threat Analytics.
Conclusion
Brute force attacks are a simple type of attack on different systems and web sites. They’ve existed for a long time and are still effective and widely used today. The attack is easy to implement and many tools are available to brute force attack different systems and services. Popular targets for attackers include WordPress and other CMS websites. WordPress is the most popular target due to the high number of websites on the Internet using this platform. Cisco Cognitive Threat Analytics is able to detect distributed WordPress brute force attacks by creating a user behavioral model from HTTP/S proxy logs.
An overview of the CMS brute forcing landscape was presented by Cognitive Threat Analytics researchers at the 9th edition of the BruCon Security Conference. The talk includes a historical overview of different malware families performing brute force attacks and an in-depth analysis on the Sathurbot botnet. A video of the talk is available below.