Post authored by Martin Rehak, Veronica Valeros, Martin Grill and Ivan Nikolaev.
In order to complement the comprehensive information about the Angler exploit kit from our Talos colleagues [Talos Intel: Angler Exposed], let’s have a very brief look at what an Angler and CryptoWall infection looks like from the network perspective. We will present one of the recent Angler incidents discovered by Cognitive Threat Analytics (CTA).
Cognitive Threat Analytics works after the attack. It sifts through the logs produced by the client’s web proxy for any malware that may have slipped through the perimeter defences, such as this specific case here. CTA was able to observe the attack in its entirety (including the phases where the perimeter defence successfully blocked several stages in the attacker’s plan) and notify the security team immediately for follow-up and investigation.
So, how does an incident start for the analyst?
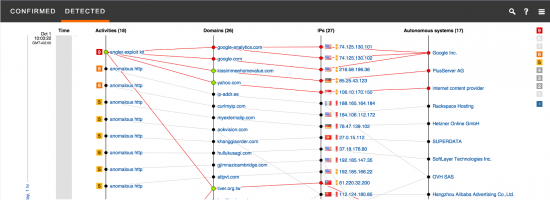
We can see that the incident has been categorised as an Exploit Kit infection. The system asserts 95% confidence in this incident being a true positive, and classifies it on the level 8 (out of 10) on the risk scale.
An analyst would then investigate the incident in detail, in order to confirm the sequence of events and the type of infection. We will emulate the analyst and walk through the incident information in the CTA UI. This will help us to reconstruct the events leading to this compromise and subsequent malware actions.
The communication related to the exploit kit itself is quite simple. The domains concerned are: liver.org.tw, yahoo.com and kissimmeehomevalue.com. Google and Google Analytics sites are usually part of the side traffic triggered by other domains, so we can safely disregard them in this analysis. We can visually imagine the sequence of events by just looking at the information initially provided, but let’s go over the infection in detail.
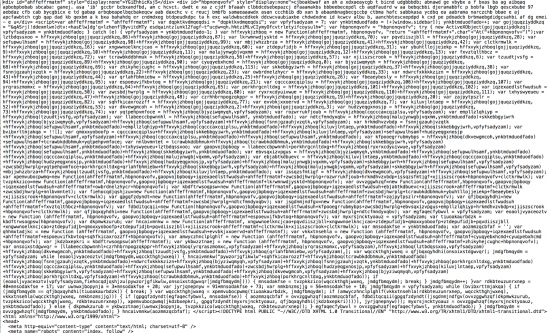
At the very beginning, the victim visited the page liver.org[.]tw, after a yahoo search. The website, seemingly legitimate, was compromised to inject a malicious javascript leading to the exploit kit as we can see below:
This piece of obfuscated javascript redirected the user to another site:
hxxp://kinderbeskerming.kissimmeehomevalue[.]com
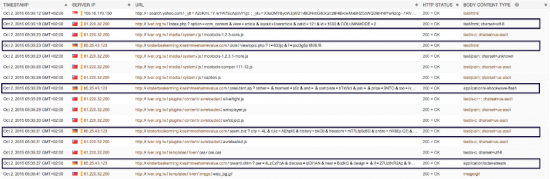
This site delivered a flash exploit in order to compromise the browser. Within nine seconds of the initial download, the malware has successfully exploited the host and connected back to the same server to download additional 220 kilobytes of obfuscated binary content. Once in place, it moved forward with the plan.
In this example, and very consistently with the Talos report, Angler has been used to deliver ransomware. Analysis of the traffic generated right after the exploit points to Cryptowall version 3 as a culprit.
The first step involved checking the IP address of the infected host. Malware tried three times, with three different servers. All three attempts were successfully blocked by the web proxy as highly suspicious.
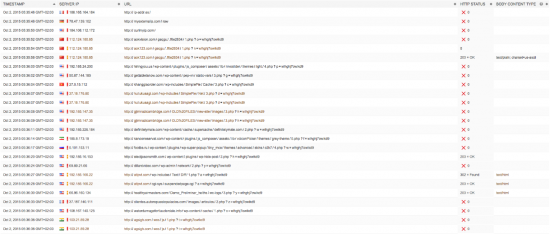
Then, the malware attempted to contact several other servers, mostly spread across China and the US. This behavior was highly indicative of a Cryptowall infection, and again consistent with Talos findings. Most of the requests were effectively blocked, but three of them managed to get through and resulted in successful connections. Another interesting fact that we can observe is that most of the servers were WordPress based and that there was no legitimate reason for the connections to them. This has been one of the factors facilitating the discovery and analysis of the behaviour by CTA. Also, we can notice that the HTTP requests going to seemingly unrelated sites show a strange consistence in their parameter values, where one of the parameters is identical for all the requests.
The whole infection took 34 seconds between the first click on the search result and the (partially) successful establishment of communication with command and control infrastructure.
What is the moral of this story? Despite our best efforts, the sheer number, resilience and variability of the attacks virtually ensure that at least some attacks will get through. Then, the defense-in-depth technologies like Cognitive Threat Analytics and Advanced Malware Protection (AMP) remain the best chance how to discover the breach and mitigate its consequences.
IOCs
List of domains contacted by Cryptowall in this infection:
agsigh.com
aok123.com
aokvision.com
atlpvt.com
clientes.autorepuestopalacios.com
definitelymale.com
dillardvideo.com
electjasonsmith.com
footbe.ru
gettabletsnow.com
gjimnazicambridge.com
healthyairmasters.com
hiringyou.us
hullukusagi.com
kanooneservat.com
khanggiaorder.com
waterdamagefortlauderdale.info
References
Threat Spotlight: Angler Exposed | Talos
Angler Exploit Kit – New Variants | Talos
Threat Spotlight: Angler Lurking in the Domain Shadows | Talos
Angler EK: More Obfuscation, Fake Extensions, and Other Nonsense | Talos
A closer look at the Angler exploit kit | Sophos Blog