In a previous post, I dove into some survey results to explain why segmentation has evolved into a foundational concept for network security. Specifically, I discussed how a dual segmentation approach—deploying both macro- and micro-segmentation—helps organizations enhance their network security.
But implementing this dual approach isn’t simple. There’s no “box” or single product that one can purchase. Nor is there a single approach that can be modeled as a best practice for every use case. Instead, organizations are having to rely on multiple segmentation methods. Unfortunately, this lack of clarity can add complexity to an already complex situation. The result? Many, too many, segmentation projects fail.
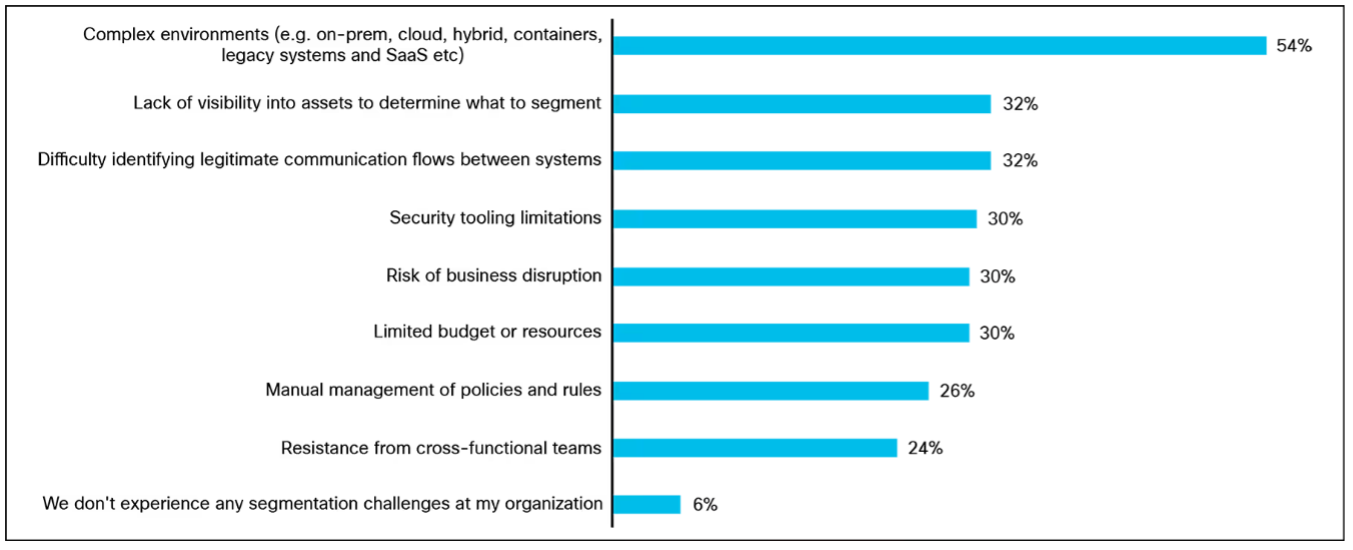
The data backs this up. According to our survey results, 94% of organizations are currently facing segmentation challenges, which range from technical to non-technical issues. Let’s dig deeper into the rest of the report to understand why organizations are facing these challenges and how they can mitigate their impact.
Challenges Inhibiting Segmentation Projects
Understanding the challenges organizations face will ease the transition from partial to comprehensive segmentation implementations, allowing organizations to accelerate their progress through their segmentation journeys. Unfortunately, this sense of frustration has become an epidemic. In addition to the 94% of survey respondents who report facing challenges, 87% of respondents indicate that their segmentation process requires improvement. The most common challenges holding them up include the complexity of their environments, a lack of visibility into these environments, and a failure to gain context into communication workflows between systems.
1. Complex Environments
According to the report, the main challenge impeding segmentation projects is the complexity resulting from the combination of hybrid IT, cloud, containers, and legacy systems (54%). Managing against this complexity requires organizations to follow a common framework to create network segmentation areas, then focus their time and resources on finding solutions for edge use cases. Obviously, it is essential to deploy network security technologies that span all these environments (on-premises, cloud, hybrid cloud, containers, SaaS, etc.) to get to a fully segmented environment.
2. Lack of Asset Visibility
The second main challenge is the lack of visibility into network assets (32%). And this makes sense. You can’t secure what you don’t know about. While some portion of this challenge stems from the complexity of the environment, a significant portion can also be attributed to the complexity of large organizations, where people, processes, and technology are constantly changing. For example, the purpose of a homegrown application in the data center may have been perfectly obvious to the IT organization a few years ago. Still, after organizational changes and the introduction of shiny new applications, organizational memory has likely dwindled to the point where securing the application risks disrupting business workflows.
3. Lack of Insight Into Communication Flows
A limited understanding of how disparate users, devices, applications, and services connect and interact with each other makes it difficult to create, apply, and enforce segmentation policies. In fact, the third most pressing challenge is difficulty identifying legitimate communication flows between systems (32%). Organizations need context that goes beyond just IP addresses. Behavior needs to be tied to identity (whether they are an actual person, device, or workload). Having a better understanding of user and workload behaviors enables organizations to create rulesets that allow or disallow specific actions and behaviors. This enables security systems to, for example, determine that an attempt by an HR workload to connect to the open Internet is not normal behavior, should be marked as suspicious, and blocked to prevent data exfiltration.
Overcoming Segmentation Challenges Enables a Proactive Security Strategy
Segmentation remains a foundational element of enterprise security. Still, many organizations have yet to fully implement both macro- and micro-segmentation due to a series of challenges, including an increasingly complex IT environment, a lack of visibility into individual workloads, and a lack of context for distinguishing between normal and abnormal behaviors. These blockers need to be addressed if organizations want to implement a proactive security strategy.
In our next blog, I’ll outline what the survey results reveal about the benefits organizations achieve when their segmentation projects succeed. In the meantime, download the 2025 Cisco Segmentation Report to better understand the state of segmentation today.
We’d love to hear what you think! Ask a question and stay connected with Cisco Security on social media.
Cisco Security Social Media





