Defenders face two significant challenges in today’s complex threat landscape. First, the number and variety of malware types and families are increasing—so much so that automation of detection and response efforts is now a must. Second, the volume of encrypted web traffic—both legitimate and malicious—is expanding exponentially.
Encryption is meant to enhance security. However, as explained in the Cisco 2018 Annual Cybersecurity Report, it also provides adversaries with a powerful tool to conceal their command-and-control (C2) activity, affording them more time to operate and inflict damage.
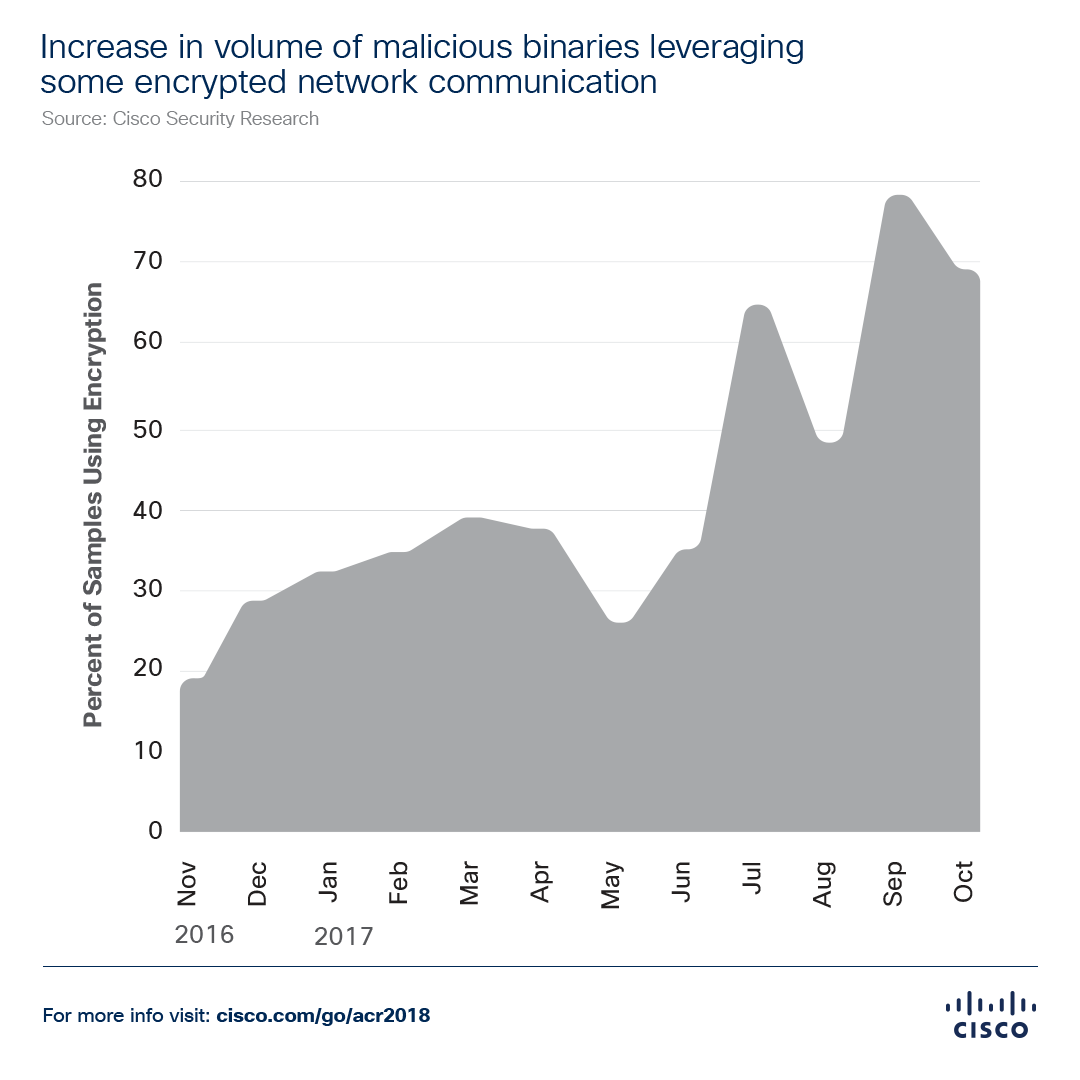
Consider these findings, presented in our new report: Over a 12-month period beginning in November 2016, Cisco threat researchers observed a more than threefold increase in encrypted network communication used by inspected malware samples (see below). And our analysis of more than 400,000 malicious binaries found that about 70 percent had used at least some encryption as of October 2017.
Advanced capabilities help level the playing field with adversaries
As adversaries widen their embrace of TLS, Tor, and other encrypted protocols, we see another more positive trend: Enterprises turning to capabilities like machine learning and artificial intelligence to enhance their network security defenses. In fact, findings from the 2018 Security Capabilities Benchmark Study, which are featured in our latest cybersecurity report, show that 34 percent of defenders are completely reliant on machine learning and 32 percent are completely reliant on artificial intelligence.
At Cisco, we see the use of machine-learning and artificial intelligence technologies as a way to level the playing field with adversaries who have been innovating for years and are becoming only more adept at obfuscation.
Balance is the key to delivering the right response
Machine-learning and artificial intelligence solutions can, over time, “learn” how to automatically detect unusual patterns in network traffic that might indicate malicious activity. They help defenders improve threat prevention and detection by allowing them to:
- Discover correlations that human security teams can’t see or interpret on their own
- Reduce the complexity of big data analysis
- Reduce the time to discovery and remediation of threats
- Gather contextual evidence to explain why activity may be malicious
One of the most valuable aspects of machine learning, especially in monitoring encrypted web and other network traffic, is its ability to detect variations of known threats, malware subfamilies, or related new threats, as well as net-new malware.
That’s critical in today’s threat landscape, where adversaries are constantly evolving malware and taking it to new levels of sophistication and impact. As explained in the Cisco 2018 Annual Cybersecurity Report, one reason defenders struggle to understand what’s happening in the threat landscape is the sheer volume of potentially malicious traffic they face. Our researchers report that Cisco security products saw an elevenfold increase in overall malware volume just during the period from January 2016 to October 2017.
Use of advanced technologies like machine learning and artificial intelligence can also help security teams overcome skills and resource gaps — a common problem for organizations around the globe due to the current cybersecurity talent gap. Through automation, defenders can also better manage the scale of threats as the security perimeter continues to dissolve due to the cloud and the expanding Internet of Things (IoT). The Cisco 2018 Annual Cybersecurity Report notes that many security teams are already struggling to defend both IoT and cloud environments, and many organizations lack awareness about the number of IP-enabled IoT devices connected to the network.
It is an art and a science to understand what activity is “normal” in a given network environment and deliver an appropriate response to known and potential threats. Ultimately, an effective machine-learning architecture should have the right balance of “supervised” and “unsupervised” learning methods to detect new threats in encrypted communication channels, while maintaining a high level of accuracy and presenting findings prioritized for fast incident response. In simpler scenarios, the response may be fully automated. In more complex situations, the response may involve escalation and further correlation.
To better understand the value of machine-learning and artificial intelligence capabilities in network security, and which threat detection techniques are best-suited to certain threat types, take a look at the detailed taxonomy provided in the Cisco 2018 Annual Cybersecurity Report, available here.






It is so difficult to keep up with the cyber crooks and malicious fiends who want to destroy or exploit. Staying ahead isn't easy. Thanks for working diligently to keep businesses and individuals safer.
Roxanne, thank you. There is another more detailed write-up on the Encrypted Traffic Analytics capability, if you are interested: https://blogs.cisco.com/security/securing-encrypted-traffic-on-worldwide-scale.