Today’s threat landscape is completely different than last year; and next years will be, not surprisingly, even worse. The Industrialization of Hacking has spawned a new era of professional, entrepreneurial, and resourceful cyber criminals. In recent year’s dynamic malware analysis (aka sandboxing) has become the shiny new technology that we all want, no, need to have. At one time anti-virus held this position as well, and the same will eventually be said of sandbox technology used to fight advanced malware.
You may have purchased a sandbox a few years ago but it’s likely that your malware analysis needs have gone beyond the traditional sandboxing technologies that simply extract suspicious samples, analyze in a local virtual machine, and quarantine. You need a more robust malware analysis tool that fits into your infrastructure and can continuously detect even the most advanced threats that are environmentally aware and can evade detection.
Tripwire recently partnered with Cisco and integrated the AMP Threat Grid dynamic malware analysis solutions into Tripwire Enterprise. But why choose this dynamic malware analysis tool? After careful evaluation there were a few key reasons to integrate this tool versus others:
-
It’s not just dynamic malware analysis
AMP Threat Grid provides both static and dynamic malware analysis, and a full subscription provides an API that is used to seamlessly deliver context rich threat intelligence into existing security technologies.
-
Not everyone out there is a security expert
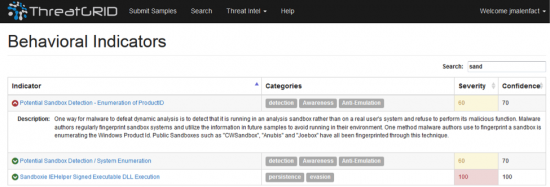
Heck, very few are. AMP Threat Grid was designed to empower junior security analysts by providing a Threat Score so they can easily determine how malicious a sample is. The behavioral indicators are written in plain English so they can understand what the file is doing, and why its behavior is malicious, suspicious, or benign.

-
Lack of instrumentation
AMP Threat Grid was designed without any instrumentation inside the virtual machine. Most experts agree that around 40% of today’s malware is environment aware, checking to see if it is running in a sandbox or the age of the operating system before detonating.
There are 3 ways that most people deploy a malware analysis tool:
- A stand-alone solution designed to feed itself samples for analysis without dependency on other security products. This has the most flexibility in deployment but adds significant hardware costs and complexity to management and analysis, especially for distributed enterprises.
- A distributed feeding sensor approach, such as firewalls, IPS, or UTMs with built-in sandboxing capabilities. These solutions are usually cost effective and easy to deploy but are less effective in detecting a broad range of suspicious files including web files. They can also introduce bandwidth limitations that can hamper network performance and privacy concerns when a cloud-based solution is the only option.
- Built into secure content gateways, such as web or email gateways. This approach is also cost effective but focuses on web and email channels only and also introduces performance limitations and privacy concerns.
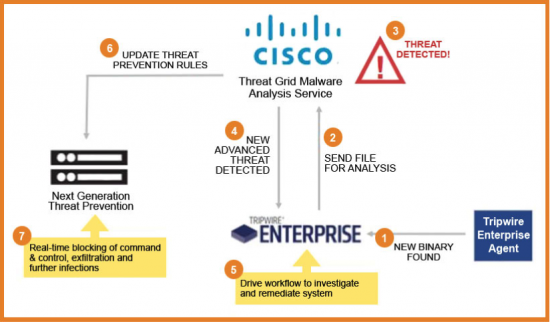
Since Tripwire is already monitoring and collecting the data on your mission critical systems, these approaches don’t seem to work. But there’s a fourth way that actually takes the best of what these approaches offer and raises the bar to help you fight well-funded attackers that get better at what they do every day: Cisco AMP Threat Grid. Through AMP Threat Grid, Cisco offers advanced malware analysis and intelligence that delivers integration directly with Tripwire Enterprise providing you with a better ROI and more visibility into what is happening in your environment. Tripwire has integrated AMP Threat Grid into their Tripwire Enterprise, providing both static and dynamic analysis so you can better understand the malware targeting your organization, as well as the ability to automate the consumption of threat intelligence into your existing security infrastructure.
How does the Integration actually work?
AMP Threat Grid’s content driven security analytics dynamically and statically analyzes all submitted files, executing the sample in a safe environment, examining the behavior of the samples, and correlating the results with hundreds of millions of other analyzed malware artifacts. In less than 10 minutes AMP Threat Grid reports back and Tripwire Enterprise tags the file with the result. This enables Tripwire Enterprise customers to prioritize actions for changes on systems with threats identified by AMP Threat Grid and initiate workflow actions for quick remediation.
Not only does AMP Threat Grid analyze a broad range of objects, but those interested in an AMP Threat Grid subscription will also be provided with deep analytics capabilities wrapped with robust context. With over 350 behavioral indicators and a malware knowledge base sourced from around the globe, AMP Threat Grid provides more accurate, context rich analytics into malware than ever before. Tripwire customers can register for their free demo here.






Grid reports back and Tripwire Enterprise tags the file with the result. okey.