One important lesson the pandemic taught us is that enterprises need a network infrastructure to support a hybrid workforce with a distributed application landscape. In a hybrid workplace environment, people need to be able to work fluidly from remote home offices as well as from established branch and campus office spaces. In these dynamic workplace environments, IT needs to ensure that specific workers or work groups are subjected to the correct security policy controls, regardless of the connection location, so they can use the applications that they are entitled to access. With our most recent innovations and integrations, Cisco’s SD-WAN fabric is ready to support IT’s security needs while ensuring optimal application experiences for the hybrid workforce as well as customers and partners.
The Cisco SD-WAN secure fabric has evolved in multiple directions to address hybrid workforce by:
- Bringing identity awareness with Cisco Identity Services Engine (ISE) into the SD-WAN fabric to authenticate people and devices as they access networked resources,
- Extending the network security fabric to remote home offices and workspaces,
- Detecting advanced persistent threats through integrations with Cisco Secure Network Analytics.
Integration with Cisco Identity Services Engine
Cisco’s Identity Services Engine (ISE) is the state-of-the-art network access control (NAC) solution for managing all types of endpoints. It provides people and devices with secure access to network resources with a zero-trust architecture. Cisco ISE serves as a policy decision point by performing authentication and authorization of the people and devices connecting to the network. To enable authentication, ISE integrates with identity providers such as Active Directory. Cisco’s SD-WAN vManage integrates with ISE to enable IT to configure security policies based on users and user groups connecting to the SD-WAN fabric. IT can apply comprehensive security capabilities—such as application firewall, anti-malware protection, intrusion prevention, and URL filtering—throughout the SD-WAN fabric to a specific user or user group anywhere in the enterprise campus to remote locations. (Refer to Fig.1)
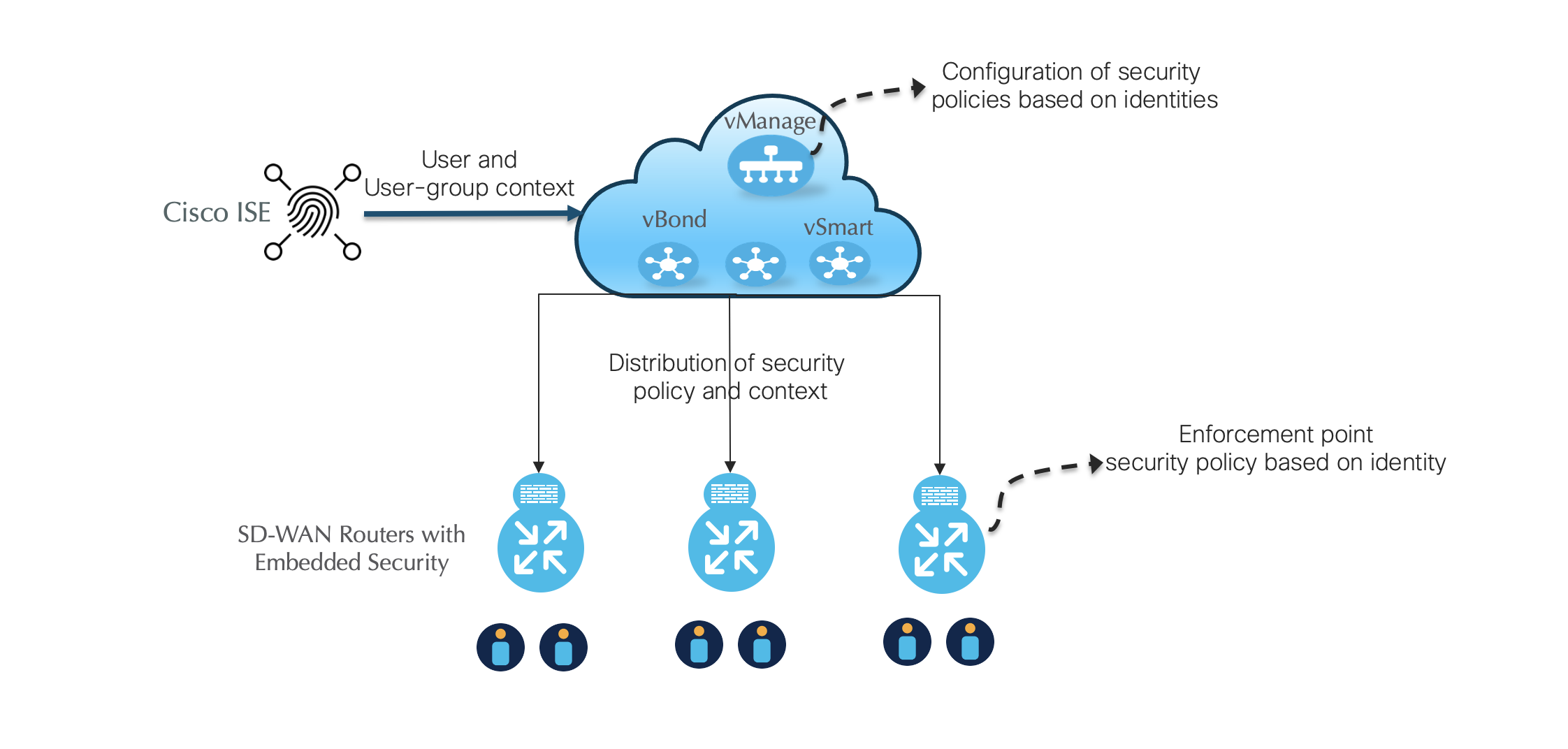
Consider a scenario in a university where the network administrator would like to limit access to social media sites for students—but then make an exception for a specific user group in recruiting for social outreach purposes. Access policies can now be configured on Cisco vManage through user and user-group-based URL filtering.
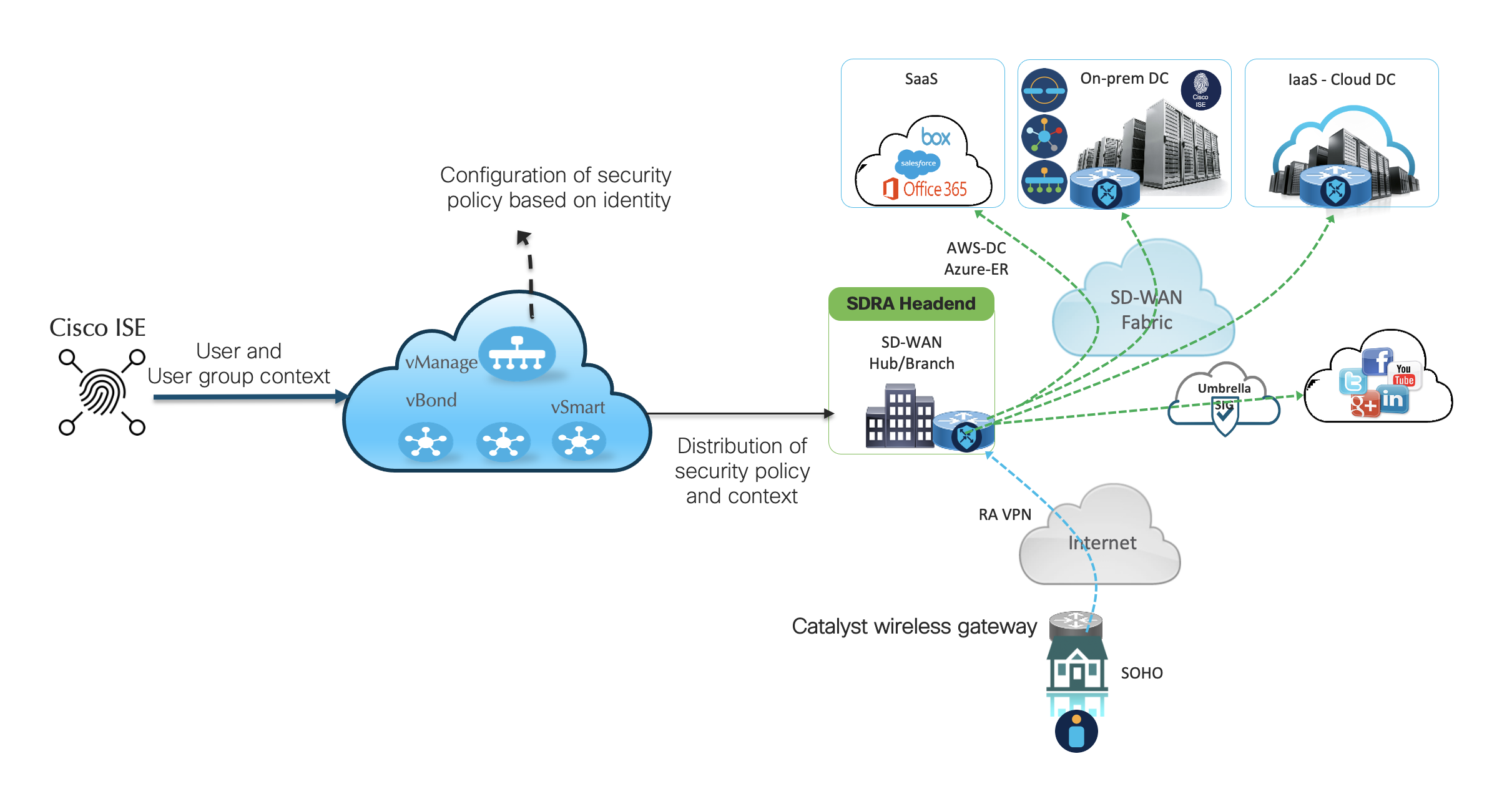
Connecting and Protecting the Home Office
Cisco’s Catalyst Wireless Gateway platform enables the remote home office workforce to seamlessly connect to the secure SD-WAN fabric. Remote workers connect locally to a Catalyst Wireless Gateway at home and authenticate network access permissions via Cisco ISE. The IPSec tunnels that originate from Catalyst Wireless Gateways are terminated on an SD-WAN branch router. This enables the user and user-group-based policies to be applied from the Cisco ISE Policy Server to remote home-based workforces, thereby extending the scope of the identity-based secure fabric. (Refer to Fig 2)
Securing Enterprise Branches with Cisco Secure Cloud Analytics
From a security perspective, enterprise branches employing direct internet and multi-cloud access connections are particularly susceptible to breaches that are signatureless and able to exploit vulnerabilities, compromise credentials, and access encrypted communications. These behaviors can occur weeks to months before a file-based threat is injected and can continue to occur even after the breach as the threats move laterally east-west to target corporate assets.
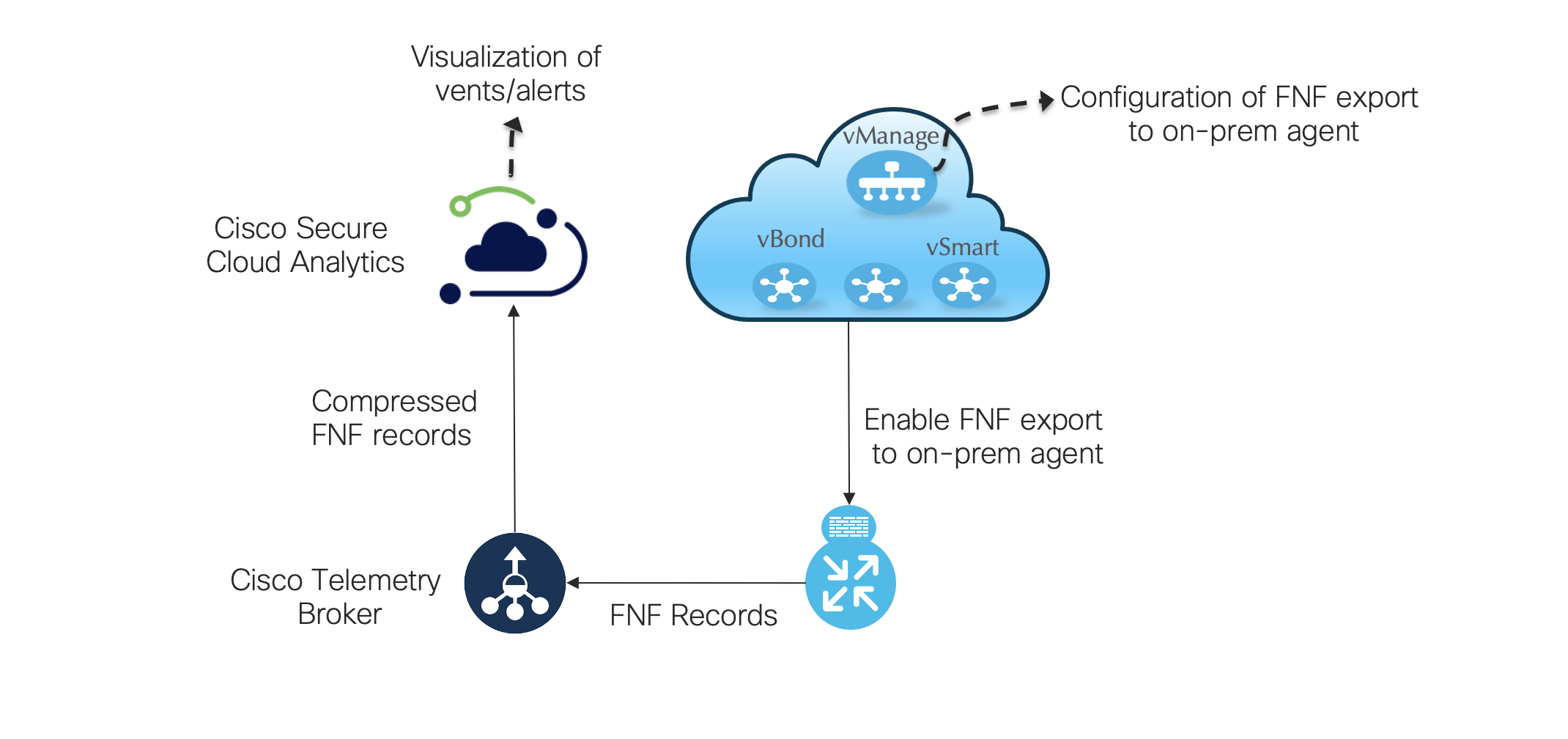
Cisco vManage can now export Flexible NetFlow (FNF) records to the Cisco Telemetry Broker. This enables Cisco Secure Cloud Analytics to detect behavioral threats associated with credential theft, insider threats, consequences of misconfigurations, signatureless day-zero exploits, and encrypted threats. These new integrations with Cisco vManage enable IT to:
- Maintain network visibility and reporting on hybrid/multi-cloud and on-prem networks;
- Enable protection against Advanced Persistent Threats such as workload vulnerabilities, data exfiltration, privilege escalation, stolen credentials, and encrypted threats;
- Enable faster identification of threats and indicators of compromise;
- Provide policy verification;
- Identify vulnerabilities due to misconfigurations.
A More Secure SD-WAN Fabric from Campus to Home
The Cisco SD-WAN fabric has increased its scope to include securing the remote workforce with new integrations with Cisco ISE and Cisco Secure Cloud Analytics. Now IT can extend access and security policies across the enterprise campus to branches and remote workers at home—wherever people need to connect to the SD-WAN fabric.
Learn more about Cisco SD-WAN
Know and control devices and users on your network
Additional Resources:
Hybrid Work Animated Explainer Video
Cisco Remote Workforce Network Solution Overview
Get curated content from Networking experts at the Networking Experiences Content Hub






Thanks Ram for this Blog! So from now onwards for user segmentation we dont need to extend from sda to sdwan, directly we can do in sdwan network right?
Yes, we can define what a user or group of users can access.