Zero trust network access (ZTNA) is the ideal architecture for securing remote access to enterprise resources.
But in OT environments, ZTNA needs to be distributed.
Remote access is key for operations teams to manage and troubleshoot operational technology (OT) assets without time-consuming and costly site visits. In many organizations, machine builders, maintenance contractors, or the operations teams themselves have installed their own solutions: cellular gateways that nobody knows about or remote access software that IT is not controlling.
Traditional remote access solutions have too many drawbacks
These backdoors are at odds to the OT security projects undertaken by the IT/CISO teams and create a shadow-IT situation which makes it difficult to control who is connecting, what they are doing, and what they can access.
On the other hand, Virtual Private Networks (VPN) installed by IT teams in the industrial DMZ (iDMZ) have drawbacks of being always-on solutions with all-or-nothing access to OT assets. This makes it challenging to control when someone connects and what they have access to without using jump servers to manage sessions and complex firewall rules that need to be frequently updated to prevent wide-open access.
Existing ZTNA solutions do not translate well to OT
Industrial organizations are starting to deploy Zero Trust Network Access (ZTNA) solutions as alternatives to always-on VPNs. ZTNA is a security service that verifies users and grants access only to specific resources at specific times based on identity and context policies. It starts with a default deny posture and adaptively offers the appropriate trust required at the time.
The solution consists of a ZTNA trust broker, typically a cloud service, that mediates connections between remote users and OT assets. The trust broker communicates with a ZTNA gateway deployed in the industrial network. The gateway establishes an outbound connection to the trust broker which in turn cross-connects to the remote user, thereby creating a communication path to the OT assets in the proximity of the gateway.
In field networks like traffic control cabinets at roadway intersections, or utility pole-mounted capacitor bank control cabinets, installing dedicated ZTNA gateways is not an option because space is an issue. When space is available, having to maintain dedicated ZTNA gateway hardware just to access a few OT assets puts an undesirable burden on customers.
In larger industrial networks, such as manufacturing plants, the ZTNA gateway is centralized in the iDMZ to avoid the cost and complexity of distributing dedicated hardware in the OT network. But this centralized architecture puts the ZTNA gateway too far from the OT assets and suffers the same drawback of the legacy VPN design:
- In such environments IP addresses are often reused, and many assets sit behind NAT boundaries which makes them unreachable to the ZTNA gateway in the iDMZ. The complexity now falls on the end customer to expose these private IPs to the higher layers of the Purdue model.
- In addition, because the ZTNA gateway is far from the OT assets, preventing lateral movement of remote users between OT assets becomes challenging.
Both these aspects negate key tenants of ZTNA, namely resource isolation and limiting lateral movement.
Cisco is embedding the ZTNA gateway in industrial networks
With Secure Equipment Access (SEA), Cisco is solving the challenges of deploying secure remote access to operational assets at scale. It embeds the ZTNA gateway function into Cisco industrial switches and routers, making secure remote access capabilities very simple to deploy at scale. There is no point hardware solution to source, install, and manage. No complex iDMZ firewall rules to configure. Enabling remote access is just a software feature to activate in your Cisco industrial network equipment.
Distributing the ZTNA gateway function anywhere in the network lets you remotely access every asset. The Cisco industrial switch or router that provides secure and reliable connectivity to OT assets, now also provides zero trust remote access to these assets, whatever its IP address or your NAT strategy. And the same network equipment can also enforce micro-segmentation policies to prevent lateral movements in the case the asset is used as a jump host. Only Cisco offers such an advanced security capability in industrial switches and routers today.
Enabling zero trust network access for OT
Managing a large number of ZTNA gateways across your operational environment is simple. Cisco Secure Equipment Access comes with a cloud portal that centralizes gateway management and configuration of remote access policies. It acts as a ZTNA trust broker, verifying users and granting access only to specific resources based on identities and contexts.
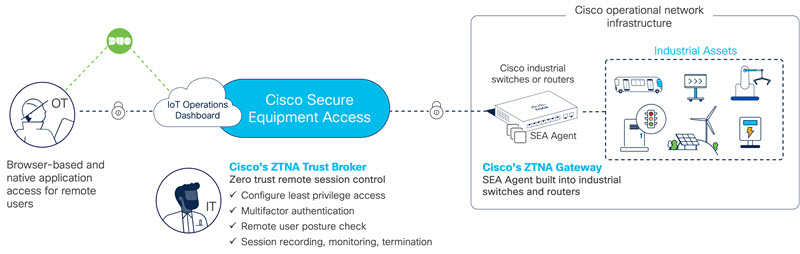
Remote employees, vendors, and contractors connect to the Secure Equipment Access cloud portal where they are authenticated and offered access only to the devices you choose, using only the protocols you specify, and only on the day and time you allow.
Remote access sessions start with a default deny posture and Secure Equipment Access adaptively offers the appropriate trust required at the time. Assets are hidden from discovery and lateral movements are made impossible. IP addresses are never exposed in the iDMZ, further reducing your attack surface.
Operations administrators can easily create credentials to meet their business needs and grant access to OT assets in two different manners:
- Clientless ZTNA. Users just need a web browser to access remote OT assets using RDP, VNC, HTTP/S, SSH, or Telnet.
- Agent-based ZTNA (which we call SEA Plus). Cisco SEA establishes a secure IP communication channel between the user’s computer and the OT asset so any desktop application can be used for advanced tasks, such as file transfer or PLC programming using native applications for instance.
Cisco Secure Equipment Access is designed to enforce strong zero trust security policies and offer advanced monitoring and compliance capabilities:
- Multifactor authentication (MFA) to address the risk of stolen credentials.
- Single sign-on (SSO) to streamline the user experience and enforce strict user policies from a centralized location.
- Device posture check to assess the remote user’s security posture and only grant access to hosts with malware protection software installed for instance.
- Session monitoring with the ability to join a session and view in real time what a remote user is doing.
- Session termination offering administrators the ability to kill an active session.
- Session recording to go back in time and watch what remote users did.
We will detail these features in upcoming blog posts over the next few weeks. Make sure you subscribe to our OT Security newsletter to receive them in your inbox. In the meantime, learn more about Cisco Secure Equipment Access (SEA), and have a look at our Cisco Validated Design Guide for assistance on how to implement ZTNA in your operational environment.




