 In a recent cybersecurity study, Gartner reported that data center protection is the foundation of digital business and innovation. With organizations embracing digital business, they need to address the lack of directly owned IT infrastructure and the prevalence of services outside of IT’s control. These services represent some of their biggest security risks.
In a recent cybersecurity study, Gartner reported that data center protection is the foundation of digital business and innovation. With organizations embracing digital business, they need to address the lack of directly owned IT infrastructure and the prevalence of services outside of IT’s control. These services represent some of their biggest security risks.
Furthermore, Gartner predicts that by 2020 sixty percent of organizations will experience a major service failure due to security incidents. And service outages damage the brand. Yet according to the latest Cisco cybersecurity survey, 71 percent of large enterprises believe data protection concerns are impeding their innovation.
The key to successfully navigating these data center challenges is pervasive visibility – if you don’t see something, then you can’t possibly know how to protect against it. Cisco Tetration Analytics provides pervasive, unprecedented visibility across every node in your data center and cloud infrastructure. Coupled with the right dynamic policy enforcement, it allows you to efficiently and effectively manage your organization’s risk posture.
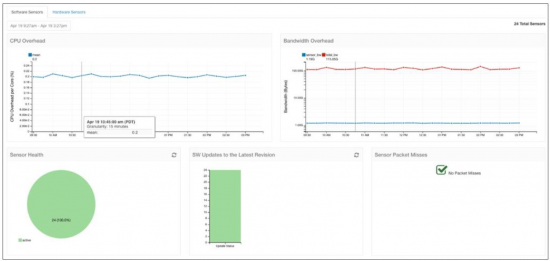
Cisco Tetration Analytics incorporates a mix of network/hardware sensors that monitor every single packet at line rate and server/software sensors with very low overhead. These sensors work with a big data analytics cluster that operates in real time, presenting actionable insights with easy to understand visuals. Additionally, it provides application dependencies, automated white-list policy recommendations, policy impact analysis, detection of policy deviation and network flow forensics.
If you want a zero trust data center model and are interested in migrating from black list to white-list security to shrink the surface of attack, but lack information and resources to implement or maintain it, you can follow simple five step Cisco Tetration Analytics implementation guide below.
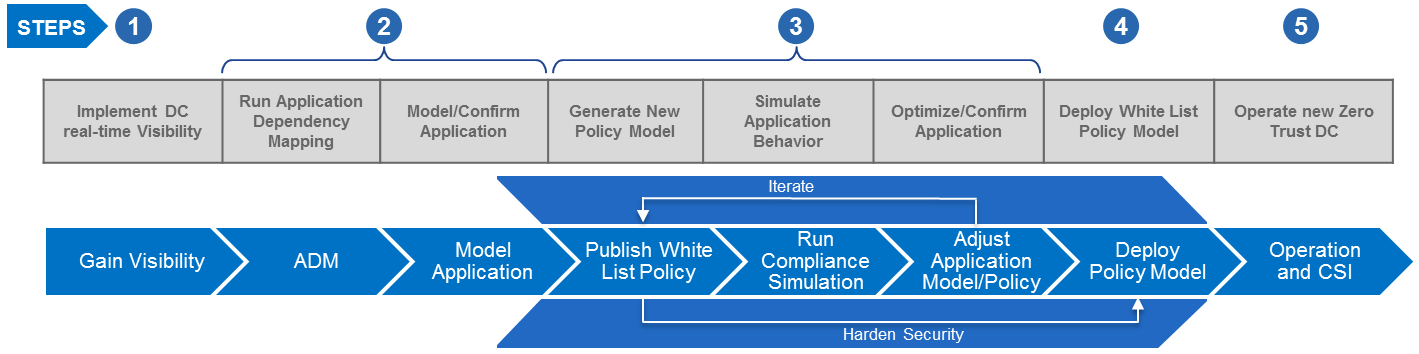
1 – Gain Real-time Visibility: Gaining pervasive real-time visibility is the foundation for zero trust operations in data center. This step entails installing on-prem Tetration Analytics platform, software host and network hardware sensors. You can immediately start collecting and storing all data flows in your data center. All searchable when, where and how you want.
2 – Map Application Dependencies: Tetration Analytics provides application behavior based mapping of processes and data flows using unsupervised machine learning algorithms. Smart enough to map and group business applications, Tetration autonomously creates application cluster views.
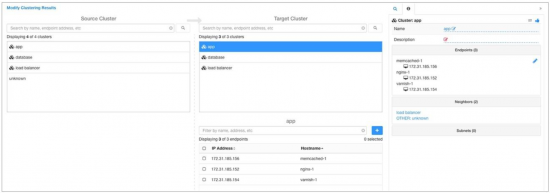
If any adjustments are needed, Tetration also allows you to redesign or model new groupings so that you can get to confirmed Application Dependency Map (ADM) template to be used for creation of white list policy.

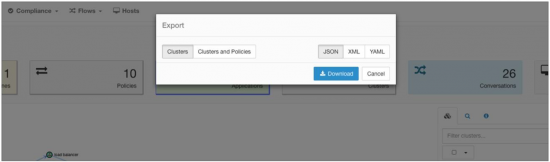
The application mapping then can be exported in various data interchange formats for the next step – whitelist policy enforcement on data center infrastructure.
3 – Recommend White List Policy:
Enabling “zero-trust operations” in data center hinges on Tetration’s automated whitelist policy generation that dramatically reduces the surface of attack and simplifies compliance. In a whitelist policy nothing communicates by default, and exceptions are explicitly allowed. This prevents attacks from propagating across applications, tenants and data.
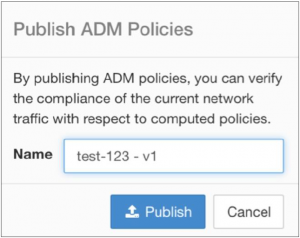
Publishing application dependency policies obtained in the previous step to a policy compliance workspace allows you to run policy experiment. You can then verify compliance of the past network traffic with respect to recently calculated policies. Simply select the policy group you wish to test and the time period in which you wish to test.
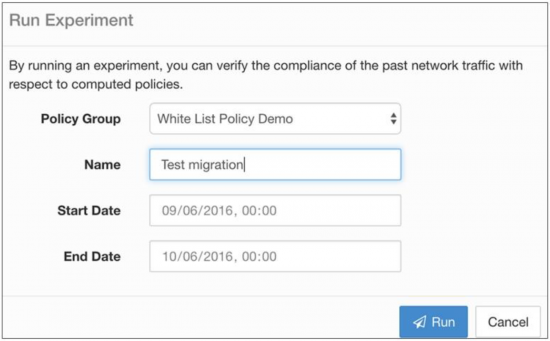
Next, run the simulation of whitelist policy and assess its impact before applying it in the production network. You can immediately see which flows will be classified as compliant, noncompliant or dropped when this policy is enforced.
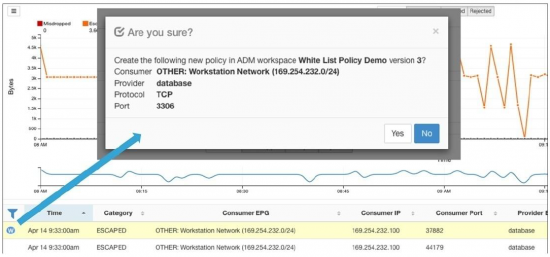
The end result is the new whitelist policy, deployment of which will result in zero trust data center environment.
4 – Deploy White List Policy: With the compliant and confirmed white list policy model available, it is time to export the policy model to SDN controllers, such as Cisco ACI. SDN controllers then enforce this new white list policy model in provisioning data center infrastructure to create zero-trust operations in production environment.
5 – Operate Zero Trust Data Center: On an ongoing basis, Tetration continues to collect network flows and uses them to generate application connectivity patterns and detecting any deviations from baseline application behavior. Combining unsupervised machine learning, anomalous behavior detection, and intelligent algorithms, Tetration Analytics brings new levels of network and security analytics to the data center.
Change is inevitable, as forces outside the business demonstrate. It’s up to businesses to decide how they’re going to respond to change. IT infrastructure and operations organizations need to quickly and flexibly deliver business services and enterprise apps that best equip a modern workforce. Cisco Tetration Analytics will accelerate your organization’s digital transformation journey by giving you previously unattainable knowledge about data center. Respond quickly to changes in your digital business and to changes happening in your data center and cloud environment, while becoming more secure each day, as additional policy is discovered, simulated, applied, and verified!
This is the only way your business can create competitive advantage and stay relevant in today’s digital world!
Learn More:
Cisco Tetration Analytics Overview
Cisco Tetration Video – Cisco IT implementation of zero trust data center operations across 50,000 servers with 70% less staff time by using Tetration Analytics platform
IDC White Paper – See the details in this storyline and the many additional benefits Cisco IT achieved with Tetration Analytics deployment – check it out!




Network/hardware sensor? Every single packet? Doing this with optical tap? SPAN ports 1-1 matching upstream ports to maintain line rate? Most platforms can’t span that much? how does this scale beyond a small deployment? Furthermore how do you scale analytics of every single packet in a 1+ Tbps environment? With Hadoop and other analytics platforms, this request is not far-fetched…