Our focus is to make collaboration secure, simple, and scalable. There is no reason to compromise between simplicity and security. At Cisco Webex, we know millions of you across the globe use video conferencing technology every day and meetings are at the core. Highly sensitive and confidential information including contracts, finances, earning details, planned deals and partnerships, M&A activity, patents, new IP and products, and much more are regularly discussed. Just weeks ago, we published a blog outlining what makes Cisco Collaboration a proven, trusted solution, and at the same time making it easy to use and manage.
Laser-Focused on Security
Having spent 14+ years in the security industry, one thing I learned is that it is never a good idea to bypass security measures for the sake of convenience and simplicity. And when so much sensitive data is being shared in video conferencing, including the ability to utilize a person’s personal camera, security must be the foremost concern.
At Cisco Webex, we live by secure, simple, and scalable principles.
As such, when you chose Cisco Webex for your collaboration needs, you can feel confident that you are receiving the highest level of security, including SOC-2 Type 2, ISO 27001, FedRAMP compliant, GDPR compliant, and end-to-end encryption.
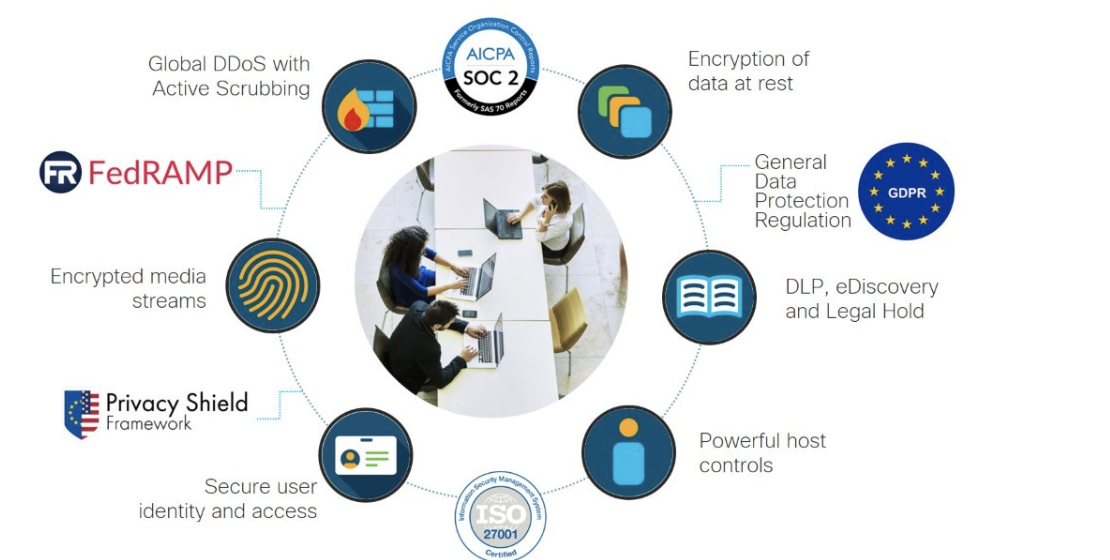
With Cisco Webex you get end-to-end encryption.This means your data remains encrypted with a key that you own — from the moment any data leaves your machine up until it gets to the recipient’s device.You can put this key into your own data center and it remains totally secure within your control, managed and accessible by you. All messages, files, whiteboards, and actions are end-to-end encrypted, whether in-transit, at-rest, and even in-use. While other solutions offer things like “Bring Your Own Key” or “Encryption at Rest,” Cisco Webex is the only vendor that has this end-to-end.
Cisco’s strategy is to develop a highly secure architecture with Webex while enabling an open platform to allow interop with all meetings and devices. Cisco has prioritized security in the design, development, deployment, and maintenance of its networks, platforms, and applications.
As part of Cisco, we put a huge focus on security. Examples of this include Cisco PSIRT and CSIRT programs.The Cisco Product Security Incident Response Team (PSIRT) is a dedicated, global team that manages the receipt, investigation, and public reporting of security vulnerability information related to Cisco products and networks. Cisco PSIRT provides security advisories. The PSIRT team is available around the clock to identify possible security issues in Cisco products and networks.
The Cisco Computer Security Incident Response Team (CSIRT) forms the investigative branch of Cisco’s Information Security organization and is Cisco’s cyber investigations and forensics team. CSIRT provides Cisco with tailored security monitoring services to protect Cisco from cyber attacks and loss of intellectual assets. CSIRT’s primary mission is to help ensure company, system, and data preservation by performing comprehensive investigations into computer security incidents, and to contribute to the prevention of such incidents by engaging in threat assessment and detection, mitigation planning, incident trend analysis, and security architecture review.
Simple, Secure, Scalable… AND Open
While we place a premium on security, interoperability and openness are also critical. Video conferencing and collaboration solutions need to allow businesses to connect with their customers and partners without restrictions. This means that collaboration solutions must integrate and work with the various devices, conferencing, calling, and productivity tools in the market today.
We also recognize the importance of building integrations with the tools you use every day. Cisco has created a partner ecosystem to help drive new integrations and innovations. We believe that flexibility and choice in your toolset is central to a successful user experience.
We are serious about interoperability with the tools you love and use every day. Some examples of the work we have done this space include our native integrations with Google, Apple, Microsoft and Slack and more. More about how Cisco Webex works well with others can be found at this Webex interoperability blog from Anurag Dhingra.
We are setting the bar higher because you use Webex for your most trusted, sensitive information and assets. Unsupported collaboration applications could lead to increased customer risk. Soon, you’ll see us announcing a certification program ensure even greater security and interoperability with third-party tools. Compatibility and security can be challenging, that is why we will only support third-party collaboration vendors who meet our security standards.
To summarize, we are laser-focused on delivering secure collaboration solutions. We are also delivering an open platform that meets rigorous security standards.We will continue to ensure our security and user experiences on the Cisco platform are the gold standard.
To understand more about our focus on security, please read our white paper on meeting security
We’d love to hear what you think. Ask a Question, Comment Below, and Stay Connected with Collaboration on social!
Collaboration Social Channels
Facebook
Twitter
LinkedIn
YouTube
Learn More






Nice Posr
Great article on security!! Thanks for sharing.
We should highlight secure in Webex outdoor advertisments.
Amazing article! Thank you!