If you were driving a race car without brakes, chances are you’d keep your speed in check. How else could you manage the corners? Pushing the pedal-to-the-metal on the straightaways and actually reaching the car’s peak performance would only end poorly when the road turns. The same can be said for enterprise network security: only with proper security capabilities can you run your digital business at breakneck speed.
This breakneck speed is being fueled by the growth of mobility, IoT devices, and private and public clouds, all of which massively increase the attack surface for threat actors. Meanwhile the top recommendation of the newly released Cisco 2017 Annual Cybersecurity Report is that “as the attack surface increases, defenders must focus on their most important goal: reducing their adversaries’ operational space.”
Fortunately, you can keep the pedal-to-the-metal while reducing your adversaries’ operational space by building security capabilities into the very fabric of your network. The network can provide deep visibility into network traffic patterns and rich threat intelligence. With Cisco DNA, the network can be used to quickly detect cybersecurity threats and then automatically take action to stop them.
Baked in, not bolted on
Cisco’s Identity Services Engine (ISE) and TrustSec can help turn the network into a sensor and enforcer. ISE provides visibility and control of users and devices on the network, while TrustSec provides software-defined segmentation to isolate attacks and restrict movement of threats in the network. Together they form a dynamic duo.
At Cisco Live Berlin, we’re announcing the latest Cisco DNA Security advancements, including the latest releases of ISE and TrustSec.
Deeper visibility, more granular control: Cisco ISE 2.2
ISE 2.2 offers much deeper visibility into applications on endpoints and more granular control. But the feature that really floats my boat is the ability to define “DEFCON” policy sets that allow customers to escalate their response to prolific threats.
Rapid threat containment is tremendously powerful in dealing with a handful of systems at a time. But what if numerous systems are simultaneously getting “popped” and a threat is spreading in real time? That’s where ISE DEFCON policy sets come in.
DEFCON powerfully enhances your incident response playbook with the ability to move to pre-defined responses to systemic attacks. Rather than changing the authorization of individual users and devices, or implementing policy changes manually, changing DEFCON state changes the TrustSec policies defining how users, devices, and systems can talk to others — essentially raising the “network drawbridges” to protect your critical data and maintaining essential services. For example, you could define DEFCON 4 to kick all guests off the network, DEFCON 3 to kick all BYOD users off the network, DEFCON 2 to restrict peer-to-peer traffic, and DEFCON 1 to severely limit access to your “crown jewels.”
ISE 2.2 also provides Streamlined workflows that include guest, secure access, and BYOD setup with Cisco Wireless LAN Controllers in as little as 10 minutes. This approach also extends to customers migrating from the Cisco Access Control System (ACS), which Cisco recently announced will go end-of-sale. An enhanced ISE migration tool now streamlines ACS replacement so you get all the same ACS benefits coupled with advanced secure access, profiling, and postures capabilities offered with ISE.
And it’s not just us. SC Magazine recently recognized Cisco ISE with their 2017 Best NAC Solution award. If you’re interested in learning more you can ready this technical blog.
Dynamic Segmentation: Cisco TrustSec 6.1
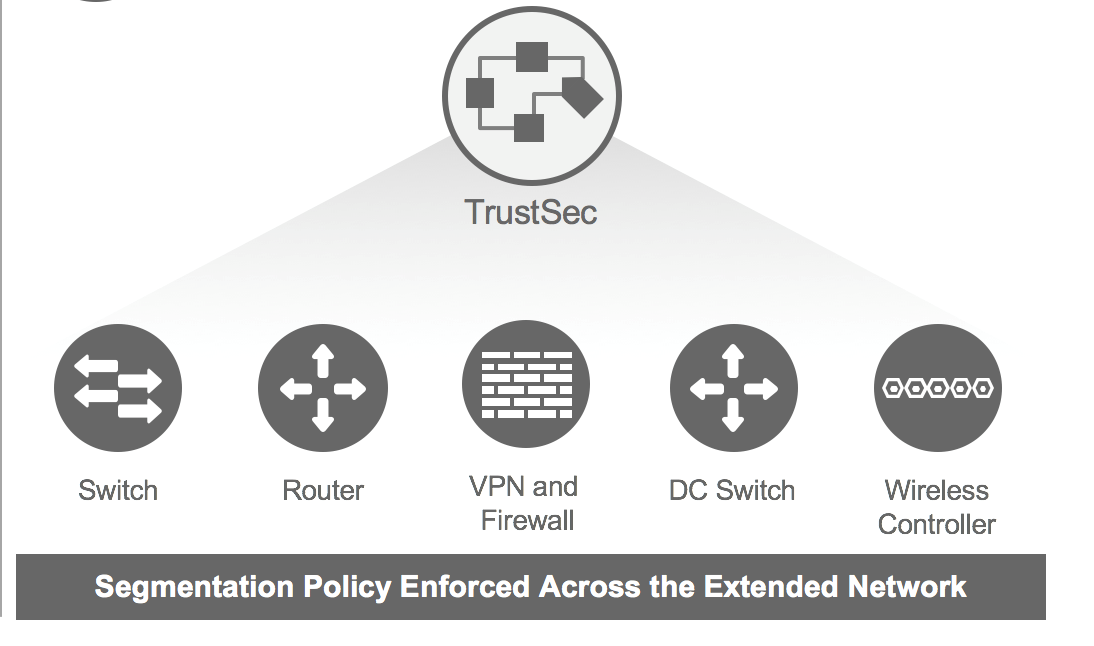
TrustSec Software-Defined Segmentation reduces risk and restricts the lateral movement of threats in a network, allowing for these segmentation policies to be enabled and changed without reconfiguring network devices. This proven technology can enable security policy changes 98% faster and with 80% less operational effort than the traditional VLAN-based segmentation.
TrustSec has now been extended to Cisco Access Points, WAN routers, Cloud Services Routers and Industrial Ethernet switches that now work seamlessly with the existing TrustSec-enabled Catalyst and Nexus switches. Coupled with new integration with Cisco ACI, TrustSec now enables dynamic segmentation anywhere on the network, from the edge of the network to the data center to the cloud.
Among the many use cases, Mondi is using TrustSec to rapidly integrate new acquisitions into their security architecture and dramatically simplify firewall policy management. We at Cisco are using TrustSec to segregate high-risk labs as well as simplify security during divestments. Banks are using TrustSec to meet regulator’s segmentation requirements and ensure that only authorized users have access to financially regulated applications. And security-minded agencies of governments are using TrustSec to restrict peer-to-peer communications that could cause lateral movement of threats.
With these new capabilities on ISE and TrustSec, Cisco is now the first in the industry to deliver software-defined segmentation across the entire network—from the network to the endpoint to the cloud – with complete application visibility.
This is important because you can only drive at digital speed if you have the right security. And by turning the network into a sensor and enforcer, Cisco is helping our customers accelerate their digital journey.





Very good overview how the ISE and it’s ecosystem is getting better and better. But telling the customers the junior admin can set the system up in ten minutes is dangerous. For that, the whole system is much too complicated (and I say that as a Cisco instructor teaching ISE classes).
Good point, Karsten. Many use cases as well as large-scale deployments will require more time and resources to deploy. The point I was making is that we have dramatically simplified the product for the mentioned use cases, and for small-scale deployments you are able to deploy ISE in a matter of minutes https://www.youtube.com/watch?v=yikrmBje3rI&t=14s. Hope this helps to clarify my statement. And thanks for being an ISE instructor!
Скупка картриджей дорого