Scale, speed, new consumer experiences — these goals all come to mind as drivers of the massive transformation happening in media & entertainment. When it comes to the underlying IP and cloud technology needed to bring this transformation to life, Cisco has a unique ability to deliver comprehensive solutions, which we have laid out in the Cisco Media Blueprint.
Security is one of the core components of the Media Blueprint, and its role is to let our media customers digitize, connect and cloudify with confidence that their digital assets remain safe. But before we talk about solutions — more on that coming next week! — I’d like to take a moment of your time to reflect on the growing challenges that make it so important to take a proactive stance on security, and to implement a robust security strategy.
In the IP era, media companies wishing to protect their businesses, the content and services that they create and deliver, and the consumers they serve, need to address a new and ever evolving range of cyber-attacks and piracy threats. These attacks can originate at multiple points and target multiple places across the entire content path, from acquisition to consumer experiences.
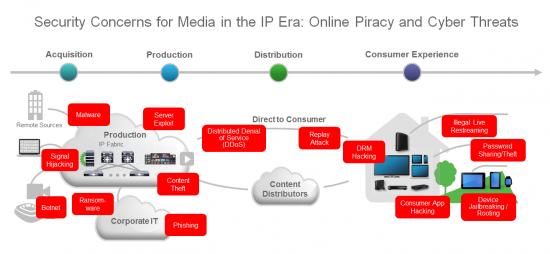
Cyber-attacks, which have traditionally been a concern for enterprise IT departments, are now very relevant for the media space. With video production and delivery increasingly moving to IP and cloud, the traditional boundaries between media infrastructure, corporate IT, and the outside world are blurring. This change brings great opportunities but also poses new cybersecurity risks.
Attackers seeking to steal sensitive business or consumer data, pirate content, tamper with broadcast streams or impair consumer services now have many more ways to achieve their targets.
And there’s no need to be a hacking whiz to launch an attack. Consider this example — a simple online search gave me handy guidance on creating a botnet in 15 minutes using available tools. In case you are not familiar, botnets allow remote control of an Internet-connected device such as an employee’s PC or phone even without the device owner’s awareness. Attackers use them for hacks such as distributed denial-of-service (DDoS) and corporate espionage.
Piracy always has been and will remain a fundamental security issue for media & entertainment. As the industry evolves, so do the pirates’ techniques, meaning that anti-piracy solutions have to adapt constantly in tow.
First, as pirates have more sources from which they can pilfer content in various stages of production, distribution and consumption, accurately identifying and stopping those sources of leakage — while ensuring superb experiences to legitimate consumers — is a growing challenge.
Second, the ubiquity of broadband, which is fueling the transformation of consumer expectations and experiences around the globe, is also fertile ground for pirates to distribute video content and services illegally. At any given time, the latest popular series or live sports games may be available illegally on pirate web sites, IPTV-like paid services, online streaming and social media platforms to name a few.
So, what should we do about the challenges ahead? How can media companies achieve the security needed to thrive, without compromising their customers’ experiences or their business goals? A sustainable solution needs to take into account the operations and economics of the media industry as well as that of pirates and hackers. Then, of course, the technical ability to see, quickly react and effectively protect against evolving threats is critical.
If you are as passionate about the changes happening in this industry as we are, or curious to hear more about the security solutions Cisco has to offer, talk to us! If you are attending NAB Show, be sure to stop by — we’re in booth SU8502CM.





this is a very contentious area. In Australia the laws have been changed to try and protect peoples’ intellectual property, without restricting their rights to surf the net for legal content.
Thanks Peter for your comment. Indeed the protection of rights – for intellectual property owners and consumers alike – and the definition of those rights, is a complex topic. This is especially true amidst the major changes happening in how content is distributed and consumed. In this changing reality, security implementations should adapt to detect and ensure proper usage of content without limiting consumers’ ability to access content legally – also not an easy challenge.