This post authored by Nick Biasini with contributions from Erick Galinkin.
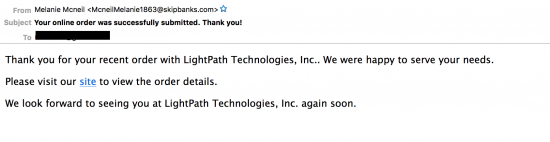
Exploit kits have been a recurring threat that we’ve discussed here on this blog as a method of driving users to maliciousness. Users typically encounter exploit kit landing pages through compromised websites and malvertising. However, we’ve found a new email twist to the standard procedures associated with getting users into the exploit kit infection chain.
Usually when we see compromised websites serving exploit kit gates there are malicious iframes dropped on single pages or throughout the entire site. These iframes can either be links to an exploit kit landing page directly or to a gate. Using a gate allows the adversary to change the location of the landing page without having to change the compromised wordpress site. In the spam campaign that we detected and blocked, adversaries were instead linking users to “hidden” web pages (pages located within the site’s directory structure) on these sites instead of linking users to pages containing an iframe.