Exploit kits
Multiple Cobalt Personality Disorder
Despite the notion that modern cybersecurity protocols have stopped email-based attacks, email continues to be one of the primary attack vectors for malicious actors — both for widespread and targeted...
Threat Spotlight: Sundown Matures
This post authored by Nick Biasini with contributions from Edmund Brumaghin and Alex Chiu The last time Talos discussed Sundown it was an exploit kit in transition. Several of the large exploit kits had left the landscape and a couple of strong
Take the RIG Pill: Down the Rabbit Hole
Executive Summary Talos is monitoring the big notorious Exploit Kits(EK) on an ongoing basis. Since Angler disappeared a few month ago, RIG is one EK which seems to be trying to fill the gap Angler has left. We see an ongoing development on RIG. This
Sundown EK: You Better Take Care
This post was authored by Nick Biasini Over the last six months the exploit kit landscape has seen some major changes. These changes began with Nuclear ceasing operations in April/May and arrests in Russia coinciding with the end of Angler in June.
Talos ShadowGate Take Down: Global Malvertising Campaign Thwarted
Yet another example of how organizations work together to stop threats affecting users around the globe.
Connecting the Dots Reveals Crimeware Shake-up
This Post Authored by Nick Biasini For a couple of weeks in June the threat landscape was changed. Several high profile threats fell off the landscape, causing a shake-up that hadn’t been seen before. For a period of three weeks the internet
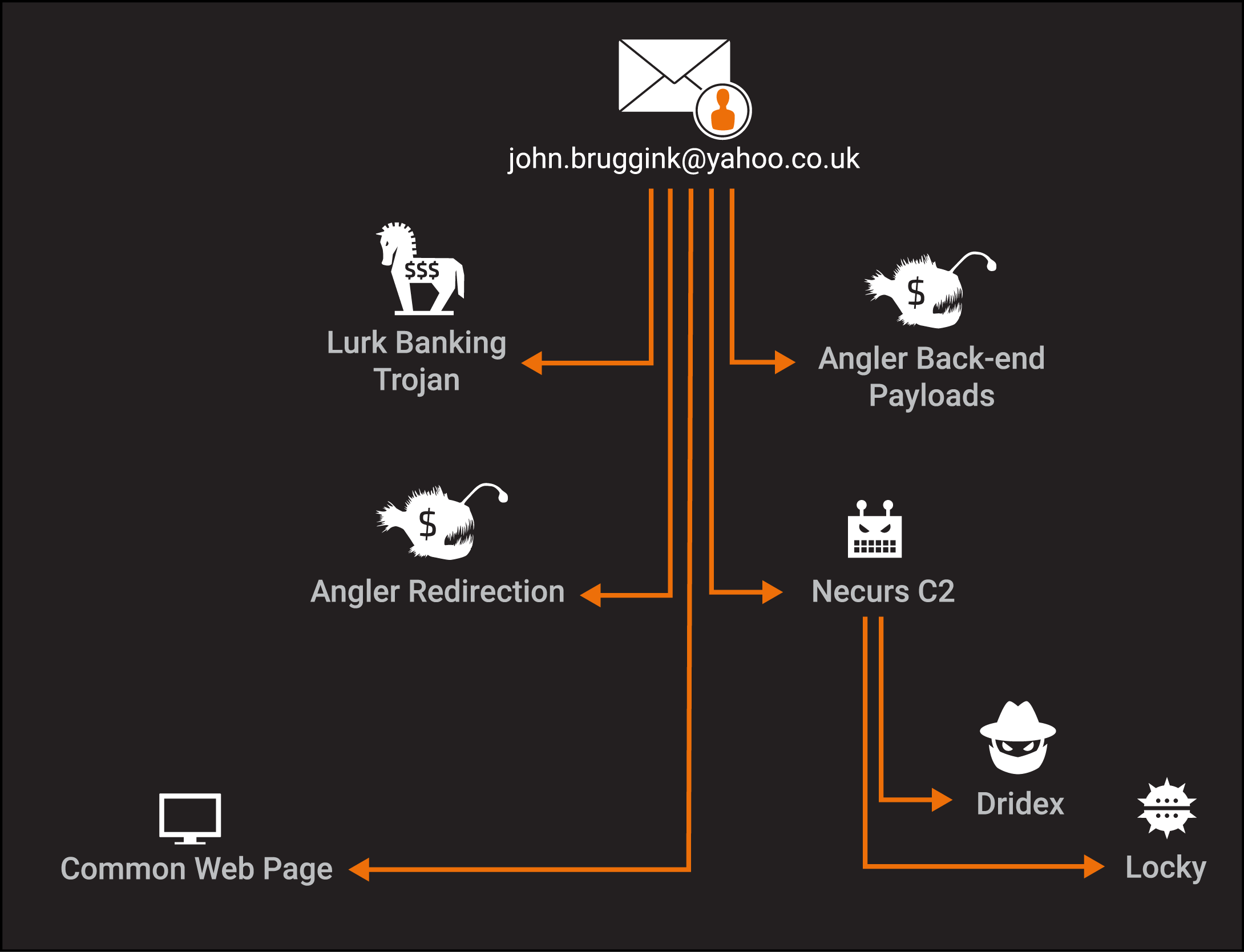
Angler Catches Victims Using Phish as Bait
This post authored by Nick Biasini with contributions from Erick Galinkin. Exploit kits have been a recurring threat that we’ve discussed here on this blog as a method of driving users to maliciousness. Users typically encounter exploit kit
Threat Spotlight: Spin to Win…Malware
This post was authored by Nick Biasini with contributions from Tom Schoellhammer and Emmanuel Tacheau The threat landscape is ever changing and adversaries are always working to find more efficient ways to compromise users. One of the many ways that