This blog post is part three of a three-part series discussing how organizations can address mobile security concerns through an architectural approach to mobility. The first post discusses how next-gen Wi-Fi models will pave the way for secure mobility. The second post highlights the risks versus the rewards of mobility.
Providing corporate network access via mobile devices is nothing new to today’s IT administrators. However, the future of BYOD and mobility will change as rising generations expect and demand more seamless and secure connectivity. Recently Tab Times editor Doug Drinkwater shared a similar idea: BYOD is still in an early phase with plenty of new challenges and opportunities ahead.
In this last installment of this security and mobility series, I’ll discuss why BYOD policies will change and outline how C-level executives can leverage employees as solution drivers in order to solidify the future of mobility within their organization.
The Millennial Workforce
A major reason BYOD will need to evolve is because of the growing millennial workforce that is already adept and well versed with using mobile devices. Already outnumbering Baby Boomers, it’s estimated that by 2030, Millennials will be the largest population group. They are the first generation to grow up using touchscreens, social media networks and a myriad of devices with Internet capability.
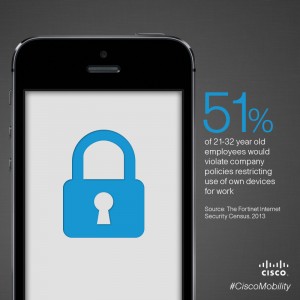
As digital natives, Millennials are also fearless when it comes to bringing new technology to the workplace. Recent research from The Fortinet Internet Security Census 2013 reveals that over half (51%) of 21-32 year old employees would contravene company policies restricting use of own devices, cloud storage, and wearable technologies for work.
Another concerning figure from the study is that 14% of respondents said they would not tell an employer if a personal device they used for work purposes became compromised.
The way they use portable devices continues to change and evolve. So that means security—how we manage the risks of those BYODs—also has to evolve.
So, how can organizations evolve their security policies to match the brazen BYOD approach of the new workforce?
Onboarding Employees
As employees demand more freedom and flexibility with regard to mobile device use at work and consumer devices provide an increasingly cost-effective and attractive way to keep employees engaged and productive, IT must remain vigilant about ensuring an appropriate experience and protecting the network and corporate intellectual property.
One key way this can be accomplished is to expect employees to become more aware of IT security issues. Organizations can leverage the benefits of a more tech-savvy workforce, thanks to the consumerization of IT, to create opportunities for employees to fix less critical BYOD/mobile issues instead of clogging up precious IT resources.
With this in mind, here are a few steps C-level executives can take to propel their BYOD policies to the next level:
- Incorporate your mobility strategy within your business strategy. The process of creating a safe and productive BYOD environment begins with understanding the goals of your organization with respect to mobile devices. Some businesses have minor security concerns and actively encourage the use of any type of mobile device. In some other businesses, the vast majority of data must be protected with the highest levels of security. Allowing employees to securely use mobile devices in a world without the traditional boundaries that have guarded sensitive data requires a new and far more pervasive approach to security. Establishing the appropriate mobile device strategy begins with business requirements.
- Integrate threat education with BYOD policy training. There is a direct link between BYOD usage and “threat literacy.” By including information about real and perceived threats, IT leaders can have a better chance of improving security measures across the organization.
- Empower employees to troubleshoot minor tech errors themselves. Common tech issues that have consumed IT resources in the past are likely to lessen as a more tech-familiar workforce comes aboard. Encourage these employees to fix small issues themselves and hold training for those that need extra help. If enterprises can make this potential a reality they could allow IT departments to focus on higher-level issues, enabling enterprises to stay on the cutting edge of security and truly be innovative.
I’m confident that if business leaders harness the power of the rising workforce, the rewards of mobility can be better realized. Learn more about mobile security trends in the just-launched 2014 Annual Security Report or check out Cisco Secure Access.
Did this blog inspire you to make a change in your mobility strategy? Let us know via comment below or join the conversation on Twitter, #CiscoMobility.