Often it is quite surprising how long old, well-known vulnerabilities continue to be exploited. Recently, a friend sent me an example of a malicious script used in an attempted attack against their server:
![]()
The script attempted to exploit the Horde/IMP Plesk Webmail Exploit in vulnerable versions of the Plesk control panel. By injecting malicious PHP code in the username field, successful attackers are able to bypass authentication and upload files to the targeted server. These types of attacks could be one avenue used in the DarkLeech compromises. Although not as common as the Plesk remote access vulnerability (CVE-2012-1557) described in the report, it does appear that this vulnerability is being actively exploited.
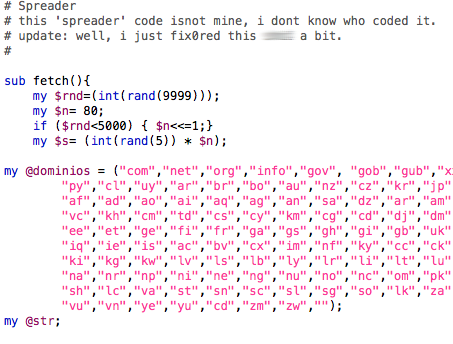
In this specific instance, the attackers were using an IRC-based botnet as a payload. The botnet was technically minimal, but did include basic flooding capabilities.
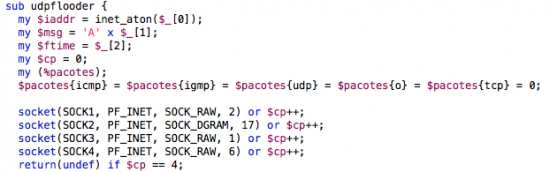
The Perl script used in this case has been around for a number of years, and the bot is openly discussed in PHP exploit groups. What’s interesting is that this particular version seems to have been pieced together by many individuals, judging from the alternating English and Spanish found throughout the script.
The active exploit of this year-old vulnerability serves as an important reminder that website operators and administrators must keep systems up-to-date. This is especially urgent with vulnerabilities that are remotely detectable. This means not just the operating system, but every program and add-on for those programs also needs to be kept up-to-date. A vulnerability left unpatched in any one of them can lead to total system compromise. Left unpatched, this bug and others like it will likely continue to be exploited for years to come. Only time will tell what other payloads may be installed.






Impresionante documento
Parallels takes the security of its partners very seriously and regularly advises partners about how they can protect themselves against new threats. The exploit warned about by a Cisco researcher was in the 3rd party Horde webmail for Plesk 9.3 and earlier (products circa 2009 and earlier), not in the Plesk control panel itself. These Plesk versions are end-of-lifed now, but a patch was promptly issued in Februrary 2012 at http://kb.parallels.com/en/113374.
Parallels agrees with this Cisco researcher: “The active exploit of this year-old vulnerability serves as an important reminder that website operators and administrators must keep systems up-to-date. This is especially urgent with vulnerabilities that are remotely detectable. This means not just the operating system, but every program and add-on for those programs also needs to be kept up-to-date. A vulnerability left unpatched in any one of them can lead to total system compromise.”
We also strongly encourage our customers to subscribe to our support e-mails, subscribe to our RSS feed and add our KnowledgeBase browser plug-in.
Dear Parallels:
Hard to take seriously your claim that you “[take] the security of [your] partners very seriously”.
I was running Plesk 7.5 seven years ago (2006) when you were bundling Horde version 3 with IMP version 4.1. Now — did I mentioned seven (7) years later? — with Plesk 11 you’re bundling (wait for it) Horde 3 and IMP 4.3! It’s so old it’s still not using Ajax! It’s an embarrassment to have to offer it to clients used to webmail modelled on the Gmail interface that everyone has been trying to emulate for the better part of a decade!
News flash: Horde has moved on to version 5 and IMP is onto 6!
Craig
Just to be clear this comment is not from Cisco.
Hello Craig,
Plesk 11.5 is in final Previews you can download from http://www.parallels.com/download/plesk/11.5 Webmail is updated to support both Horde/IMP 5.0 and Roundcube. It will release at the end of the month.
@Parallels: Glad to hear it.
@Craig Williams: Sorry! Didn’t even notice we had the same name. My name is indeed Craig, but I am not the author of this article and I do not work for Cisco!