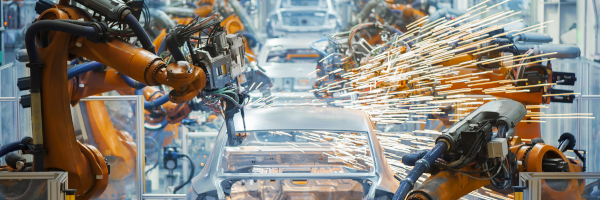
Securing industrial networks: What is ISA/IEC 62443?
Securing industrial operations is top of mind. But converting good intentions to action can be challenging! Fortunately, the ISA/IEC 62443 standards provide a framework to move ahead. But what is it exactly?