With BYOD, virtualisation, cloud adoption, and IoT becoming commonplace in most organisations, users, devices and workloads are more dynamic than ever. This creates visibility and attribution problems as well as segmentation policies that are increasingly complex and difficult. At a business level, organisations define security policies using roles, functions, risk-centric attributes and combinations thereof, but much can get lost in the translation to a network-centric policy with building blocks like IP addresses. This makes segmentation policies static and inflexible; leaving organizations too open and vulnerable to an ever-evolving threat landscape or too closed and hindered by the demands of today’s dynamic businesses.
Over the years, firewalls have evolved from ip addresses, ports & protocols to identity and application awareness and have become increasingly threat-centric with the inclusion of capabilities like intrusion prevention and advanced malware protection. However these Next Generation Firewalls (NGFW) often still sit as siloed points of enforcement in the network. In addition, with the rise of Software Defined Networking (SDN), networks have evolved to support attribute/group based policy mechanisms, which allows writing intent and policy into the fabric of the network, and when needed stitching in firewalls for deeper inspection and advanced control.
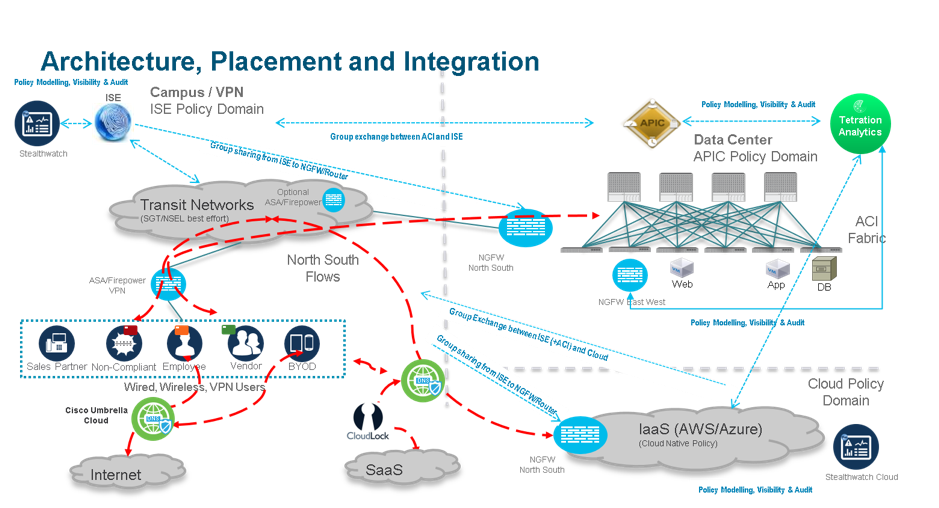
Cisco’s Software Defined Segmentation architecture allows practical application of the above concepts into most environments. Dynamic context-aware policies can be written into the network fabric and security controls, which are a combination of business attributes (roles, functions and risk), and context can be shared across multiple domains (like campus/branch, datacentre and cloud) and multiple enforcement points like firewalls and network devices. Unlike static network attributes, these business-centric attributes are far more flexible, which makes segmentation policies extremely succinct and policy management very efficient requiring minimal changes even in the most dynamic environments. Visibility also becomes much richer with Cisco’s Software-Defined Segmentation model.
Let’s look at the components and how they work together:
- Cisco Network & Cisco Identity Services Engine (ISE) – As users and devices connect to the network (over wired/wireless/vpn), ISE classifies them into security groups based on attributes like role, function, location, health, etc. There are various mechanisms in Cisco network devices & ISE to extract these rich contextual attributes. Some examples are active authentication or passive identification for identity, profiling for device type and posture assessment for compliance using agent or agentless mechanisms. In addition, Cisco ISE also has several integrations with third party tools to receive information on device compliance, infection state and unpatched vulnerabilities. Rules within ISE combine these rich contextual attributes into a security group assignment for every connected endpoint. These security groups then form the basis of security policies, centrally managed on ISE and enforced across the network fabric. This policy centric approach is available for implementation in most Cisco campus and branch networks today. For environments already running Cisco’s Catalyst 9000 series switches, Cisco DNA can integrate with ISE for contextual enrichment and orchestrate the network to implement this policy centric model, eliminating configuration complexity.
- Cisco Application Centric Infrastructure (ACI) – As workloads connect to the datacentre (DC) fabric, they are assigned by ACI to endpoint groups based on applications attributes like function and risk. Group based policies are created centrally on ACI and enforced across the DC fabric. ACI follows a whitelist policy model, which ensures every workload has a valid group and an assigned policy to be able to communicate.
- Context Sharing between campus/branch and DC– The security groups in ISE/Cisco DNA and endpoint groups in ACI are exchanged between the two policy domains, to allow uniform north south policies (user/device to DC) to be created for the campus/branch and DC.
- Context Sharing with cloud hosted environments – The security groups in ISE/Cisco DNA, both created locally and received from ACI integration, can be shared with a capable router or NGFW hosted in the IaaS cloud, to allow uniform north south policies (user/device to cloud) to be created at the cloud perimeter.
- Context Sharing to discreet security controls – ISE can further share all contextual groups (native or acquired from ACI and cloud) into other platforms like firewalls, intrusion prevention systems, proxies, single sign on services, etc. to allow easier policy at the other security layers. As an example, a NGFW or router positioned at the internet perimeter or DC perimeter (ACI or otherwise) or even IaaS provider (AWS, Azure, etc.), can receive all the groups classifications and mappings from ISE. This ensures a consistent, context rich and yet simple group based policy language across all domains and even discreet controls.
- Policy Efficiencies – Moves, Adds & Changes (MACs) are reduced drastically as policies are based on roles and functions which don’t change very often. Policies are also more flexible and encompassing of criteria like risk and impact. These group-based policies are also now distributed across the network fabric. Lastly when deployed on discreet firewalls on premises or in the cloud, these policies consume far fewer resources and memory as opposed to static IP based access control entries.
- Rapid Threat Containment – in the event of an incident or workflow change, group membership of an endpoint or workload can be simply changed (manually or programmatically via APIs) to allow a different policy profile to be applied, significantly bringing down risk resolution times. Due to their low resource demands, policies applicable to risky groups (eg. infected or quarantined) can be pre-created and applied to segmentation infrastructure and will dynamically enforce the required controls, whenever connected endpoints move to these risky groups.
- Better Visibility & Remediation – Visibility tools understand and use this common group-based language. ISE shares the groups and assignments with Cisco Stealthwatch, a network visibility and security analytics solution. Alarms within Stealthwatch are reinforced with rich contextual information such as user, device, location, etc. and offending endpoints can simply be assigned to a quarantine group via the Stealthwatch-ISE remediation workflow, resulting in an accelerated threat response.
- Better Visibility & Policy Recommendations in the DC – Cisco Tetration uses the concept of application groups based on behaviours for application dependency mapping and visibility in the DC & cloud (IaaS) and also recommends (for ACI/NGFW) and enforces policies (on endpoints/VMs) using these application groups.
Below is a diagrammatic example of these policy components and integrations.
In summary, there’s still value in good segmentation policies, both for least privilege access control and for prevention of lateral malware movement. Organisations embarking on improving their segmentation policies (and even zero trust projects), need to look beyond firewalls and NAC (network access control) projects and embrace these concepts of group based policies and context sharing to reduce costs and get the most out of their network and firewalls, in the campus, branch, DC and cloud.
Most organisations would benefit by starting small and then building these concepts into their segmentation roadmap. However for organisations that have all the building blocks already (i.e. ISE, ACI, NGFW, Cisco DNA, etc.), they need to start looking at integrations, one at a time, to bring in further automation and improve their overall security posture.
Check out the software defined segmentation and network visibility and segmentation pages to learn more about these holistic solutions.






Thank you for sharing this . Great insights on how software defined segmentation is the next big thing.