As I’ve talked about before, many organizations have traditionally relied on a tactical approach to security: encounter a new threat, buy another box. This happened time and time again, resulting in a complex security “frankenstructure” of products.
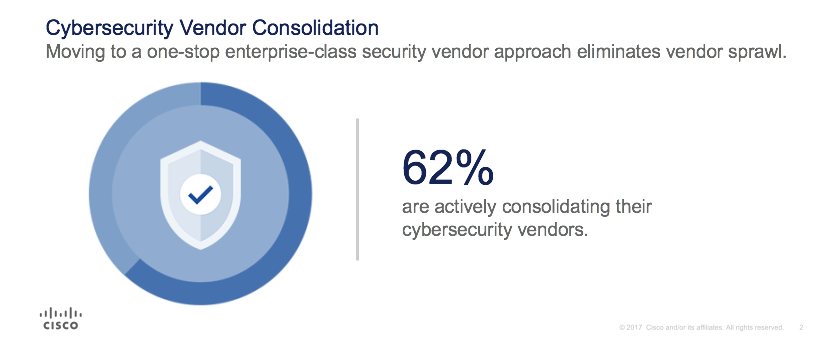 But new independent research from ESG shows that 62% of companies are now rethinking the way they purchase and deploy security technology. They’re actively consolidating their cybersecurity vendors and looking for enterprise class providers. Why? The top two reasons are:
But new independent research from ESG shows that 62% of companies are now rethinking the way they purchase and deploy security technology. They’re actively consolidating their cybersecurity vendors and looking for enterprise class providers. Why? The top two reasons are:
- Greater operational efficiencies: security and IT teams gain greater operational efficiencies when products are designed to work together, and;
- More effective against new threats: Fewer, yet stronger vendor partners have the wherewithal to bring more innovative products that better address evolving threats.
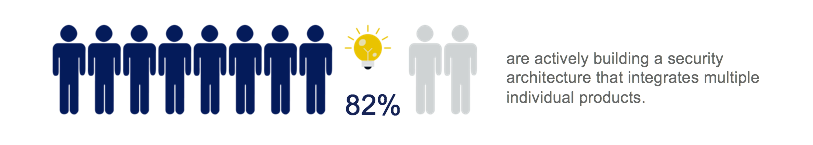 The vast majority of companies use an architectural approach to guide their consolidation – one that integrates products so that they work together to secure the network, endpoints, applications, and the cloud.
The vast majority of companies use an architectural approach to guide their consolidation – one that integrates products so that they work together to secure the network, endpoints, applications, and the cloud.
The ESG findings underscore what we have been hearing from customers for some time – disparate point products can drive up cost, operational complexity, and management headaches. It is for this very reason we place considerable time and effort into building products that are simple, open, and automated – to get to an architectural approach that spans:
- Network – using your networks for security and segmentation, stopping threats at the edge, and preventing lateral movement.
- Endpoints – encompassing productivity so employees can work securely from any device, at any time from any location; compliance to ensure that every device that connects to the network meets your security policies; and also security to protect roaming users and defend against advanced malware protection on the device itself.
- Cloud – using cloud-delivered security that protects users on and off network, over all ports and protocols; discovers and controls cloud apps; and protects data and workloads in the cloud while allowing employees to get their work done and securely collaborate.
We’ve made significant investments to deliver products that fit together for simpler security that delivers automation to yield a force-multiplier of effectiveness.
The ESG research goes on to explore what companies look for when selecting an enterprise-class cybersecurity vendor. Four key attributes rise to the top.
- Industry expertise
- Alignment of security with strategic IT initiatives
- Reduced complexity and a lower TCO
- Products designed to scale and integrate
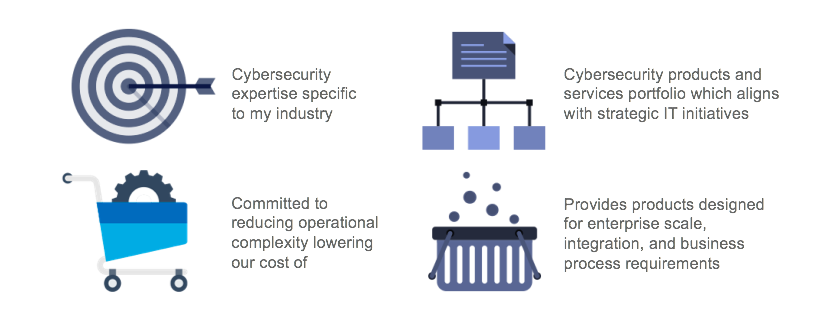 Cisco came out on top, embodying all of these.
Cisco came out on top, embodying all of these.
- Our team of more than 5,000 brings a diverse set of industry experience while our security services team has expertise in most if not all verticals/industries. We’ve helped:
- a prestigious healthcare organization detect and stop attacks like ransomware;
- a large school district build a more secure digital learning environment;
- a global manufacturer automate network security;
- a leading retailer save costs while increasing protection against advance malware;
- and a major financial institution move to the cloud more securely.
- Cisco, as a company, considers how to integrate security into IT/networking – in order to provide as much value as possible to all of enterprise IT.Our products leverage the Cisco network to fit into your larger IT initiatives while streamlining operations with cloud-delivered security and management. We incorporate automation across IT infrastructure to quarantine devices, and can even allow you to clean up malware in a couple of clicks.
- I have spoken before about gaps in security resulting from a patchwork of point products and how we aim for better outcomes with greater simplicity through our architectural approach. This approach also delivers approximately 40% TCO savings over deploying point products, based on research from Forrester.
- As for scale and integration – few do this better than we do. With products built with openness in mind, we streamline the process for scaling security to protect mobile users or new branch offices coming online by activating additional security capabilities into your existing routers, endpoint security or other devices.
And finally, when asked about which vendors deliver the best cybersecurity intelligence (considering quality and efficacy) – once again Cisco Security comes out on top with Cisco Talos, our threat research organization. Why is Talos the strongest? Because it possesses the best global visibility into the threat landscape and leverages the industry’s most robust research capabilities including an unprecedented diversity of data sources, to deliver advanced threat intelligence that reduce the operational surface for attackers.
When we say diversity of data sources – we see a ton: threats and malware, web traffic, email, DNS, network intrusions, and endpoint intelligence – even insights about attacker infrastructure. Talos translates that data into intelligence and coordinates our response to stop more threats. Once a threat is detected, Talos immediately coordinates protections across products, from web and email security to endpoint and network security, for a fast, synchronized response across our entire portfolio, with no effort needed by the end user. Cisco Security, with Talos, keeps organizations safer.
Operational efficiencies, innovative solutions, and stopping advanced threats. This is what more effective security postures boil down to and this is why more enterprises are looking to consolidation and looking to Cisco.
Third-party validation is critical as you make IT and security decisions. I encourage you to learn more about ESG’s findings.






Great piece, thank you!
So how does one ensure that we tap into Cisco Talos? By that I mean, are there specific configurations to make either on the routers/firewalls or servers to ensure access to this facility?
Musole: Great question. The best part is every Cisco security product and service incorporates Talos intelligence. Talos does vulnerability and malware analysis that leads to the development of detection content for all of Cisco’s security products. Talos unpacks, reverse engineers, and the develops proof of concept code to ensure we address each threat in the most efficient and effective way possible on each platform. There are lots of other ways you can get information from Talos through their website, blog, podcast, newsletter https://www.talosintelligence.com/about. You can learn more in this Talos white paper. http://www.cisco.com/c/dam/m/en_us/offers/pdfs/talos-group-whitepaper.pdf
Hope this is useful to you. Thank you for reading our blog and for the insightful question.