The Changing Face of Cyber Security
Cyber Security is quite like an onion; it brings tears to your eyes! And we at Cisco have made it our mission to wipe those tears and put a smile back on your face.
But the onion analogy does not end there. Good Cyber Defense is architected in layers, much like the anatomy of the tear-jerking bulbous root. As the network expands beyond the traditional perimeter, so does the need to provide defense in depth. We all see the trend: The boundaries of the network are blurring, even as it is being called upon to process even larger amounts of data. To monitor the pulse of your network, you have to dig deeper to find answers to the questions such as “Who attacked us?” or “What was compromised, and when?”. Your security teams might break into a sweat dealing with this reality without help, as the attack surface continues to expand.
Gone are the days when a bouncer at the entrance of your bar (or your friend’s bar) could keep troublemakers out. Today, bad actors can seep in through other points of entry, or disguise (encrypt) themselves and walk right through the front door. They sometimes even enter in plain sight, especially if they are not on the most-wanted list (yet). How then do you protect against such elements from seeping through the cracks?
What you need, if you stay with the bar analogy just a little longer, is a ‘stealthy’ manager monitoring the behavior of all entities on your premises, so that you can get alerted when something looks amiss. This trusted aid should be armed to receive inputs from multiple sources: all points of entry, as well as from folks working the floor itself.
Jump back now to the real world of IT infrastructure (unless you actually own a bar, you should still read on), and what you need is a method to monitor all your traffic, both inbound/ outbound and lateral, using a single analytical tool. By bringing together these critical sources of telemetry, you get a unified view of your perimeter and internal threats, not by manual or point-by-point correlation, but by automated and programmatic means. In this manner, you get complete end-to-end visibility into your network, with the ability to detect threats and indicators of compromise. Now, what if this capability was available without need for authoring lengthy configurations or complex rules, while requiring minimal care and feeding? All of this may to sound like a fantasy novel, but often times facts are stranger than fiction.
Welcome to Cisco Security Analytics and Logging
Cisco Security Analytics and Logging was born in the cloud, with simplicity and ease of use as a core design tenet. It has a self-evident name, and an equally simple goal in mind: aggregation of your disparate sources of telemetry into a single data store. Automated means of analysis (statistical, M/L and behavioral modelling) can then be performed on this combined data set, treating it as a single logical input. Since every aggregation effort must have a start point, Security Analytics and Logging’s kick-off candidates are the most voluminous telemetry producers in networks today:
- Firewall logs, which keep track of every connection made, and well as any incidents encountered (IPS/IDS or File/ Malware), mostly at the perimeter.
- Internal traffic telemetry produced by connections between network elements such as endpoints, switches, wireless access points, routers, etc. on your premises.
To bring together perimeter and internal telemetry, Security Analytics and Logging integrates two avant-garde SaaS products in Cisco’s security portfolio:
- Cisco Defense Orchestrator, a cloud-delivered, SaaS-based solution that cuts complexity for consistent management of policies across Cisco security products.
- Stealthwatch Cloud, a cloud-delivered, SaaS-based solution that provides end-to-end visibility, behavioral analysis, and threat detection across your private network, public cloud, and hybrid environments.
Now, you might wonder “Why stop there”? We hear you, and you are right; we are NOT stopping here. Rather, this is just the start. Security Analytics and Logging is being built out as an aggregator of data, to provide intelligence derived from desperate points in the network, treating them as a pool for analysis. The discerning mind will differentiate this as being different from the outcomes of say a SOAR, which correlates processed data, rather than crunching raw data. In this manner, the output of Cisco Security Analytics and Logging’s analyzed outcomes become a source of input for other Incident Response (IR) tools.
Tell me why we need this:
Bringing machine-scale analysis to human-scale understanding
This is how I would explain it to my Grandmother: Information is Power. The more information I can gather, the better equipped I am to arrive at the correct conviction of a threat. While I can gather convictions from numerous trusted inspectors, I can also gather my own raw data straight from the source and build my own point of view. The disadvantage of relying on others’ convictions alone is that each of them may have a limited view of the world; perimeter only, endpoint only, content only, etc. What if I gathered all the information for myself, treating these various sources as sensors, and made my own conviction in addition? Am I better or worse off?
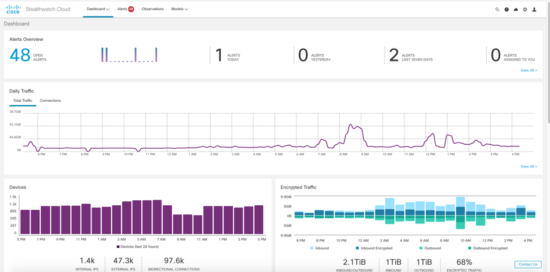
My smart grandmother would say, “Well, that depends on your ability to process all that information intelligently”. And she would be right; You need a best of breed analysis engine to do your intelligent tasks. It is for this reason that Security Analytics and Logging is powered by Stealthwatch Cloud’s advanced entity behavioral modeling and threat detection engine. We use a combination of behavioral modeling, multilayered machine learning, and global threat intelligence to automatically detect threats. For those amongst you who are already familiar with the magic of Stealthwatch Cloud, I know you must be eager to end the conversation with my grandmother, order Security Analytics and Logging, and head to your friend’s bar. Stay a little longer, and I promise that you will be on your way.
Visibility, Visibility, Visibility
It all starts with visibility. You cannot protect what you cannot see. Often times, you don’t even realize what it is that you should be monitoring. Therefore, when it comes to visibility, there are some more advanced questions that need to be addressed. These questions may come up in a conversation with your security budget office. We shall speak to some of those now:
Question 1 – Tell me what ‘accretive’ outcomes I achieve by sending firewall logs to Security Analytics and Logging for Analysis?
That is a great question. First of all, behavioral threat detections are based on baselining of network behavior based on established patterns. This is widely considered a more dynamic way of detecting threats than static rules or content-based inspection methods. It may come as no surprise to anyone that notwithstanding the most robust IPS/DPI inspection policies and rules, suspicious behaviors continue to be detected inside networks. The key word to understand here is ‘accretive’; it is by no means suggested that Cisco Security Analytics and Logging attempts to be or will ever replace other sensors such as firewalls. It does however certainly enhance the efficacy of the said sensors, by allowing correlation of anomalous behavior within your network, with the traffic that is associated with it. Such analysis may point to a potential data exfiltration or a compromised insider. As stated before, Security Analytics and Logging enables you to additionally monitor traffic generated between your internal network elements (endpoint to access points, between switches and routers, etc.). Your firewall may not be in the path of this traffic, so may not be able to provide the depth of visibility needed for making high-fidelity convictions.
Question 2 – Apart from Security alerts based on correlation of my firewall logs and Network traffic, does Cisco Security Analytics and Logging provide any other outcomes?
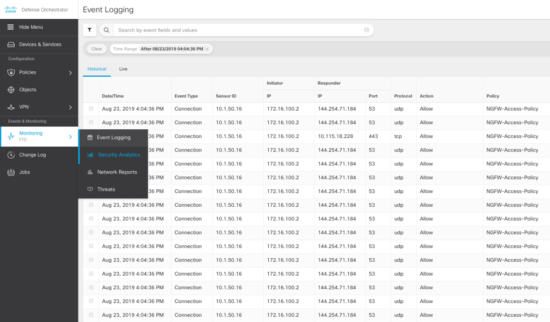
It certainly does. One of the primary use cases of storing NGFW logs is providing a historical and live view of said logs. NetSec operators love (?) sitting in front of these views and scrolling to troubleshoot based on connections that have occurred at a particular time with a particular IP address. With filters on search, Security Analytics and Logging fulfills this use case, providing real-time visibility of what is happening at your firewalls. What is more, this view is rendered within the CDO (Cisco Defense Orchestrator) user interface. Furthermore, since CDO is the curator of firewall tenants analyzed by Security Analytics and Logging, it is simpler to view logs in the portal that is used to manage those very devices.
Question 3 – If I am an existing Stealthwatch Cloud customer using my private network monitoring, what accretive value can I derive from Security Analytics and Logging?
Let’s break this down. A firewall connection log has visibility beyond what just network elements can provide. An example for this could be blocked connections, which will immediately show up in the event viewer in CDO. Filtering by all ‘blocks’, the operator can plainly see the policies that was responsible for the block. This is just one example of numerous workflows /sources that contribute to enhanced visibility that results from Security Analytics and Logging.
Better efficacy with smarter security
With our new offering, get ready to leverage effective policy management with CDO powered by Stealthwatch Cloud’s advanced behavioral analytics, for total network visibility and faster breach detection. You can now make better security policy management decisions with greater visibility and threat detection capabilities across the firewall and network. As the biggest security company in the world, Cisco has committed itself to solving platform-level challenges that span all the points in your network.
The good news is that Cisco Security Analytics and Logging, is just starting up. The intent is to foster a new security paradigm, one that reduces risk and makes compliance easier; one that fuses your business and security architecture, that frees your workforce to focus their valuable time and energy on business objectives. This will empower them to think less about threats, and more about opportunities.
Time now to enjoy that drink. Cheers.
Click here to learn more about Cisco Security Analytics and Logging for more details on how we are raising the bar on network security.






A good read. i must recommend people to try it once.
However very much informative but could have used a section to tell people about securing themselves with the simple use cases.
Like I use vpn of pure vpn whenever I purchase online and using public wifi.
As simple it is a most discussed topic now a days.