This post was also authored by Andrew Tsonchev and Steven Poulson.
Update 2014-05-26: Thank you to Fox-IT for providing the Fiesta logo image. We updated the caption to accurately reflect image attribution.
Cisco’s Cloud Web Security (CWS) service provides TRAC researchers with a constant fire hose of malicious insight and now that we are collaborating with Sourcefire’s Vulnerability Research Team (VRT) we have additional capabilities to quickly isolate and prioritize specific web exploit activity for further analysis. Thus when we were recently alerted to an aggressive Fiesta exploit pack (EP) campaign targeting our customers, we quickly compared notes and found that in addition to the typical Java exploits, this EP was also using a Microsoft Silverlight exploit. In the Cisco 2014 Annual Security Report (ASR) we discuss how 2013 was a banner year for Java exploits, and while updating Java should remain a top priority, Silverlight is certainly worth patching as threat actors continue to search for new application exploits to leverage in drive-by attacks.

https://www.youtube.com/watch?v=HdPUUW3YAi0
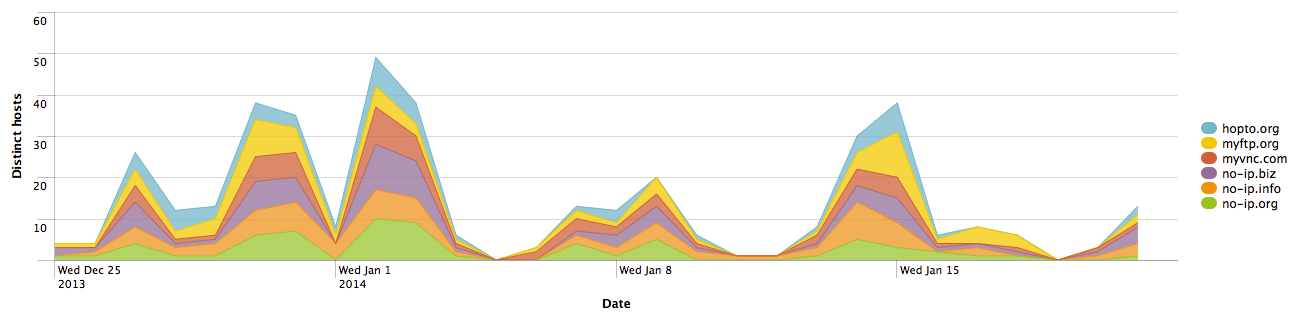
Over the past 30 days this specific Fiesta campaign was blocked across more than 300 different companies. The attacker(s) used numerous dynamic DNS (DDNS) domains – that resolved to six different IP addresses – as exploit landing pages. The chart below depicts the distribution of hosts used in this attack across the most blocked DDNS base domains.
Managements’ Bottom Line
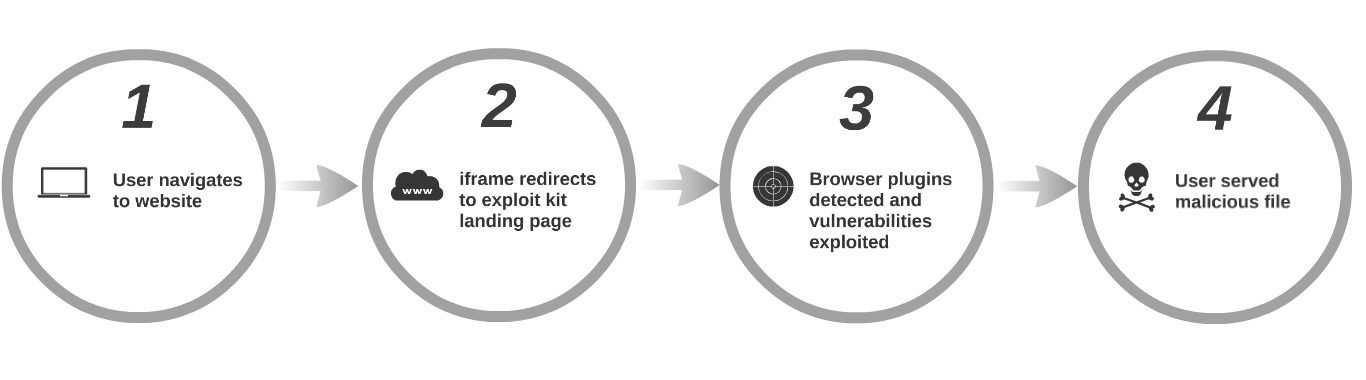
Exploit packs are easy to find, purchase, and install. Essentially they are a compilation of specific exploits for relatively trusted applications packaged into a web framework with an administrator interface for threat actor ease of use. Currently, most exploit packs are licensed on a per server basis (essentially a criminal SaaS model) which further increases revenue for EP sellers, and gives EP users every incentive to maximize a single server EP instance. EP users’ primary goal is to force as much victim web traffic to their respective EP servers as possible, in order to execute a “drive-by” attack (really it’s a reverse drive-by since the victim is moving and the attacker is stationary). Thus any number of malicious mechanisms may be used to drive unsuspecting web users to the EP server including “malvertising” (injecting a rogue advertisement into an advertising delivery network), email/social media spam, and/or compromising a legitimate website and automatically redirecting visitors.
The majority of the exploits we discuss in this particular campaign are known, meaning that patches were released for the corresponding vulnerabilities either in 2012 or 2013. The exploits used affect all of the popular rich Internet application environments including Java Applets, PDFs, Flash files, and now Microsoft’s Silverlight (essentially used by companies like Netflix for streaming media). The Silverlight exploit detection rate is particularly abysmal for anti-virus engines, likely due in part to the paucity of Silverlight custom heuristics similar to the situation for PDF exploits five years ago. To address this attack we recently wrote custom Silverlight heuristics for CWS. Additionally, Sourcefire continues to profile Silverlight for enhanced detection of future exploits. While a fully patched workstation is spared the drive-by compromise in this case, multiple “zero day” attacks occurred in 2013 which leveraged new exploits for previously unknown vulnerabilities.
Thus, corporate patching represents an important piece of information security policy, but it’s not a web threat panacea. The behavioral detection of known indicators of compromise (IoC) is the savviest approach to detecting web threats, specifically EPs. For example, this specific Fiesta campaign used over 400 different DDNS based domains. Does your organization allow traffic to DDNS domains? Typically there are a few employees in every enterprise that connect to their home network via DDNS, and certainly there are legitimate DDNS use cases, but given the high correlation between DDNS domains and malicious activity, this is an easy indicator or compromise (IoC) to detect.
There are two primary options for behavioral detection: build the capability in-house, or outsource detection to an organization that is leveraging the cloud for rapid large scale web threat analysis. Regardless of the specific business decision, near real-time detection of web threats is essential to enterprises. The web remains a crucial and trusted enabler for employees, yet presently it is also the most prolific and dangerous neighborhood on the Internet.
Incident Responders’ Operational Insight
Beginning in mid-December, 2013 Cisco CWS began blocking a large amount of HTTP requests to hundreds of DDNS domains that all resolved to 64.202.116.125 – HostForWeb (Chicago, IL). Sourcefire consultation and open source queries of the URI paths quickly confirmed Fiesta EP involvement. Additional Fiesta servers were detected at:
50.7.179.43 – MegaHoster.net (Dnepropetrovskaya, Ukraine)
50.7.179.44 – MegaHoster.net (Dnepropetrovskaya, Ukraine)
50.7.179.45 – MegaHoster.net (Dnepropetrovskaya, Ukraine)
67.159.16.250 – SOUNDBWOYKILLAZCA (Chicago, IL)
64.202.116.122 – HostForWeb (Chicago, IL)
All of the above IP addresses ultimately belong to FDC Servers, dispersed between the Chicago and Amsterdam data centers. According to Domain Tools, eleven static domains resolve to 64.202.116.125 including:
cherrychetty.com
finamars.com
hexoberg.com
jueddieslo.com
maxipont.com
yellowsub.in.ua
yelorebos.in.ua
youandyou.in.ua
yphonesge.in.ua
yppletree.in.ua
yredinblu.in.ua
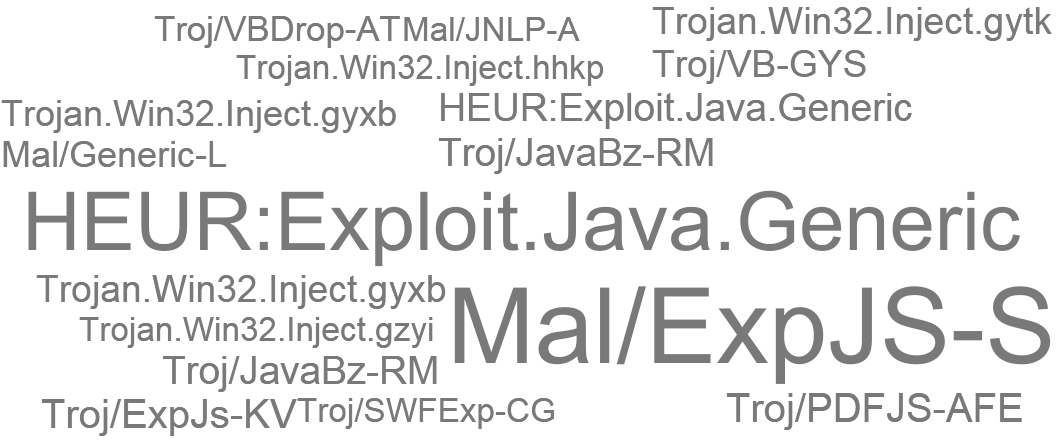
The last domain – yredinblu.in.ua – is also actively hosting Fiesta. The name servers for yredinblu.in.ua include ns1-ns3.ukrnames.com. The DNS A record for ns1.ukrnames.com is 91.197.128.182 (Operator of Virtual Data Computing LLC) located in Kyiv, Ukraine, the A record for ns2.ukrnames.com is 195.123.1.2 (CJSC Global Ukraine), and the A record for ns3.ukrnames.com is 195.64.154.36 (Ukrainian Internet Names Center LTD). These name servers are authoritative for approximately 6k domains. Thus it appears that this Fiesta threat actor(s) has a penchant for the Ukraine and is leveraging Ukrainian ccTLDs, Ukrainian name servers, and Ukrainian hosting providers. Looking at Fiesta’s specific exploits, the following word cloud depicts specific web requests as labeled by Kaspersky and Sophos (larger font equals higher request counts).
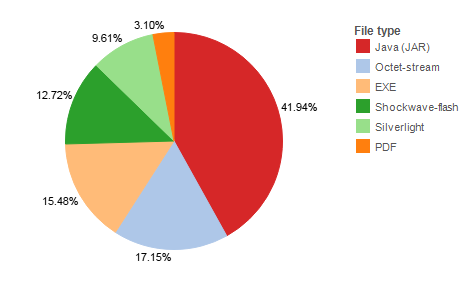
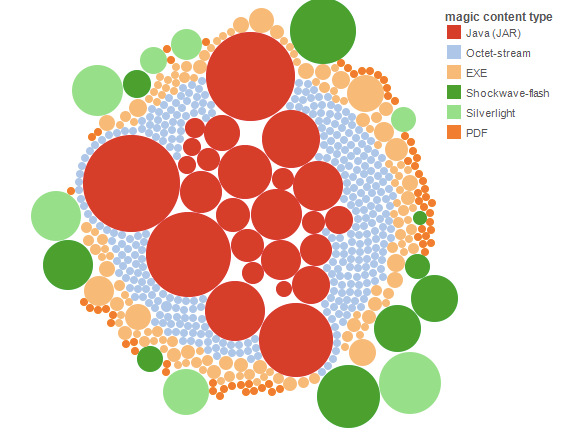
Next, the following chart depicts malicious file type percentages based on all web responses observed since mid-December, 2013.
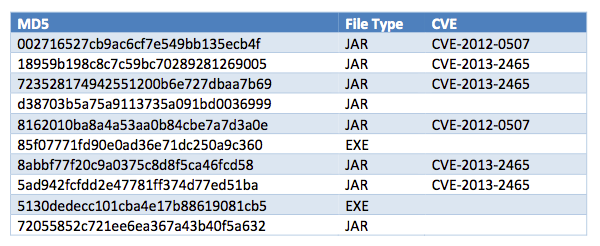
The top ten exploits blocked (by count) and their corresponding CVEs include:
The additional Microsoft Silverlight exploits include:
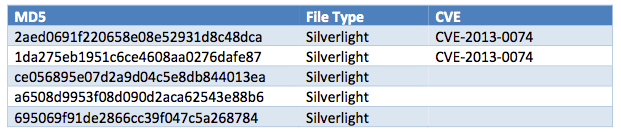
CVE-2013-0074 – subclassing System.Windows.Browser.ScriptObject to access vulnerable protected Initialize() – was generated in March, 2013, but it only works because CVE-2013-3896 allows the address of usable functions to be found, which occurred in October, 2013. The following is an excerpt from the published proof of concept which sets up the vulnerability.
// declare descendant for System.Windows.Browser.ScriptObject to access vulnerable protected Initialize()
public class MyObject : System.Windows.Browser.HtmlObject
{
public MyObject()
: base()
{
}
// access protected Initialize()
public void Init(IntPtr handle)
{
MainPage.LogAdd(“ScriptObject.Initialize(” + MainPage.Hex((ulong)handle) + “, 1, true, false)”);
Initialize(handle, (IntPtr)1, true, false); // call agcore.dll DOM_ReferenceObject()
}
}
The below is from the Silverlight malware byte code, showing identical functionality:
class tag.pig{
.ctor(){
ldarg.0
Call System.Windows.Browser.HtmlObject..ctor
ret
Init(){
ldarg.0
ldarg.1
ldc.i4.1
Call System.IntPtr.op_Explicit
ldc.i4.1
ldc.i4.0
Call System.Windows.Browser.ScriptObject.Initialize
Ret
While examining this Silverlight exploit, TRAC produced a Silverlight reverse engineering tool which we will be releasing and discussing in a future blog post.
The following graphic reveals the total distribution of malicious file types (a larger bubble size represents a higher count).
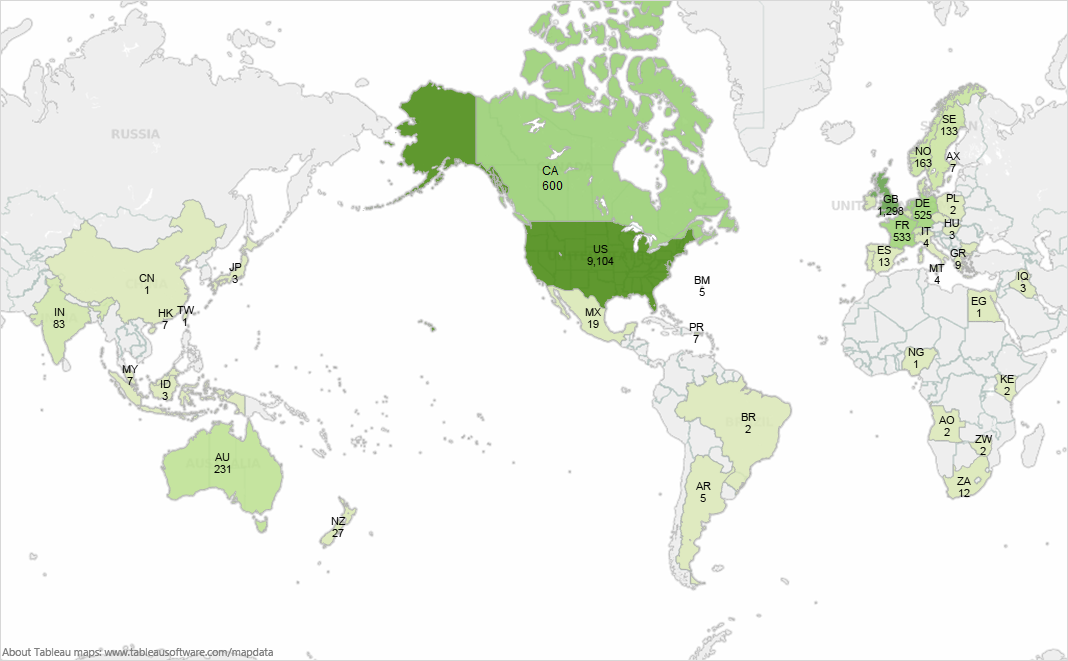
The below map represents the number of individual web requests from affected users to Fiesta EP servers. These geographic distributions largely reflect the websites used to redirect victim web users from different countries to the Fiesta servers. Obviously North America is the top target followed, to a lesser extent, by Europe.
Indicators of Compromise
The following are known Fiesta URI Paths:
/0nfxrb6/
/1oi20pr/
/4p6mvs1/
/9cui6mf/
/cl7utm6/
/cw41ugh/
/fwkl6ch/
/r1tmip5/
/uej8lir/
/uiwtv07/
/xricv8b/
You can download the full set of observed referrer URLs and Fiesta server URLs, as well as the Fiesta server responses by file hash and application category. The URI paths match known Fiesta EP patterns; URIs ending in “?1” and “?2” are landing pages which subsequently redirect victims to different payloads.
Signatures
Snort is a phenomenal open source tool for detecting exploit pack activity. The following rules are specifically aimed at Fiesta detection – SIDs: 27807, 29442, 29443, 29444 – which can be found at the Sourcefire VRT Rules Update page. The following regular expressions (REGEX) are also helpful for alerting on Fiesta landing pages and Fiesta Java responses.
Fiesta landing page detection: ^\/[a-z0-9]+\/\?[0-9a-f]{60,66}[\x3b\x3c\d]*$
Java request detection: ^\/[a-z0-9]+\/\?[a-z0-9]{60,66}[\x3b0-9]/
All of the portable executable (PE) and Java archive (JAR) exploits referenced in the indicators of compromise section are currently covered in the ClamAV and FireAMP products. The specific ClamAV definitions include:
Java.CVE-2012-0507.Dropped-1
Win.Trojan.Miuref
Java.Exploit.Dropped-30
Java.CVE-2012-0507.Dropped
Java.Exploit.Dropped-31
Java.CVE-2013-2465.Dropped-1
Java.CVE-2013-2465.Dropped
If you’re using the Sourcefire Defense Center, enabling the exploit pack rule sets is only a mouse click away. 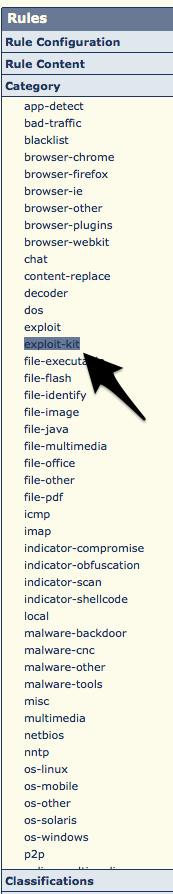
Thank you to Joel Esler for his excellent contributions to this post.






Are there any relevant log files that would contain traces of this sort of attack?