Cellular roaming has been transformed over recent years! It has shifted from a premium, high cost service that was targeted at business users, to an essential service used by consumers to keep in touch, keep entertained and update their social media profiles when they are travelling. However, at its foundation is the requirement that all participants broadly align in terms of delivering coverage and connectivity-centric value propositions. Moreover the roaming service provided by an access network is assumed to be monetized by usage fees.
OpenRoaming
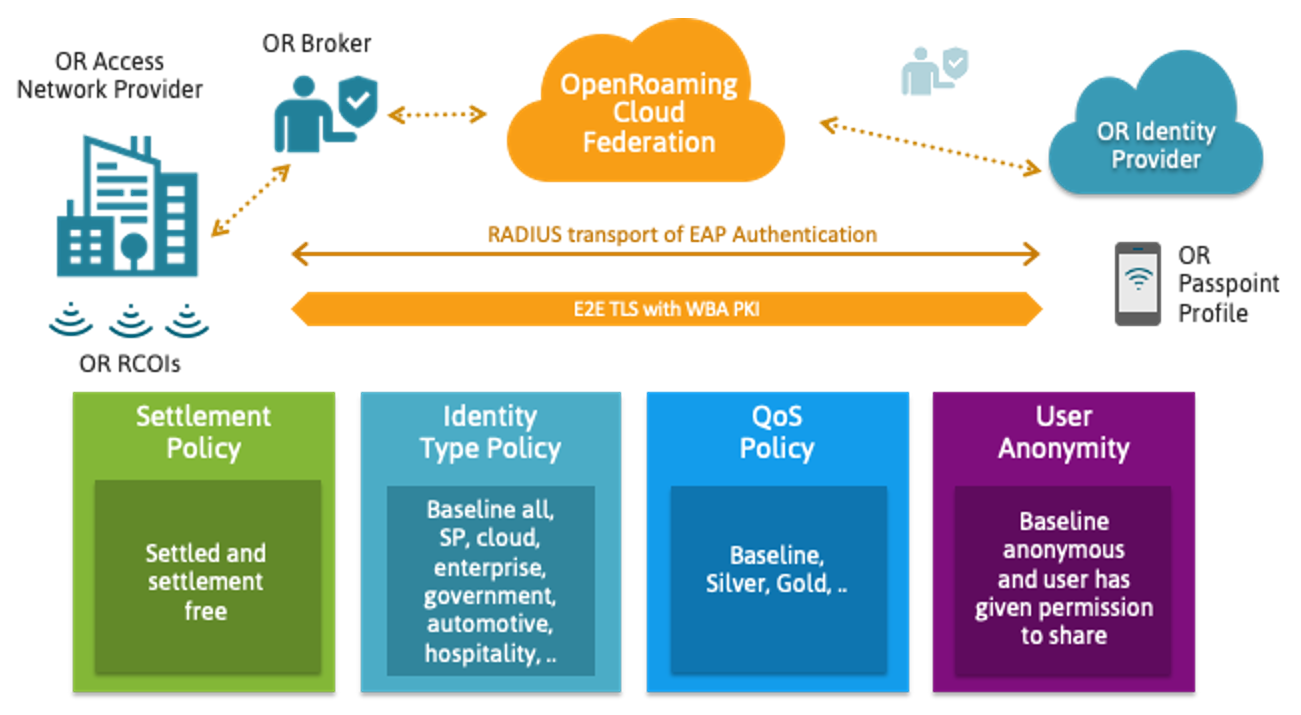
Wireless Broadband Alliance’s (WBA) recent standardization of OpenRoaming offers a different approach. The system is built on a cloud foundation. However, its real innovation is its use of a flexible policy framework. This enables the value-chains of individual participants to vary, while simultaneously opening up identity provision to a new set of stakeholders. Instead of being a capability uniquely attributable to conventional service providers, OpenRoaming enables cloud providers, private enterprises, device OEMs and even loyalty program providers to deliver the authentication service used when roaming. With this capability, we can significantly expand the addressable roaming use-cases, now enabling IoT device OEMs, vertical specific events providers and others to use their identities to support novel roaming scenarios.
Moreover, rather than assuming all access networks are monetized through usage fees, OpenRoaming recognizes that a significant number of wireless deployments are used to serve “guest users”. In these scenarios, the wireless network is monetized by supporting alternative value propositions; an improved retail experience in a shopping mall, a more efficient meeting in a carpeted office, a superior stay in a hospitality venue, or a better fan experience in a sporting arena.
Policy-Enabled Roaming
The core capability of the OpenRoaming federation enables the automatic matching between the policies defined by the individual identity providers with those defined by the separate wireless access providers. Importantly, if we determine in advance that there is no common policy between access and identity provider, the OpenRoaming enabled device will use standardized Passpoint™ capabilities to prevent the device from triggering an authentication exchange that would subsequently have to be rejected due to the policy mismatch. In contrast, where we can determine that there is a common policy, the OpenRoaming enabled device will automatically trigger an authentication onto the access network.
The access network then uses the same domain name system used to scale the web to dynamically discover the services offered by the user’s identity provider. It then uses the OpenRoaming Public Key Infrastructure to establish a secure connection to the identity provider and uses the connection to automatically authenticate the user using a standardized Passpoint authentication exchange.
In the first release of WBA’s OpenRoaming specification we have enabled policies to be defined based on:
- whether access is monetized through usage fees or provided on a settlement-free basis;
- the specific identity-type used, for example whether it corresponds to a conventional service provider identity or has been allocated by a cloud provider;
- the quality of service configuration of the access network; and
- the end-user agreement concerning use of personal identifiable information.
Continuing the OpenRoaming Evolution
WBA has used its Federation Task Force to bootstrap the definition of the various commercial, legal and technical OpenRoaming specifications. With this milestone completed, WBA is transitioning OpenRoaming from launch to full operations as a priority program.
I am tremendously honoured to have been selected by the WBA membership to chair the group that will drive the OpenRoaming program. Moving forward, we will continue to be driven by member input. Already we have a number of enhancements being discussed, from database APIs, through service level assurance to enhancements to include established clearing and settlement capabilities.
Summary
The shift of roaming from a premium to a utility service, the increasing focus on massive adoption of IoT devices, the tremendous scale forecast for private (5G) cellular systems, and the continued adoption of Wi-Fi to address vertical-value chains, are all trends that are driving the transformation of systems used to support roaming service. The OpenRoaming federation is set to revolutionize the adoption of roaming, bringing well established Passpoint™ based roaming to a new set of use cases, a new set of Wi-Fi hotspot networks and a new set of Identity Providers.
As the newly appointed chair leading WBA’s OpenRoaming Task Group, I encourage all venues, vendors, service providers and identity providers to join WBA OpenRoaming and revolutionize Wi-Fi usage around the world.
Learn how you can enable OpenRoaming with DNA Spaces






How did you get my permission to become a Cisco Partner? What is the site or App or Cookie that gave you permission to choose me? I am skeptical about this site and know nothing about the Cisco DNA Center. Is there security measures I can take. Thank you
Great insight – thank you!