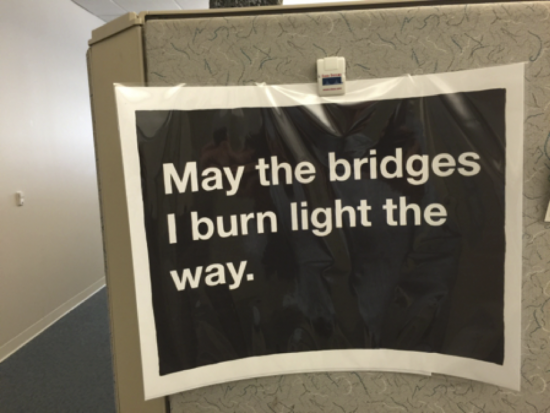
In a recent meeting I saw this meme posted in a cubicle:
How appropriate for a discussion on business executive moments of enlightenment. I have the opportunity to lead a line-of-business senior executive advisory board with members from the top manufacturing companies across the world.
Our recent board meeting focused on digitization in manufacturing where there were several opportunities for enlightenment, or Ah-ha moments. Not only did we discuss digitization, but supply chain visibility, OT/IT (Production Network and Enterprise Network) convergence, and manufacturing network security.
One moment of enlightenment we had was that manufacturing leaders really need to understand the risk that cybersecurity has on their business. The discussion of cybersecurity in manufacturing is too often transferred to technology oriented CIO’s and their network architects.
Many manufacturing executives think that person in charge of the IT enterprise network or the person in charge of the OT production network on the shop floor is taking care of security.
And they’re not.
This needs to be talked about in the boardroom.

Manufacturing leaders should discuss the impact of cybersecurity breaches on global business operations to make the threat real to senior executives. Security is not restricted to the four walls of a manufacturing company, but it extends to both your customers and suppliers as well. They should paint a picture of the threats in the factory – inadequately secured controllers, outside technicians performing routine maintenance, and the network’s connectivity to outside sources.
Here are 5 cyber security discussions you should be having with your board:
Factory Threats
Many board members have not considered the threats from equipment controllers that are not adequately secured or from factory equipment technicians attaching malware-ridden PCs to the OT network while performing routine maintenance.
Advice: Start with a formal evaluation of how your production network is architected as well as how it is being used.

Product Threats
Manufacturers need to prevent embedded chip sets that control cars, airplanes, production equipment/robotics, and other technology from being compromised. While one thinks naturally of a network based cybersecurity attack, the impact of an attack to change how a computer processor works is just as harmful, if not more.
Advice: You need to build security into your products, from product design through the end of life.
Production Networks vs. Enterprise Networks
IT is often unwilling to accept or manage risks associated with OT requirements, which stifles innovation. The security of cloud-based platforms is especially a top of mind subject now. The integration of the production network and the enterprise network must be engineered, and IT must present itself as a facilitator, not the gatekeeper it is today. The business value from combining these networks now presents a huge opportunity.
Advice: Foster open dialogs between enterprise and production operations as part of your daily operation, covering both business and technical conversations.

Risk Awareness and Safety
Supplier relationships are always changing, which creates constant security risks. The production team needs to talk to the IT team about these risks. Hackers who endanger OT are generally attacking endpoints (such as production controllers) in pursuit of intellectual property. Supply chain leaders must mitigate risks, develop a better relationship with IT, and address possible inquires.
Advice: Supply chain leaders need to articulate these risks in their strategic as well as their daily operational routines and make employees aware of the risks they could expose the business to.
Supplier and Customer Connectivity
Traditional connectivity between suppliers, customers, and manufacturers requires agreement from multiple IT departments. This is especially challenging when the supplier is required to purchase equipment from the manufacturer.
Advice: Professionals responsible for customer and supplier relationships should talk about cyber security and how to mutually address it as part of a normal contract negotiation.
A Final Word of Enlightenment
Our 2016 Cisco security report shows that enterprises are increasingly less confident that they have the technology and skills to manage attacks and security incidents. The report also found that the number of online attackers is increasing and the quality of the attacks is improving.
Manufacturing companies certainly lack the understanding and support of the cyber security threats from line-of-business executives. Quotes from top business executives support this view:
We have many unsophisticated problems, and we hear “we haven’t fixed the security problem so we can’t do (insert initiative)” The barriers to entry have protected us for over 100 years, and the fear of losing our IP is held up as a way to prevent progress.
I just spent $20M on a production line and I haven’t had one person talk to me about security. The production engineers never have these discussions with me and my team. They ran the wire to the panel, and off to the races you go.
In the end, Cisco and our advisory board has found that line-of-business senior executives must drive enterprise and production network security for their businesses. This includes both customer and supplier relationships as well. They must start these difficult discussions, and enlightenment will come by lighting the way and yes, perhaps burning some bridges along the way. Our teams have worked with Board of Directors and senior executive teams to make business security a reality for the competitiveness, safety, and continuity of their companies.
Do you really know how secure your business is?
Share your thoughts in the comments section below. To learn more, view our factory security resources.





Love the quote – and the post makes a very important point. So many have their heads buried in the sand, not wanting to deal with the fact that security and privacy issues span every part of the public and private sectors.
Thanks for the note Elizabeth. Although a technology company, our Business Transformation team are seeing manufacturing security show up in three ways: manipulation, disruption, and theft of IP. That seems to be the way to get the attention of business executives from a threat/risk point-of-view.
Peer-to-Peer Networking. First, it is great to see Bob Dean blogging again. His GMAB sessions provide great insights into the issues of manufacturing executives. Thus arises another technique to gain selling momentum – offering an update on what an executive’s peers are executing and being successful at. Experienced salespeople bring these productivity insights to their executive buyers. Rookie salespeople offer them up as conversation starters. For example, my colleague at Target discovered that their customer database was hacked via their air conditioning system…is that a vulnerability that applies to you? Salespeople have the ability to pick up emerging best practices, productivity insights, lessons learned and other vignettes from their peers. Bottom Line: By listening to how other Fortune 500 executives succeed, thoughtful salespeople enjoy regular customer conversations (without burning any bridges).
Jonathan! Always great to have tour support over all of these years. Thanks for the comments!
Great article. I like the comment, “They should paint a picture of the threats in the factory – inadequately secured controllers, outside technicians performing routine maintenance, and the network’s connectivity to outside sources.”. Its important to point out that many threats are unintentional – so physical security on the factory floor plays a key role here! Raising security to an executive level is important.
Thanks Scot for contributing to the thread!
HI Scot! Thanks for the comments. Our Business Transformation team at Cisco sees manufacturing shop floor security as a key area for businesses to manage threats and risk. A simple plant network architecture assessment will show areas of strength and vulnerability. We can then plan a phased approach to helping address those issues globally – but with the business executives full knowledge and support.