Take a trip with me, if you will, back to the turn of the 21st century – when “digital transformation” was but a gleam in our eyes. Back then, we barely had email at work. The internet was still kind of a novelty. And social media had yet to be invented. (How did we survive?)
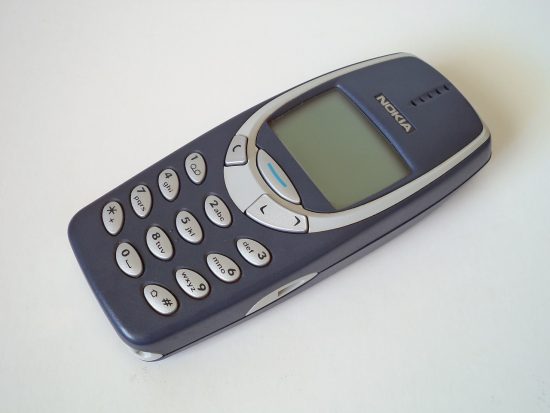
THIS was the highest-tech cell phone in the year 2000:
At the time, I worked as a Risk Manager for a professional liability (a.k.a. medical malpractice) insurance company. Among other responsibilities, my job was to advise our physician customers on legal and regulatory risks. And my phone was utterly lit up with calls about this new law called HIPAA. (It was officially passed in 1996, but because of the major operational shifts it required, organizations were given until April 2003 to comply.)
The most commonly asked question at the time had to do with the sign-in sheet at the front desk: Was having that in plain view a HIPAA violation?
Aw, weren’t we cute.
Nowadays, of course, our focus has shifted. We’ve mastered the basic tenets of HIPAA (I still remember the mnemonic device “TPO”: treatment, payment, operations), but we still worry about privacy breaches. Actually, we worry a lot more now, because unseen hackers are exponentially harder to control than a physical file folder. And although we love the internet, we don’t love the fact that breaches of protected health information (PHI) are posted on a website for the world to see.
The recent WannaCry attack was a cautionary tale for many in healthcare, even though very few in the US were affected. Ironically, the news broke during the HIMSS Privacy and Security forum, sparking deep concern among security professionals in attendance (who had just heard the day before that 75 percent of hospitals are living under the cybersecurity poverty line).
All of this only underscores the need for a hard-working, automated security solution, like Cisco’s Advanced Malware Protection (AMP) for Endpoints. Not only does it help detect, block, and remediate advanced malware across all endpoints, but it’s now also officially validated to meet the standards for HIPAA compliance.
That’s a big deal. As you know, it’s not easy to pass that test.
Check out the blog from my friends in security detailing this milestone, including the specific HIPAA security rules AMP for Endpoints meets–and exceeds.
I’ll just be over here, recalling a simpler time, and reminiscing about the utter freak-out that was Y2K (we survived, you guys!).





