Cisco AMP for Endpoints was recently the subject of a thorough technical review and test to validate that the solution satisfies requirements in accordance with the Payment Card Industry Data Security Standard (PCI DSS) version 3.2 and the Health Insurance Portability and Accountability Act (HIPAA) Security Rule. The Cisco Security Team is pleased to report that as a result of the testing, it was concluded that the AMP for Endpoints solution meets and exceeds PCI and HIPAA requirements. Organizations, regardless of size or industry vertical, can confidently deploy this solution knowing that not only will their compliance needs be met, but from a risk management perspective, that their endpoint security posture will improve.
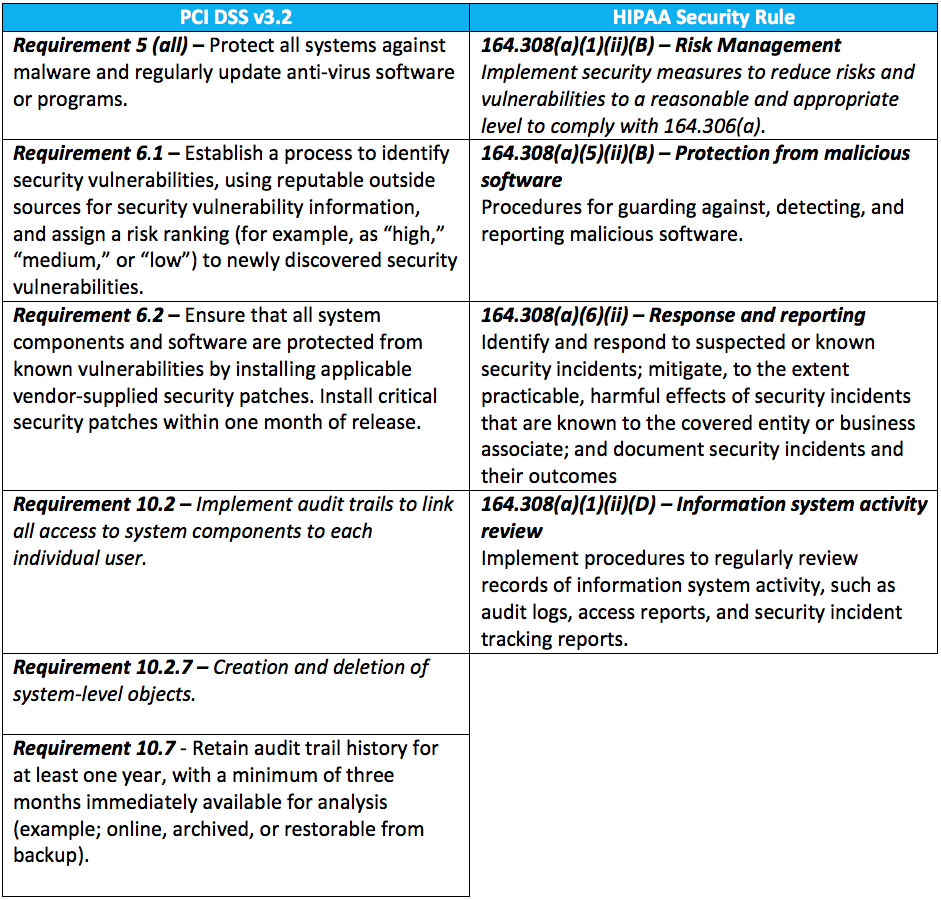
Cisco AMP for Endpoints meets and exceeds all of the following HIPAA and PCI requirements:
To learn more about the test and compliance validation, view the whitepaper here. For more information on Cisco AMP for Endpoints and how it can strengthen the security effectiveness of your organization, visit www.cisco.com/go/ampendpoint






Good to know,
Keep it up cisco !
Is AMP on the endpoint more effective than if already behind AMP running on an MX appliance?
Hi Bcesar, that is the beauty of a layer security architecture such as AMP Everywhere. Imagine if a malicious file was transferred onto an endpoint via an external storage media or while it was offnet (from the MX). AMP for Endpoints will detect it and if configured to, quarantine it. More importantly, that file identified by it’s file hash will now be known malicious to all security control points in the AMP Everywhere architecture; including the MX. Subsequent traversals of the file via network devices, such as the MX, will be blocked. See malicious once… block everywhere. The architecture can help contain the spread of malware to limit the scope of remediation. More information on AMP Everywhere can be found at: http://www.cisco.com/go/amp
Hi Bcesar
Agree with everything that Shyue Hong said.
With regard to “effectiveness”, the level of effectiveness really depends on what security mechanism you’re talking about (prevention/detection, detection after something already gets on the endpoint, or response) as well as what attack vector (network vs endpoint vs email vs web, etc.) When you deploy AMP for Endpoints, it is providing you the deepest visibility into file activity on the endpoint, hands down. And it covers you for prevention/detection upon initial file inspection, detection after something gets in, as well as response to quickly contain and remediate.
To see the level of visibility, context, and control that AMP for Endpoints provides, visit http://www.cisco.com/go/ampendpoint and click the “AMP in 5 Min”button at the top of the page.
Good to know !!!