It’s here.
Advanced Malware Protection (AMP) for Networks is now available in Cisco SD-WAN.
That means you’ll be able to sandbox and block standard, as well as polymorphic malware across the WAN, all from the Cisco SD-WAN console.
As the world’s largest networking and cybersecurity vendor, Cisco combines the most advanced SD-WAN with its industry-leading security portfolio for your campus and branch office needs. In addition, Cisco SD-WAN platforms, such as the 1000 and 4000 Series Integrated Services Routers (ISR 1K and ISR 4K) are purpose-built and enhanced with proprietary, embedded defenses to provide the most comprehensive SD-WAN connectivity and protection.
Robust SD-WAN Security
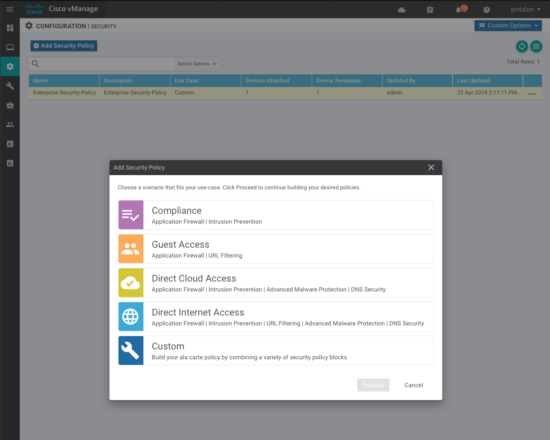
With the software release of Cisco IOS-XE SD-WAN 16.11, Cisco SD-WAN customers using ISR platforms gain access to the most advanced security services backed with Cisco Talos threat intelligence. These services include:
- NEW: Malware defense and sandboxing with Cisco AMP and AMP Threat Grid
- Enterprise firewalling with application awareness
- URL filtering and Umbrella DNS security
- Snort Intrusion Prevention (IPS)
- End-to-end segmentation across the WAN
- Embedded platform security, including the Cisco Trust Anchor module
Building on the Cisco SD-WAN Security Stack
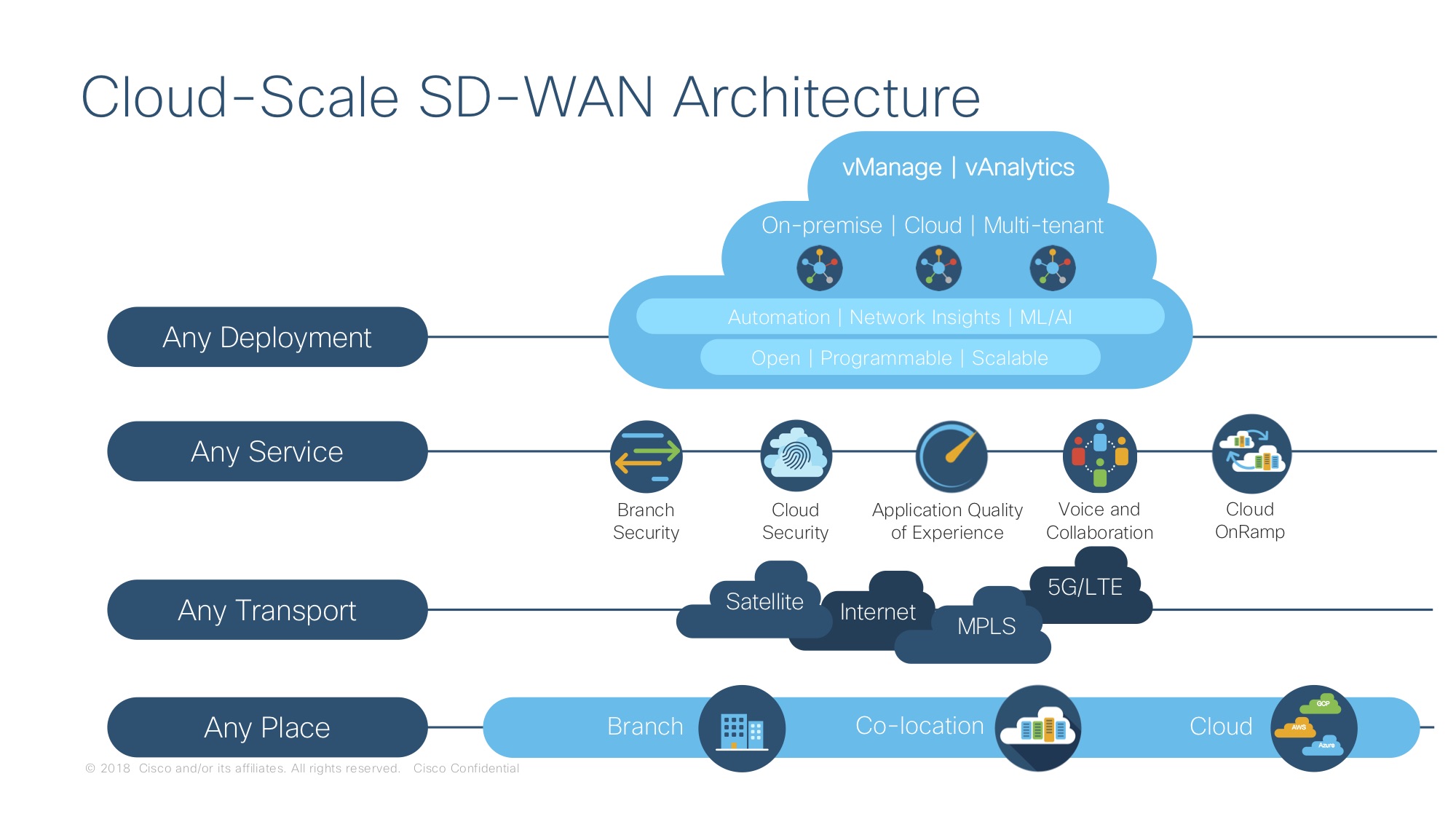
SD-WAN presents unique challenges for your network management and security teams. Branch offices transmit sensitive data like their core and campus location counterparts, yet modest branch office size and scattered geography make them difficult to secure with multiple point products. When branch locations begin using direct internet access (DIA) for cloud applications, enterprise risk increases further. Adding malware protection in these environments is critical.
Cisco SD-WAN allows enterprise IT teams the ability to layer security including malware protection at branches and core locations across the WAN with a few clicks. These capabilities help WAN locations identify, defend against and remediate a wide variety of threats.
AMP Understands Malicious Behavior
 Modern malware has evolved.
Modern malware has evolved.
Without the appropriate protections, detection and remediation in an SD-WAN environment is unlikely, exposing branch offices and the WAN to advanced threats such as data exfiltration and unauthorized encryption.
For network, security and IT operations teams, that means taking time to work across departments, correlating disparate tools to fumble through threats in hopes of preventing their expansion into other sensitive network areas.
That’s why AMP for Networks in Cisco SD-WAN uses integrated preventative engines, exploit prevention and the most intelligent signature-based antivirus to stop malicious attachments before they execute.
AMP understands malware. Together with Cisco Talos, AMP imbues your SD-WAN branch, core and campuses locations with threat intelligence from millions of worldwide users, honeypots, sandboxes, and extensive industry partnerships. In total, AMP identifies more than 1.1 million unique malware samples a day. At the first sign of malicious behavior in your core location or branch, AMP in Cisco SD-WAN automatically blocks the threat and protects users across your entire WAN.
Interested in learning more?
Try Cisco SD-WAN for yourself today.
Update: This announcement has been corrected to reflect accurate file-less functionality. File-less malware analysis is available in AMP for endpoints, and is not a feature available in AMP for Networks.






AMP for Networks calculates the SHA of the file as the file passes through the appliance, and the disposition is returned indicating if the file is good, unknown, or malicious. How does AMP for Network operate for fileless malware, where a SHA cannot be calculated? Please explain, thanks.
For fileless maleware you would need AMP on the clients , IPS could perhaps detect some patterns.
and for https/tls transport you would need ETA.