The Cisco interns are back at school now, but they shared their story with us after their experience. This post is compiled from Needhi Parekh, Tanishq Sandhu, Nabid Farvez, Shruthi Santhanam, Jamil Kassam, and Joseph Lee. Thank you for sharing your Cisco High story with us!
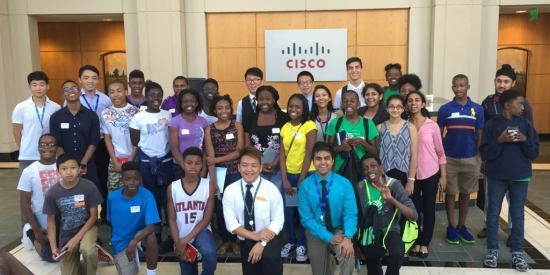
The Lawrenceville Fifteen. They were 15 upcoming junior and senior high school students from the Lawrenceville, Georgia area who came together for a STEM (Science, Technology, Engineering, Math) internship at Cisco this past summer.
Most people don’t start thinking about internships until college, and even then, finding the right intern program can be tough. These high schoolers were taking on this tough task even earlier.
After a great summer together, they wanted to share their reasons that Cisco was the right choice for them.
- The Culture: You’ll see Cisconians talk about #WeAreCisco a lot. The reason we proclaim it with pride is because the culture pulses through our veins! Cisco employees are proud to work with each other, and do do work that matters. We can even recognize each other through a peer recognition program. That’s neat stuff!
- Acceptance: At Cisco, everyone is accepted as a part of a greater team, yet encouraged to be unique. We value a diverse team because our differences drive innovation. We have big goals because we know that together we can reach them. We win together and build each other up.
- Leadership: The leadership at Cisco definitely has our back. As interns or employees. They want everyone to have the best experience. There are vast technology resources that allow for constant communication. Managers seem to always have an “open door.” Plus, they want us to have a little internship fun, too, and plan activities to encourage that.
- We’re a Team: It’s almost as close as a family. On the first day of our internship, it’s a little weird not to know anyone. But soon, we’re connected in more ways than we thought. It starts with handshakes and smiles, and becomes hugs and bonds. We helped each other up the ladders at Treetop Quest and cheered as a teammate bowled a strike. We really are the #WeAreCisco tribe.
- Constant Learning: You’ll never stop learning at Cisco – from just how to act in a professional work environment to how to build a personal brand to how to use all the great technology. This is stuff you won’t learn anywhere else. For example, you’ll see equipment that Material Scientists use to create solutions for Cisco products, or how Cisco is redefining “flat-screen TVs.” Plus, you’ll have mentors that will help you navigate through all of it.
- Feedback: When you’re just starting out, feedback can be hard. But at Cisco, you’ll learn how to accept it and grow. You’ll see how important it is to implement the advicee you’re given, and how you’ll be a better worker, and person, because of it.
- Unlimited Growth: You’ll be exposed to different people, different divisions and different technologies. You’ll learn what a product manager does verses a sales engineer verses a marketing person. You’ll learn from all of them. There’s never a “stupid question” because there are none. Ask as many questions as you’d like.
- Giving Back: Cisconians truly love giving back to our community. As an intern team, we hosted a STEM day for elementary and middle school students. We helped them learn about all the cool things we were doing at Cisco, to encourage them to look at technology as a career option. It was an amazing and something we will not soon forget. We were young minds being shaped, but we were also shaping young minds.
Our best advice after our summer? Definitely it’s to intern at Cisco. You’ll be seeing us again sooner than you think.
Want to join an awesome team? We’re hiring! Apply now.
Would you like to participate in Cisco High? Find out more information on how you can join us here!