We live in a time when lines in IT are blurring, and the line between security and network operations is just one example. When organizations are breached, their network is imperiled and business can suffer. Resiliency, performance, and threat defense are increasingly intertwined. No one understands this better than Cisco, with our decades of network leadership and our innovation in security.
Cisco is enabling our customers to maintain network performance while they keep their data safe. Our latest Firepower 2100 Series NGFWs are a testament to this, delivering business resiliency through superior threat defense and unmatched price-performance. With Firepower 2100 Series, enabling advanced threat functions does not mean compromised performance – you can maximize throughput while maintaining robust threat inspection.
Business resiliency is job one for network operations teams – but they can’t do their jobs if security is a choke point. On the Cisco Firepower 2100 Series, when you enable advanced threat functions, they won’t become a network bottleneck like competitors. Cisco’s innovative dual, multi-core CPU architecture and software optimizations maximize firewall, cryptographic, and threat inspection performance simultaneously.
From preliminary testing, we’re seeing minimal impact on large packet firewall throughput when enabling intrusion inspection. In fact, with IPS fully enabled, we see with large packets less than 1% throughput degradation to network traffic. Contrast that with the typical 50% or greater impact in competing designs. With Cisco’s design, you don’t have to choose between security and network performance – you get both!
A ‘No Compromises’ Security Architecture
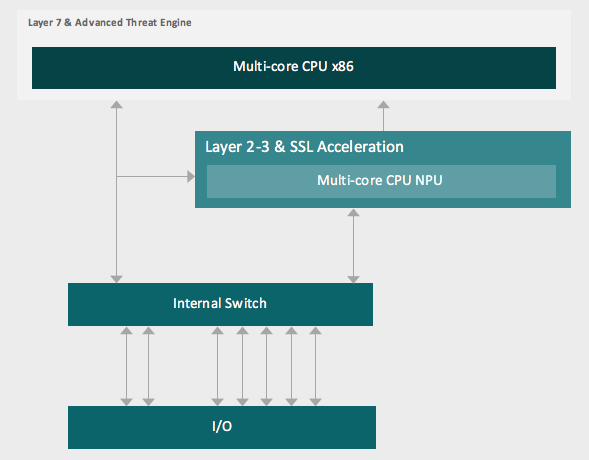
Key to the performance sustaining abilities of the Firepower 2100 Series is a dual, multi-core CPU architecture and software optimization that enables:
- Sustained throughput performance when threat functions are enabled vs. competing designs
- Flexibility and future-proofing versus ASIC-based designs that inhibit the ability to add new defenses and functions
- Fast path accelerates flows not requiring threat inspection, further enhancing performance through the appliance
By applying purpose-built processing for the tasks at hand, the Firepower 2100 Series NGFWs optimize performance and threat protection, without burdening network operators to architect around security bottlenecks. This reduces the need to overprovision and fosters deeper inspection levels than otherwise might be possible.
The design employs Intel multi-core CPUs for Layer 7 threat inspections (app visibility, intrusion detection, URL filtering, malware and file inspection, user identity, etc.) and a combination of merchant and a Network Processing Unit (NPU) for layer 2-4 traffic (stateful firewall, NAT, VPN-SSL encryption/decryption, and more.).
Traffic first traverses the NPU, and may be blocked based on access controls, obviating the need to inspect further. Flows requiring advanced inspection are copied and sent to the x86 complex – and flow handling is optimized regarding required inspection services, utilizing security group tags as one method to make this determination. In addition, a ‘fast path’ option allows intelligent re-routing of trusted traffic dynamically.
If it isn’t obvious by now, Cisco Firepower NGFW isn’t just another firewall. Across the entire family – and now the new 2100 Series – Cisco Firepower NGFW combines our effective security architecture with the power of the network for superior business resilience and protection.
Watch the video below, visit the Cisco Firepower 2100 Series NGFW product page, and take a virtual tour to learn more about the various form factors, speeds and feeds, and more.
https://youtu.be/R8Do7Q3FlB8






Hi David, I am interested in the findings of minimal impact on large packet firewall throughput when enabling intrusion inspection, SSL decryption, and other functions. This seems to be different than what we have seen on Cisco provided performance testing and real-world experience.
Throughput has typically gone down significantly. The 4110 for example starts at 20 Gbps firewall throughput; is reduced to a Cisco estimated 2.8 Gbps with AVC + IPS + URL with 450 byte packets.
With tests showing that the performance can drop by up to 80% with SSL/TLS decryption.
Also, enabling File Identification leads to a performance degradation of around 22%, enabling cloud
malware lookup and blocking results in a degradation of around 40% and enabling File Sandboxing leads to a total
degradation of around 50%.
Thank you, Jason
The performance numbers cited in our Firepower 2100 Series datasheet (you can access this at cisco.com/go/firepower2100) are based on ‘large packet’ 1024 byte tests enabling NGIPS functionality on top of the stateful firewall and application visiblity (AVC) functions – differing packet sizes will most certainly have different performance characteristics. Smaller packet sizes require added processing, so you can expect lower throughput levels. We provide performance sizing guidance via our Global Security Sales Organization and reseller partners. Please rely on the datasheet, performance guidance and counsel of your Cisco representative when sizing to your requirements.
wrt to jason’s comments it is indeed remarkable that you have created a NGFW IPS that has so little impact on through traffic. Im sure it helps that you have split the traffic up into lower order which could get blocked first and upper level which get checked second.
Would love to see the updated NGIPS/NGFW Performance Whitepaper on these devices. Any idea when that will be available?
Performance testing with AMP is underway – we will make available sizing guidance based on this prior to product availability in April. In addition, for further details on architectural differences see the blog by Dennis Perto entitled “Firepower 2100 – The Architectural “Need to Know” – find this at https://blogs.cisco.com/perspectives/firepower-2100-the-architectural-need-to-know