Ten years ago, I remember driving around my neighborhood with a laptop, wireless card, and an antenna looking at the Service Set Identifiers (SSID) of all the open wireless networks. Back then, a home user’s packets often flew through the air unencrypted with nary a thought to who might be listening.
As a protocol, Wireless Fidelity (WiFi), has continually improved (IEEE 802.11) and today it is the preferred communication channel for a multitude of home devices including video game consoles, cameras, streaming video devices, mobile phones, tablets, and list goes on. As October is National Cyber Security Awareness Month, we outline typical WiFi risks and share sensible precautions.
 In my last three homes, the Internet Service Provider (ISP) installation technician arrived with a cable modem that included four Ethernet ports and native WiFi default enabled. In each case, the technician explained that I could manage the cable modem through the settings webpage. When I inquired about management authentication credentials all of the technicians told me that passwords were not enabled by default, which naturally caused some consternation due to the obvious security implications.
In my last three homes, the Internet Service Provider (ISP) installation technician arrived with a cable modem that included four Ethernet ports and native WiFi default enabled. In each case, the technician explained that I could manage the cable modem through the settings webpage. When I inquired about management authentication credentials all of the technicians told me that passwords were not enabled by default, which naturally caused some consternation due to the obvious security implications.
It turns out that most ISPs will provide a modem without WiFi capabilities upon request. You can also request that a WiFi enabled modem be converted to bridge mode which will allow you to attach and manage your own WiFi access point (AP) without worrying about conflicts.
 When purchasing a WiFi AP, it is important that the device supports WiFi Protected Access II (WPA2) and does not include WiFi Protected Setup (WPS). Prior WiFi security systems like Wired Equivalent Privacy (WEP) contain vulnerabilities that allow unauthorized network access to even the most non-technical attackers using freely available tools. One of the most popular wireless tool suites is included in BackTrack – a custom Linux distribution – which if pointed at your network by unscrupulous individuals will likely mean trouble.
When purchasing a WiFi AP, it is important that the device supports WiFi Protected Access II (WPA2) and does not include WiFi Protected Setup (WPS). Prior WiFi security systems like Wired Equivalent Privacy (WEP) contain vulnerabilities that allow unauthorized network access to even the most non-technical attackers using freely available tools. One of the most popular wireless tool suites is included in BackTrack – a custom Linux distribution – which if pointed at your network by unscrupulous individuals will likely mean trouble.
A determined attacker with plenty of time will likely crack any home WiFi network just due to the nature of WiFi. When you plug an Ethernet cable into your computer, the only way an attacker can monitor your traffic is if they are able to tap the physical layer (unlikely given that most networks use fiber-optic cables making it largely infeasible), or if they are able to mirror a network device port at the ISP Central Office (CO) or smaller Point of Presence (PoP) (also unlikely given the inclusion of physical crime and substantially increased likelihood of detection.
WiFi, on the other hand, is public by nature and therefore provides continuous meta-data and a larger attack surface. Given this reality here are a few tactics for slightly decreasing the attack surface when configuring your AP:
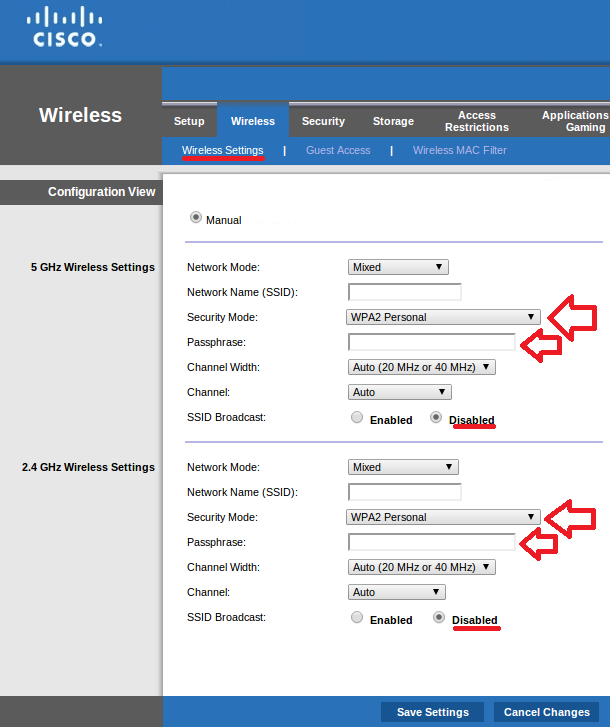
1. Turn off SSID broadcasting.
Why broadcast the existence of your wireless network? Strangers don’t need to know your SSID and configuring wireless devices on the network only requires a few more steps. Mind you, an attacker can still discover your SSID with free tools even when it’s not broadcasting, but this is an easy way to gain a bit of SSID privacy.
2. Use a strong password with WPA2.
Due to possible dictionary or brute force cracking attacks on the WPA2 pre-shared key (PSK), it’s important to use a long (over 20 characters) non-dictionary PSK (password). Unfortunately, attackers will again use freely available tools, like Aircrack-ng, to crack your WPA2 key if they can so beef up that PSK.
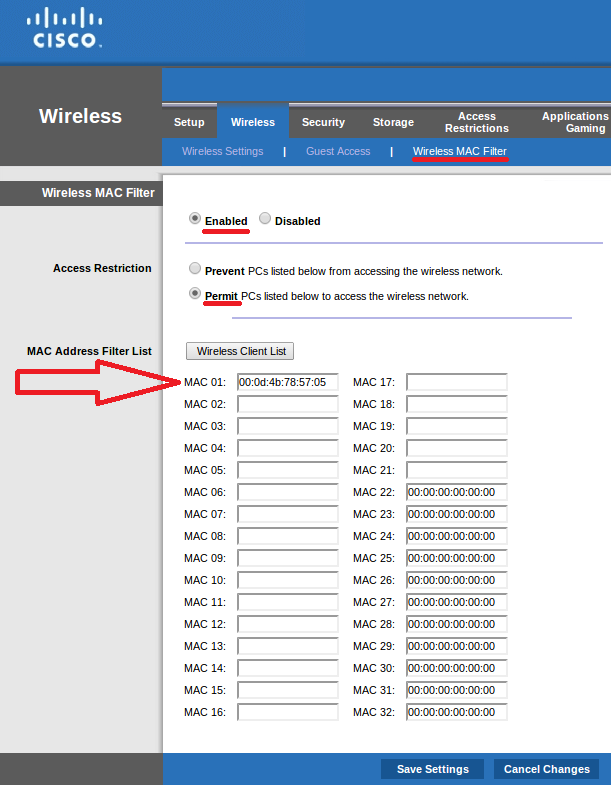
3. Enable MAC address white listing.
Every network device contains a unique address that is stamped by the manufacturer. Restricting access to your wireless network by MAC address is not fool proof as valid MAC addresses can be easily sniffed and subsequently spoofed, but it does raise the bar (even if just by inches).
Now that you’re thinking about home WiFi security, let’s move on to mobile WiFi security. When you’re out and about and your phone or other wireless device is connecting to APs how do you trust the AP owner? If an attacker turns his laptop (or even phone) into a wireless AP and names the SSID something benign, now you’re connected to a rogue AP and handing a threat actor your traffic and associated authentication credentials.
A rogue AP doesn’t require über technical chops to set up, and when done in concert with SSL Strip, an attacker will steal your passwords regardless of whether the website you are visiting is using Secure Sockets Layer (SSL). Thus, if you travel frequently and are forced to use random wireless networks, think about investing in a monthly virtual private network (VPN) service (or use an employer’s if available).
Lastly, as recently reported, if you use an iPhone with WiFi enabled it is leaking your recent location to anyone who cares to listen. Your iPhone doesn’t just broadcast recently visited wireless access point SSIDs; it also broadcasts the associated MAC addresses for any AP in the recent vicinity of your iPhone. Your phone’s wireless AP history may go back days, and practically speaking, this means that your daily movements may be trivially tracked.
If you want to try this yourself, there are plenty of tools ready to assist, including Kismet or Wireshark. For maximum effect, buy an antenna like the USB Yagi and then fire up any of the aforementioned tools.
You will be looking for iPhone probe requests. If you use the Yagi Antenna you will have no problem picking these up. A specific Backtrack application called “easy iPhone” uses a filter to identify iPhones within a packet capture (PCAP). If you can’t spot the probe requests in real time, you should save the PCAP and subsequently use Ngrep to identify them. The requests will contain the AP SSID and MAC address that the iPhone is searching for.
An even easier solution for cataloging probes and mapping them is iSniff-GPS – a useful application that visualizes iPhone data from imported PCAPs. It was officially released last year as a “passive sniffing tool for capturing and visualizing WiFi location data disclosed by iOS devices.” The easiest solution to avoid iPhone tracking is to turn off WiFi when it’s not being explicitly used, plus you will save some battery life. This is also true for Android devices that experience their own WiFi vulnerabilities.
In light of National Cyber Security Awareness Month we encourage everyone to be aware of the risks inherent in WiFi and enjoy being mobile.








Very good blog Levi. Glad that you are part of the blog team at Cisco.