In an earlier blog, we discussed the importance of a visibility-driven approach to Next-Generation Firewalls (NGFWs) and the need for capabilities that offer full visibility and contextual awareness into everything on networks since we know you can’t protect what you can’t see.
In addition to offering an unprecedented network visibility foundation, a NGFW must also be threat-centric to stop advanced, multi-vector threats, both known and unknown.
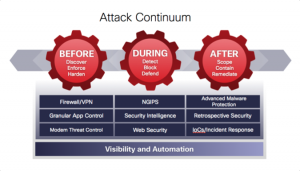
This means offering integrated threat defense for better control to combat these attacks across the attack continuum—before, during, and after an attack.
In complex environments, delivering integrated threat defense means ensuring that best-in-class capabilities, such as third-party tested and market-leading Intrusion Prevention Systems (IPS), Advanced Malware Protection (AMP), and URL filtering work together to protect against threats coming from multiple vectors.
Other NGFWs have not offered best-in-class network security capabilities in their devices, but rather, rudimentary versions of them. In addition, these solutions are poorly integrated and cannot share intelligence between security layers, making advanced threat detection and remediation difficult, if not impossible.
 Threat-Centric = Integrated Threat Defense Across the Attack Continuum
Threat-Centric = Integrated Threat Defense Across the Attack Continuum
Integrated threat defense integrates across a complete range of security layers detailed in the diagram.
Layering these capabilities together with intelligence and contextual awareness between security layers across the network and endpoint enables users to detect and protect against multi-vector threats.
These threats are often difficult to detect since they combine multiple threat characteristics that bypass traditional security measures (for example, a threat can originate from a malicious IP address, propagate through risky application, and contain a zero-day threat).
Cisco ASA with FirePOWER Services Delivers Superior, Multi-layered Protection
NGFWs must now be adaptive and threat-focused with superior threat protection across the full attack continuum. Cisco ASA with FirePOWER Services integrates trusted ASA firewalling, granular application visibility and control (AVC), reputation- and category-based URL filtering, AMP, and Next-Generation IPS (NGIPS), to provide comprehensive protection from known and advanced threats.
Enterprise-class granular AVC, oversees 3,000+ applications and uses risk-based controls that invoke custom-tailored IPS threat detection policies. Industry-leading FirePOWER Next-Generation IPS provides comprehensive threat prevention and full contextual awareness, as we have discussed in other posts, to detect and stop multi-vector threats and automate a defense response. Its reputation- and category-based URL filtering offers comprehensive alerts and control over suspect web traffic, and enforces acceptable use policies on hundreds of millions of URLs in over 80 categories. Open source integration with Snort and OpenAppID enables access to community resources and allows customers to easily customize security to address new and specific threats and applications quickly.
AMP is another threat-centric feature NGFWs must provide. In our case, we provide industry-leading security effectiveness in stopping advanced malware, enabling organizations to discover, understand, and stop emerging, persistent threats missed by traditional security defenses. Given the rapidly evolving threat landscape, “point-in-time” technologies attempting to fight malware, such as sandboxes or antivirus, are only one feature of an advanced malware solution, as malware can evade these defenses. Cisco ASA with FirePOWER Services is the only NGFW that offers more than mere point-in-time detection against advanced malware, also offering continuous analysis, retrospective security, and multi-source Indicators of Compromise (IoC). Retrospective security specifically provides the ability to “go back in time” to identify, contain, and remediate malware that initially evades defenses, filling an important gap existing in point-in-time products. These capabilities are foundational components of the architectures organizations must have in place as they adopt cyber resilience strategies.
When considering threat-centric network security, it is vital to understand how devices fare in third-party testing to understand if they are market-leading—Cisco brings extensive leadership in threat and malware security effectiveness. According to NSS Labs, FirePOWER delivers superior threat protection and the best ‘value.’ The NSS Security Value Map (SVM) shows that FirePOWER appliances routinely deliver leading threat effectiveness, up to 99 percent, with the lowest total cost of ownership (TCO) per protected Mbps, besting many well know next-generation providers. AMP was also recognized for delivering leading security effectiveness and TCO in recent Breach Detection System testing conducted by NSS Labs – besting established sandbox providers. For several consecutive years, these technologies have consistently achieved top performance results from NSS Labs for their exceptional protection, security effectiveness, performance and TCO.
With Cisco’s unique approach, all the solution parts know about each other; the firewall knows about the NGIPS and its policies, the NGIPS sees data coming through the firewall, and the malware engine correlates its events with the IPS events. This integration even extends to correlating Indicators of Compromise across endpoints and networks—no other solution provides this comprehensive capability.
Cisco ASA with FirePOWER Services provide administrators with the integrated threat defense required to protect organizations from evolving threats. The final blog in the series will discuss how this threat-centric platform also meets the third NGFW Platform requirement—platform-based.