It is not uncommon to see an anti-spam system catch >99% of the spam passing through it. Most of the best anti-spam systems catch >99.9% of spam. In this environment, spammers try just about anything to evade spam filters. Some spammers believe that blasting at high volume is the key to success. Others believe complete randomization of the message headers will confuse the anti-spam system. Still others take a minimalist approach, sending only a URL in the body. As anti-spam systems close gaps in their coverage, spammers are forced to find new tricks (or resort to variations on old tricks). It’s an arms race.
 One spam technique in particular is attracting more and more spammers. This technique is known in the email industry as “snowshoe” spam. Snowshoes are footwear that allows a person to walk over deep snow by distributing their weight over a larger surface area, thus preventing the wearer’s foot from sinking. But what do snowshoes have to do with unsolicited bulk email? In the email world “snowshoe” spam is unsolicited bulk email that is sent using a large number of IP addresses, and at a low message volume per IP address.
One spam technique in particular is attracting more and more spammers. This technique is known in the email industry as “snowshoe” spam. Snowshoes are footwear that allows a person to walk over deep snow by distributing their weight over a larger surface area, thus preventing the wearer’s foot from sinking. But what do snowshoes have to do with unsolicited bulk email? In the email world “snowshoe” spam is unsolicited bulk email that is sent using a large number of IP addresses, and at a low message volume per IP address.
Cisco’s worldwide sensor network records details about a substantial quantity of spam. We analyze this large dataset for trends among senders. Below is a breakdown of spam by sender type. Note that the volume of snowshoe spam has more than doubled since November 2013.
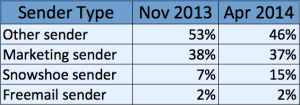
Spam broken down by Sender Type
What does a typical snowshoe campaign look like? Let’s follow just one simple example to get a feel for how a typical snowshoe operation is setup. A piece of spam with the Subject “Les Jours Oh : jusqu a -50% sur la mode et la deco” was sent the morning of May 20, 2014, from the IP address 5.135.21.191 to a SpamCop spamtrap. At the time, that IP address also appeared on the Spamhaus CSS list—a DNSBL specifically set up for blocking IP addresses used in snowshoe spam.

Below is what the IP address looks like in the SpamCop admin interface.

That IP address has only one complaint—the message that was sent to the spamtrap. However, check the section labeled “Other hosts in this block with spam reports.” The number in parentheses is the number of recent spam complaints. You can see there are a lot of other IP addresses in this /24 block that have only one spam complaint. In fact, these IP addresses all belong to different hosts operating under the same domain “dim425.com”. Looking at the domain whois for “dim425.com”, we can see the registrant is a company by the name of “RAYPROMAILING”.

DomainTools offers some online tools that are quite effective at aggregating domains registered under a specific registrant or registrant email address. A Reverse Whois check on the Admin/Technical contact email address shows six domains all registered to the same email address, “wwcq7g85dfe9b5gvjq4g@r.o-w-o.info”, including some very similar domain names such as “dim424.com” and “dim426.com”. A separate Reverse Whois check against the Registrant’s name “Yann Hericotte” reveals 80 domains potentially belonging to the same individual…a fact that can be verified in whois.
Some of Yann’s domains were registered very recently, and have yet to be deployed in any email campaigns. With RAYPROMAILING’s demonstrated history of poor email list practices, and with words such as “offres” and “promo” appearing in some of the domain names, it doesn’t exactly inspire confidence that these domains will be used for legitimate purposes.
A search on RAYPROMAILING’s domains in passive DNS reveals that many domains, including the domain used to send spam to our SpamCop spamtrap, possess a full /24’s worth of Message Transfer Agent (MTA) hosts—definitely bulk email sending infrastructure.
By virtue of its highly distributed nature, snowshoe spam is designed to evade per-IP and per-domain reputation metrics. Less advanced anti-spam filters may be fooled by tactics such as this, but Cisco Anti-Spam technology is not. By correlating together different pieces of the spammers’ infrastructure we are able to map out the associated domains, email addresses, IP addresses, and avatars on which snowshoe spammers rely. There is no place for them to hide.






