Every month, the Threat Grid development team brings you new features and capabilities in the Threat Grid cloud. After the significant benefit brought to our users by the integration of Cisco Threat Response and the Casebooks feature in the spring, we didn’t rest – we continued to bring new innovations and development, delivering some exciting additions that customers have been asking for with increasing interest. The below are the highlights of the new features and capabilities introduced over the summer. We’re happy to have recently brought you the following:
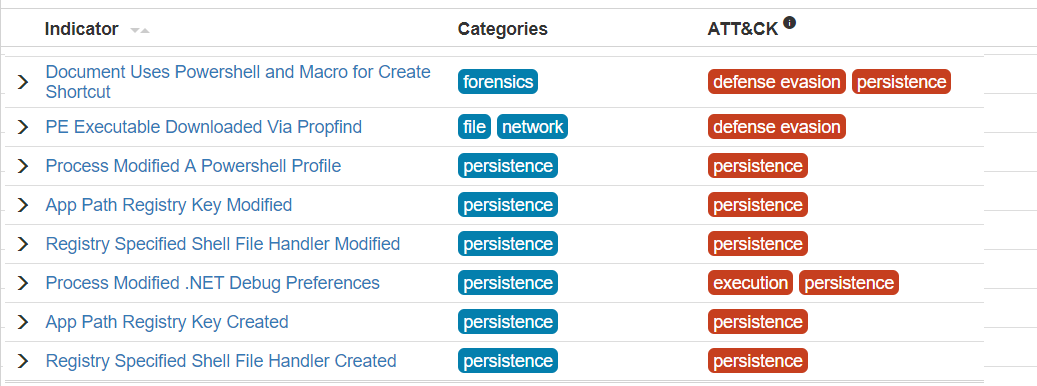
Mitre ATT&CK data
Mitre’s Adversarial Tactics, Techniques & Common Knowledge (ATT&CK) is a dictionary and a data model for recording and understanding adversary behavior. It allows automated transfer and operationalization of codified TTP information for response, detection, and potentially attribution. These values are tied to behavior indicators and appear in the indicators dictionary, as well as in both the individual sample analysis reports and the downloadable analysis data.
For more information on ATT&CK, see the Mitre ATT&CK page.
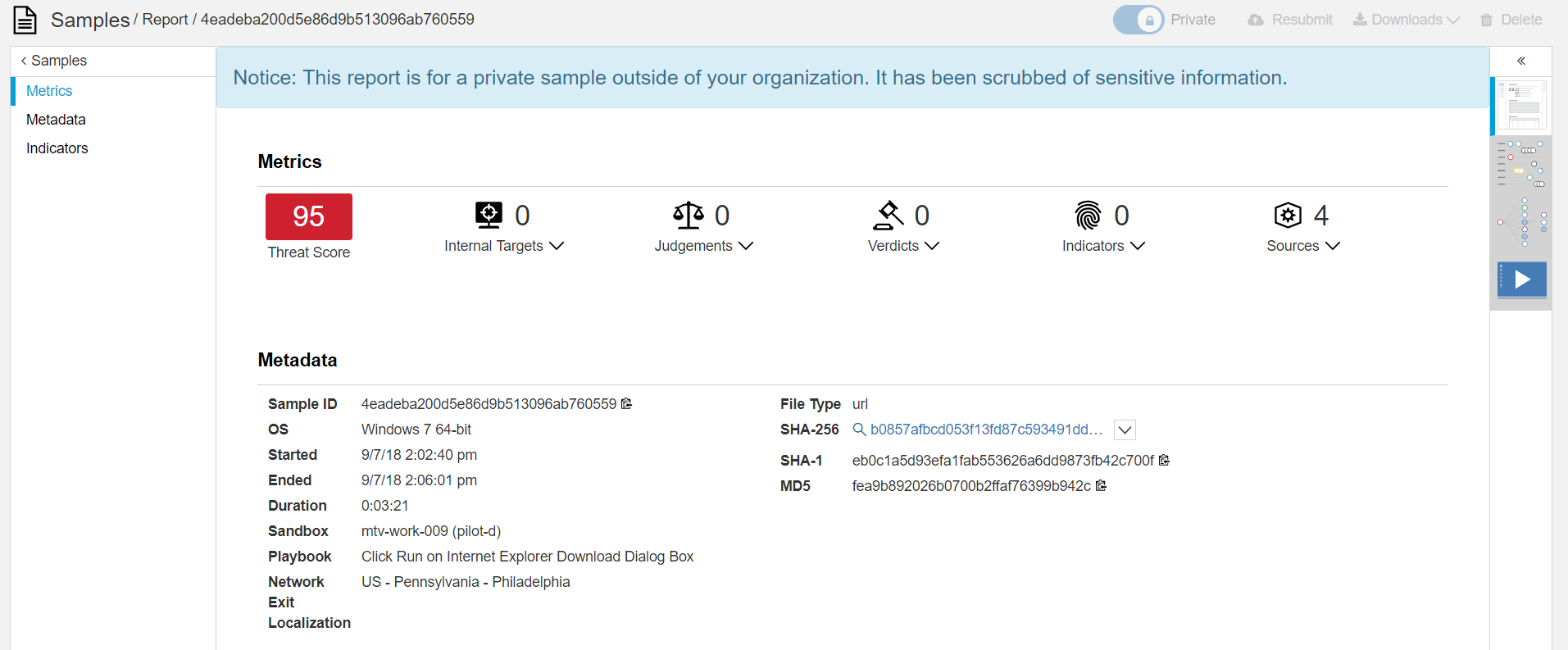
Scrubbed Reports
One of Threat Grid’s main strengths is its cloud-based nature – all customers can benefit from the submissions of all other customers. However, there are obvious privacy concerns that arise from submitting one’s files to the cloud. We have struck a balance between respecting – and enforcing – the privacy requirements of our customers and maximizing the benefit they can get from each other’s submissions. We now offer scrubbed reports on private files. These reports omit any identifying information – even the filename – and do not provide any means to download or otherwise view the file contents, but do show the hash, metadata, and associated Behavior Indicators. In the example below, note that the download and resubmit options are disabled, and that only the metadata and indicators are available.
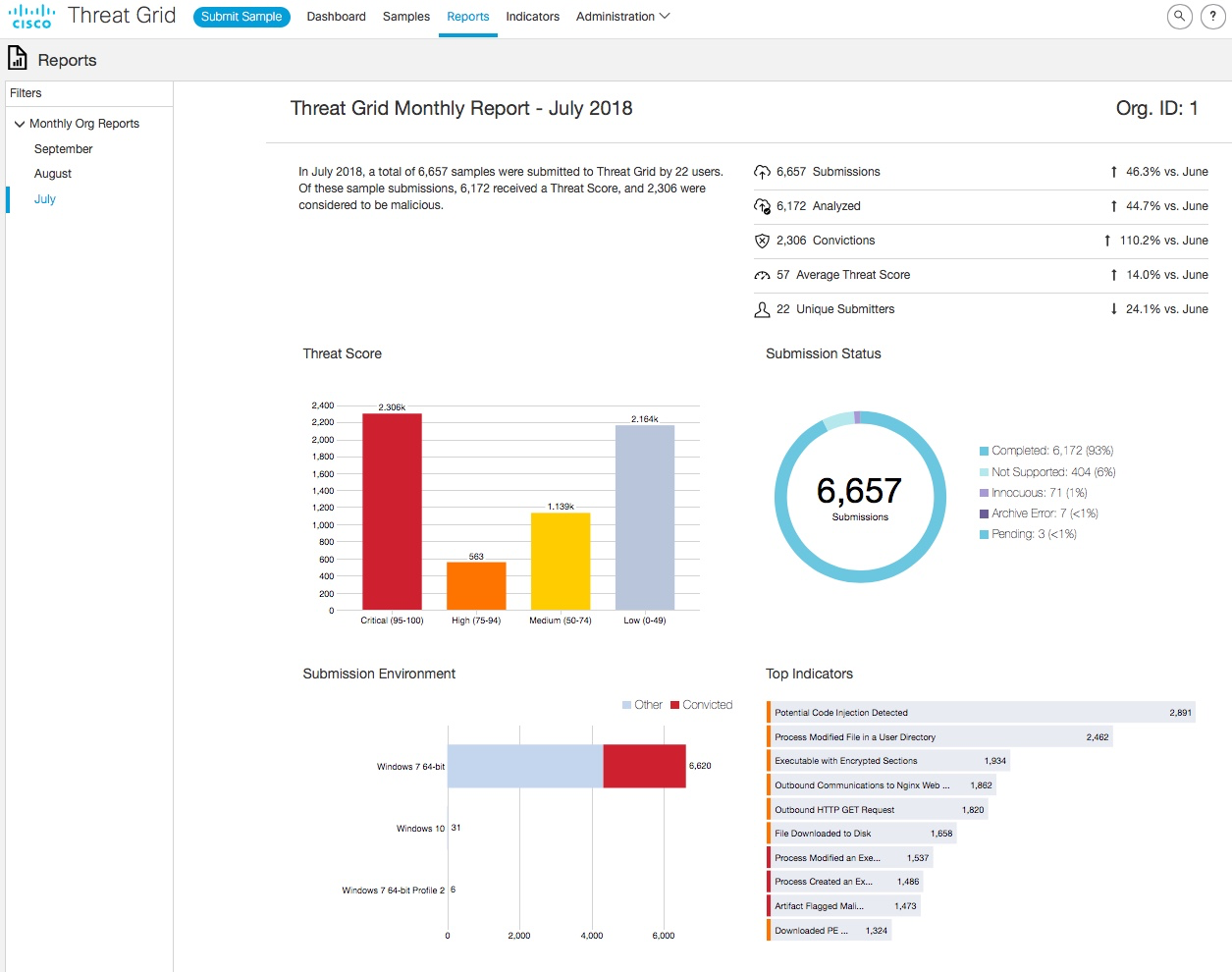
Monthly Organization Reports:
Now users can see, at a glance, how their organization has used Threat Grid over the past month; where the samples came from, the breakdown of the resultant threat scores, and more. The dashboard already allowed a quick visual summary of the last 30 days of usage, but these reports allow you to easily view each month at a time and see month over month trends.
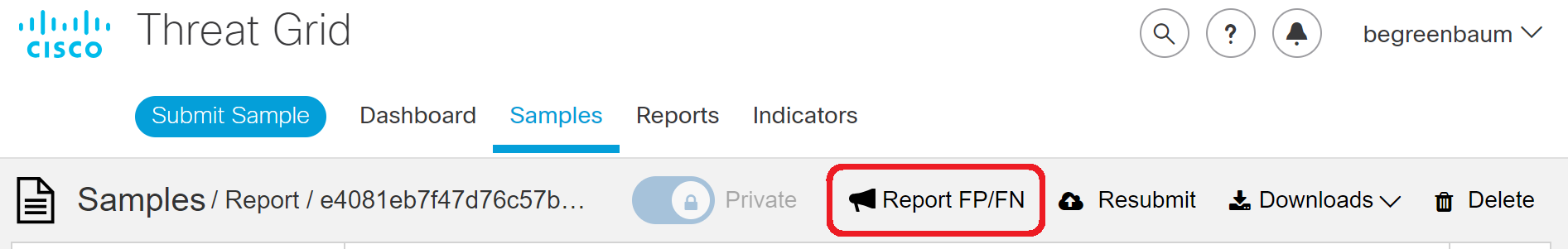
False Positive / False Negative reporting
These new controls in the Analysis Report view allow users to quickly and easily submit concerns to Cisco’s Research and Efficacy (RET) team for further review. Threat Grid makes decisions based on sample characteristics and behavior alone – and sometimes context matters. Additionally, the automated analysis errs on the side of protecting users from false positives, which can on rare occasions lead to the opposite, a false negative. Users will find this an efficient way to get concerns about potential misclassifications addressed.
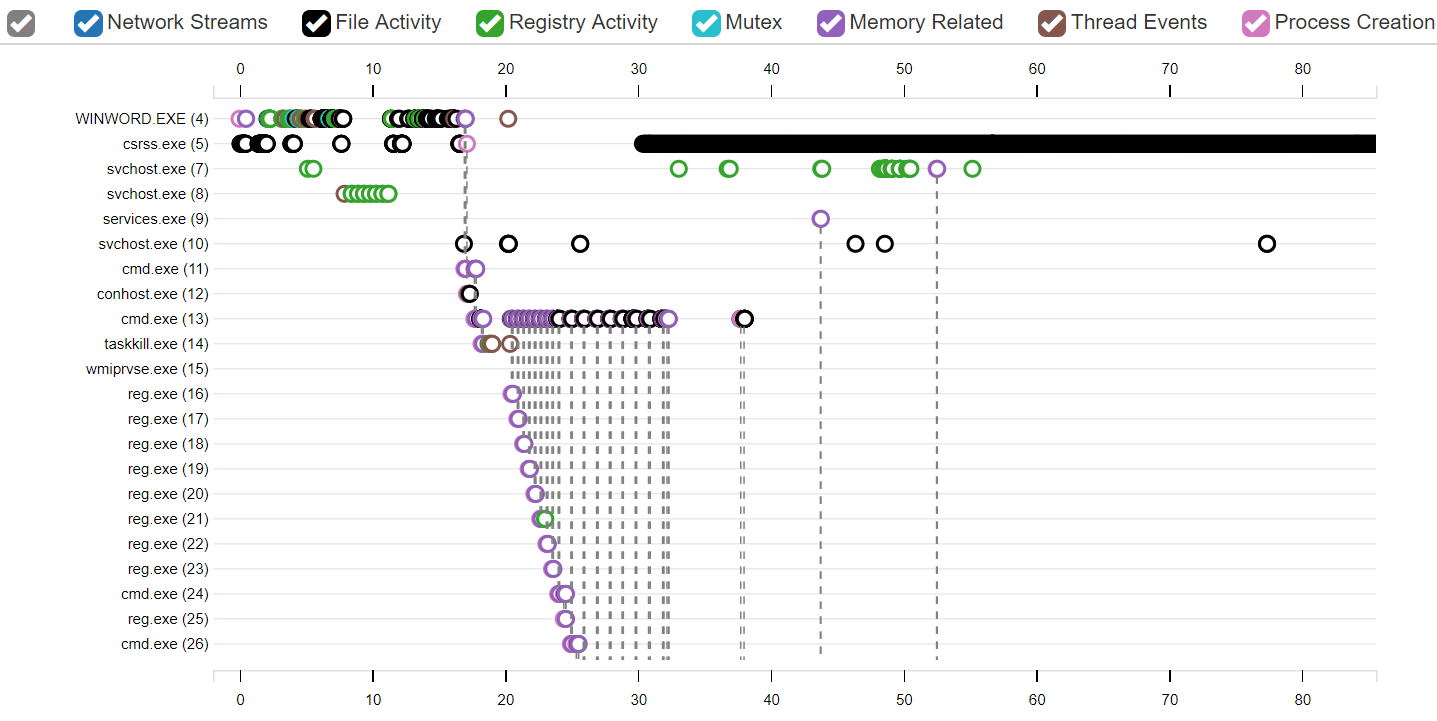
Process Timeline view
In addition to the popular Process Tree view, Threat Grid now offers a Process Timeline view, giving you far more detailed and granular insight into the sequential steps taken by a sample. When you need deep comprehension of malware activity, this is the place to look.
New Behavior Indicators
Behavior indicators are the building blocks of Threat Grid analysis and threat intelligence. They are the means by which Threat Grid detects suspicious or malicious characteristics and behavior. Every release, as a general rule, includes new behavior indicators. From June to August of 2018, we released over 100 new indicators, bringing the total count to over 1200 detectable actions that contribute to a sample’s overall threat score.
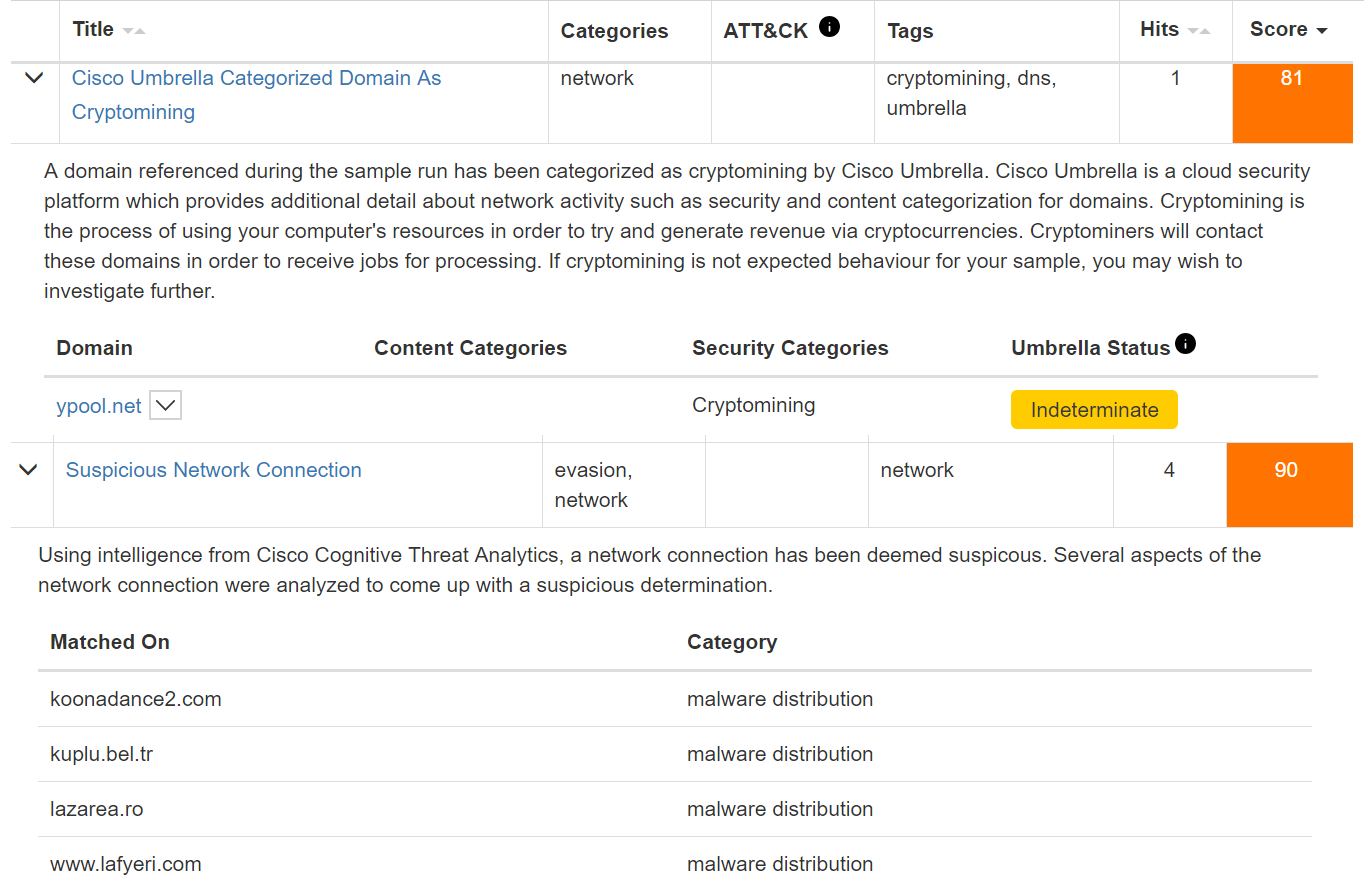
Of these new releases, a few are worthy of special mention. In a similar vein to the recent Cisco Threat Response integration, which allows you to view that tool’s insights directly in or from the Threat Grid console, we continue to integrate the capabilities of some of Cisco’s other Advanced Threat Solutions products, and leverage them within Threat Grid. The Umbrella reputation and categorization of network connection endpoints can now contribute to a sample’s Threat Score, and we leverage Cognitive Intelligence’s machine learning models to detect maliciousness from static file analysis and network traffic pattern analysis. As with all Behavior Indicators, when one is triggered, the specific details of the detection are recorded in both the web and JSON versions of the Analysis Report, available in the console or via the API.
Additional new features and improvements
The list above only includes the highlights. Many more UI and platform improvements have been made over the summer months – see the release notes for full details.
Additional content:
Threat Grid at Cisco’s Developer Network
Threat Grid now has a dedicated section in Cisco’s DevNet resources: https://developer.cisco.com/threat-grid/
In this section of Cisco’s Developer Network, you can find Learning Labs that will guide you through coding with Threat Grid’s powerful REST API. Check back for updates as we continue to grow this resource.
Demo Video
As well, I recently released a video on YouTube doing a demo of some of the primary features and capabilities of the Threat Grid Cloud portal. You can find that here.
More Blogs
In case you missed them, over the summer Jessica Bair and Evgeny Mirolyubov both wrote about Threat Grid here. Jessica detailed how Threat Grid was used in the SOC at RSAC to protect conference attendees, and Evgeny described how automation, integration, and machine learning come together to benefit Threat Grid and the entire Cisco Security portfolio.
Demo Friday
If you are interested in learning more about these new features, register for and attend my upcoming Demo Friday session on Threat Grid, on October 12 2018, in which I will be going them live and answering questions you may have. See more details and register for any of the upcoming Demo Friday sessions here.
Take care, and as I’m fond of saying, make use of Threat Grid to detonate your malware on our network, instead of your own! The Engineering team is already hard at work bringing you more new features; stay tuned here for future highlight overviews.