Part 1: Rude Awakening
Let us begin with some context in the form of a story.
I live in a very bad part of town and I am always worried that my car is going to get stolen or broken into. So, I just invested over a thousand bucks in this awesome vehicle alarm and security system. You know, one of those ultra-advanced systems that connects to an app on your smartphone, includes an ignition kill switch, vehicle tracker, cameras, motion detection, as well as all of the typical features you would expect. If someone enters the vehicle without my key fob, it calls my phone, and even takes pictures of the inside of the vehicle. I now feel so much better about parking my car outside. The company that sold me the alarm made me feel like my car was ‘un-steal-able’ and even if it was, I would have pictures of who did it and would be able to find it easily. Perfect. I feel protected. I can sleep at night.
The other morning, I went outside and strangely, it was gone…the shock sensor and its cut-wires lying on the ground where the car once sat. I think I stood there for a solid minute with my mouth open before I thought to do anything. I checked my phone – no call. I looked at the app – no pictures or interior motion detected. All appeared normal. Darn! (actually other words, but keeping it clean here) How could this happen? That alarm company assured me this was impossible. Heck, they are the most popular system on the market – everyone loves these guys. They have all of the ‘best’ and innovative features and no one makes vehicle security easier than these guys. And, I bought the top-of-the-line model, with all of the bells and whistles, just short of the biometric entry system. Wow! How could this have happened?
I called the police to file a report and see if the tracker could be used to find my stolen car. “Sure we will look for it.” The tracker required a connection, which didn’t exist. The app was useless unless something triggered it and the company that sold it to me, of course, wasn’t much help. “Looks like someone really wanted your car” they said. Long story short, the vehicle was found 26 days later on a burned-out flatbed in Mexico. What hadn’t been taken off of it was torched; no trace whatsoever.
Security Isn’t Easy
The moral of the story is two-fold. One, there is no such thing as easy security, at any price. As soon as you think you have achieved it, the unthinkable will certainly happen. Two: no amount of prevention or detection will ever overcome human motivation and ingenuity. Knowing that today’s attackers have the technology innovations of the entire industry at their fingertips when they attack us – ingenuity is boundless. Billions of dollars are made each year by attackers stealing our data. What better motivation than money. Considering much of what we are up against today is nation-state sponsored, everything becomes that much more complicated.
So, why waste all of these keystrokes on a story about my car being stolen? Simple; the story proves a very important point. That uber-cool vehicle security system, like so many of these modern-day, marketing-heavy all-in-one NG-Firewall products, do a great job of making the naïve feel safe. Until of course, the discovery of the data breach happens; and it has – countless times. Sometimes even to the same organizations multiple times- bypassing the uber-cool features of some of the most loved NGFW products on the market without as much as leaving a trace, or firing an alert. In fact, if you haven’t been breached yet, the likely reality is that you just haven’t found it yet. But, I am certain you felt pretty good when you got those shiny new boxes installed – the simple do-it-all-in-one-checkbox-UI, and all of the promises…oh those promises.
If you think that a single NG-Firewall with some advanced features that can identify applications and users, categorize some URLs and do some basic Intrusion Prevention is going to stop an attacker from stealing your data or worse, then those products are built and marketed exactly for you. Many times the NG-Firewall won’t even tell you anything happened, since it isn’t built to know everything.
Ignorance is bliss, right?
No.
Bliss is actual protection. These marketing-heavy NGFW vendors are making their living on your fear and in the same breath, telling you “security is easy” – we will protect you from the unknown and all you have to do is install this box, buy these licenses and click this check box. Well, actual protection is not easy. It never has been, and it never will be. If it was, we would be winning the war against the threat actors – but we are not.
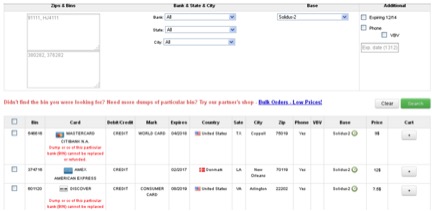
Whether you are responsible for protecting medical records, financial data, classified information, or otherwise, protection is your ultimate responsibility. My personal data (and yours) is on your network too and has been stolen along with everyone else’s during your data breach, whether it went public or not. A recent news story said that my identity is worth less than $1US dollar¹ and much of the data sold on the Dark Web has a money back guarantee. That is awesome. (Sarcasm)
Are You Protected (and Prepared)?
How confident are you in your solution? What mechanisms are in place for containment and visibility? Do you have an Incident Response plan? How long does it take your organization to assemble and execute an incident response action when (not if) a breach occurs? The statistics in the industry today would likely surprise you. Shockingly, the ‘ignorance is bliss’ theme runs rampant. Companies spend fortunes on storage and compute and spend as little money as possible on securing data. Attackers are counting on these factors. There is really no such thing as “cheap security”.
When something DOES happen, (hasn’t it? Or do you even know?), true bliss is the ability to fully understand how, why, by whom and what exactly was done, immediately. To instantly know the expanse of the breach, the scope, and be able to ensure rapid containment is critical. That helps me sleep at night.
There is a statistic that claims most threats exist on networks for 229 days on average before they are found. How much exploration, expansion and exfiltration can happen given that much time running rampant on your most precious resources?
This brings us to the real issue here. Most folks simply aren’t prepared – some are even in denial. Having a nice NGFW at the edge, some neat tools for logging and forensics, maybe a SIEM and an endpoint product that has, at minimum, AV protection, is what makes most folks comfortable thinking that they have done what they can. So let’s assume this is the norm and work from there.
Beyond Simply Policy
The landscape of the perimeter, where firewalls were once king, has changed dramatically over the years. The perimeter itself has dissolved, with the concept of “work” evolving from a place you went to something you just do – wherever you may be and whenever applicable. Wherever we can work from and by whatever means must also be considered to be attack paths.
So why is a threat-focused NG-firewall worth looking into? With a threat-focused NG-Firewall, the NGFW is actually just a small percentage of what it is actually doing to protect you. Just to be sure we are all on the same page; the industry² defines a NGFW as a single box that “provides advanced policy constructs based upon stateful firewall, application visibility & control, user-based controls, some URL or Web content security and an intrusion prevention system (IPS). “
That sounds pretty complete for a policy-based access-control device- which is what a Firewall actually is – and all it is. NGFW or UTM provides depth to the policy by allowing a permit/deny to be based upon any combination of the aforementioned elements. No matter how you look at it, a permit/deny, regardless of the policy depth and intelligence, is still just a binary decision. Allow what should be allowed, deny what should not; certainly not rocket science here. Most vendors will tie their inspection and resulting policy decision(s) to other products, like sandboxing or TI (Threat Intelligence) to provide additional context around the actual data being seen, in order to make the binary decision more precise.
From a Security Practitioners standpoint, policy is certainly a “piece” of a security solution, but that is almost the point where the Practitioners pick up and begin their work. Having a deep understanding of behavioral indicators within flows and data (even in compound communications), abnormal endpoint activities, hunting anomalies before they manifest as threats, incident controls, vulnerability management, outbreak or containment controls and remediation are just a few things that are considered ‘must-haves’ for a Practitioner. Let us not forget a logging, reporting, forensics and correlation tool that allows the Practitioner to manipulate all of these things – this is as critical as the systems providing the data.
Since many organizations implement the “Best-of-Breed” approach, Practitioners can quickly become what is defined as “tool-rich, Information-poor” – certainly not lending themselves to speedy detection and eradication of the types of modern threats seen today. This is potentially why the 229 day average detection time exists in the first place. This is where a threat-focused NG-Firewall can really help.
Another factor that seems to be overlooked frequently by the “NGFW-focused” is how much that is truly known about the target of the attack – the endpoint. Unless you are running a series of agents on every client (Windows, Mac, Linux, iOS, Android, etc.) how does one actually know what is at risk? For example, do I run an AV client, an Anti-Malware agent, a process tracker, etc. on every client? While it may be desirable from a visibility standpoint, agent fatigue is what results from this, and not every OS can be covered to the same level – every vendor has their limits for client support, etc. Regardless of the former, the reality is that deeply understanding the target is the only way that the data generated from all of the other tools can be used with a high confidence level. Allowing the Practitioner to focus on events that are confirmed to be a true-positive – and having the ability to prioritize their efforts and actions by greatest risk. Noise is the enemy of protection without capability to intelligently assess risk and impact; just ask some of the organizations that were involved in recent major data breaches. Noise was a normal occurrence, and obfuscated which event(s) of the thousands needed to be investigated or contained that led to the ultimate compromise. Thus a system that can properly evaluate risk, dynamically contain and make adjustments to policy based upon what is happening is almost a nirvana.
Now we are beginning to define a Threat-Focused NG-Firewall – a NGFW with Integrated Threat Defenses that Security Practitioners need to do their job.
Read Part 2: Enter Threat-Focused NG-Firewall






Good points
Train your Practitioners as they need to KNOW their job
Totally True..