This is Part 2 of our blog series about NG-Firewalls. See Part 1 here.
Part 2: Enter Threat-Focused NG-Firewall
What does a Threat-focused NG-Firewall do differently? Just about everything. Let’s compare the most popular NGFW systems on the market (typical NGFW) with the Cisco Firepower NG-Firewall system, (a Threat-Focused NG-Firewall).
If you consider the typical NGFW available from your choice of vendors, you are staring at a system that was designed for, and normally sold to, Network-focused Admins that need more visibility into their policy and desire some additional depth of what they can choose to allow or deny. Typical policy has been circumvented by the ever-present danger of threats, and thus policy management that actually has any effect on protection has become extremely difficult. The limiting factor with the standard NGFW is that it can only accurately enforce permit or deny on what it understands. The classic example is the firewall that employs IDS/IPS signatures in the packet path to ‘detect’ what it understands and take an action – with an output event that something was seen and some basic information about who and what, along with the action taken.
A Threat-focused NG-Firewall system by contrast, looks at the world differently – with its foundation a set of detection engines that leverage both signature-based and signature-less technologies to hand out verdicts on data flows, files and other bits of information. How well this is done depends on the intelligence built into the verdict engines – not only allowing detection and dispositions of point-in-time events, like many other vendors do, but also detection beyond the event horizon, which is the Cisco Firepower NG-Firewall’s most obvious differentiator. The event horizon is the point-in-time where a system first sees something good, bad or unknown and issues a verdict or disposition.
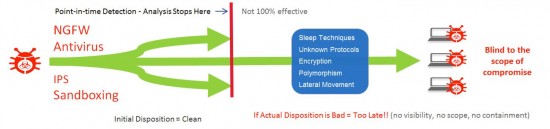
If the data was issued a clean disposition, a typical NGFW will no longer attempt to view or track that data because a clean disposition has already been issued and continuing to watch ‘everything’ takes extra horsepower that most NGFW vendors are not willing to dedicate in favor of better packet-in/ packet-out performance. NGFW was designed to be sold to Network Admins remember? We expect routers to move packets as fast as possible – that is the typical focus of evaluation with the standard NGFW; Speed, Simplicity and Price.
Continuous Analysis
To actually defend and protect your network from modern threats… speed kills.
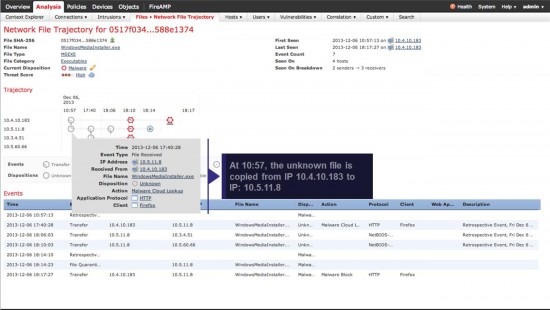
I am not trying to say that you can’t have good performance, just that packet-in/packet-out speed doesn’t equate to being thorough, especially when most of the advanced attacks we see today do not immediately show up as malicious and are used only once in most cases. Security is about detecting, understanding and stopping threats. Using the foundation of visibility you can understand context and apply collective intelligence to detect a threat. Going beyond the event-horizon uses a concept known as ‘continuous analysis’ to continue watching the activity of information that has already passed initial evaluation and been given a clean or unknown disposition. When modern malware, especially zero-day, single-use malware that is previously unknown changes behaviors, a threat-focused system can retrospectively evaluate and detect behaviors like lateral movement, sleep techniques, polymorphism, encryption or even unknown protocols. With this new detection, a new malicious (bad) verdict can be issued and further actions can be automatically taken – even retrospectively.
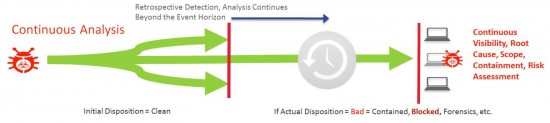
If a threat is detected retrospectively or in real-time, extremely high-confidence, automated enforcement, or ‘Adaptive Security’ is used to stop the threat. In order to accomplish this, the system must be able to record everything that is seen to have a continuous capability to detect threats hours, days or even weeks later. Visibility, context and attribution of Threat Actor, threat, and target of threat must be part of the same process in order to be effective – not separate bolt-on systems. This is what the Firepower Threat-centric NG-Firewall is built to do.
Let’s look at an example of what a continuous analysis flow looks like within the Firepower Management Center (which manages Firepower NG-Firewalls) on a file that was downloaded by a user from their browser and initially given an ‘unknown’ disposition at point-in-time, not knowing that this file contains a day-zero Malware threat (never seen before). Keep in mind that this is all done in an environment where no additional client agent software has been installed to provide details to the system. You will see the value of adding an optional Advanced Malware Protection (AMP) host agent later in the process.
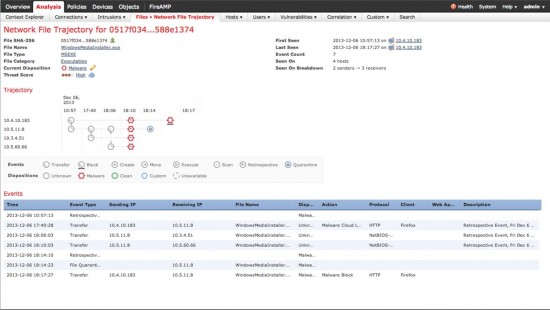
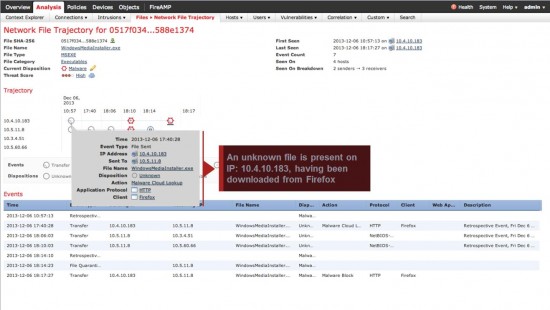
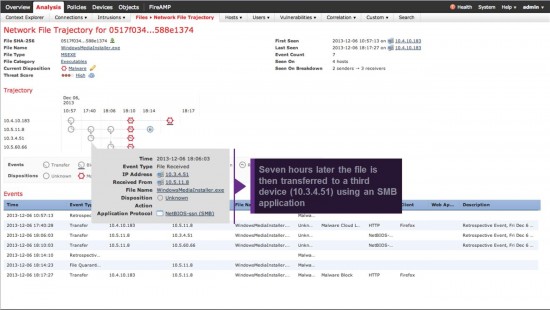
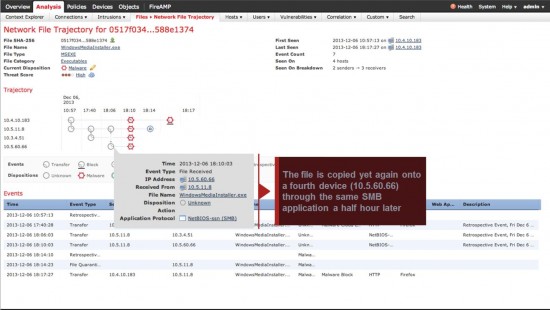
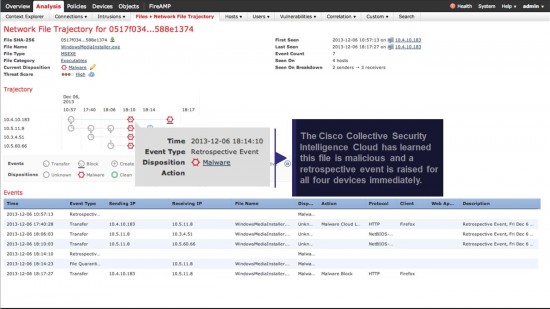
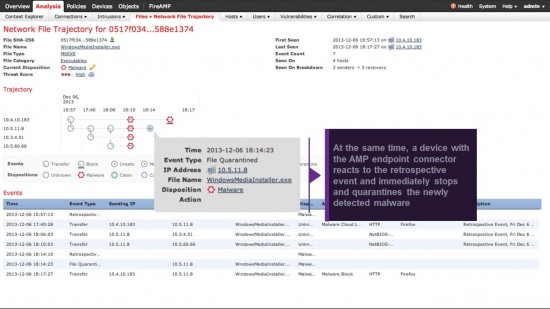
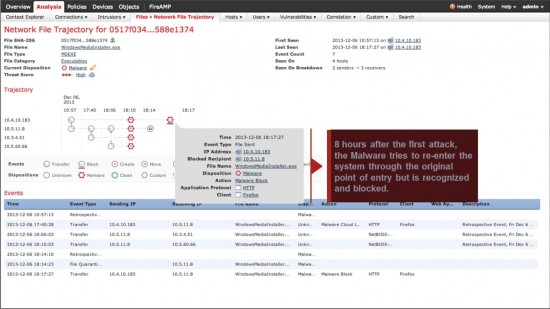
Since the information is constantly tracked, this continuous temporal visibility also enables Automatic Threat containment and scope, impact analysis and incident response as well as all hierarchical relationships to Patient-zero, etc. – all useful actions and information for the Practitioner. Due to the context and visibility of these functions, the high-confidence Security Automation is suddenly available to the process – the ability to self-adjust both policy and actions, provide automatic outbreak controls, attribution and parent-child relationships, all while a typical NGFW would be completely blind to what is happening and unable to perform these functions.
Read Part 3: Challenges of the Typical NGFW






Great article!
If no software is installed on the end hosts, how can you track? It seems that they are being sent to a different subnet so you may have the device spanning off the router or use the ng device as the router. But how would that stop or notify a lateral movement within the same Layer 2 subnet with no additional software like you said.