This blog was co-authored by Christian Clasen, Technical Marketing Engineer at Cisco.
Welcome to the first in a series of blogs on the future of the email security market and how you can leverage the latest technologies to secure your cloud email deployments. Our goal is to make these blogs easy to consume and publish them on a regular basis.
While much of the content we will cover here will be about new and emerging ways to protect cloud mailboxes, it’s important to start with a view of the continued relevance of the Secure Email Gateway (SEG). The SEG technology space, and Cisco’s Cloud Email Security (CES) in particular, is still a valuable part of the enterprise content security strategy. It’s strength lies in its versatility and comprehensive configuration options that can produce unparalleled efficacy when tuned by knowledgeable administrators and engineers.
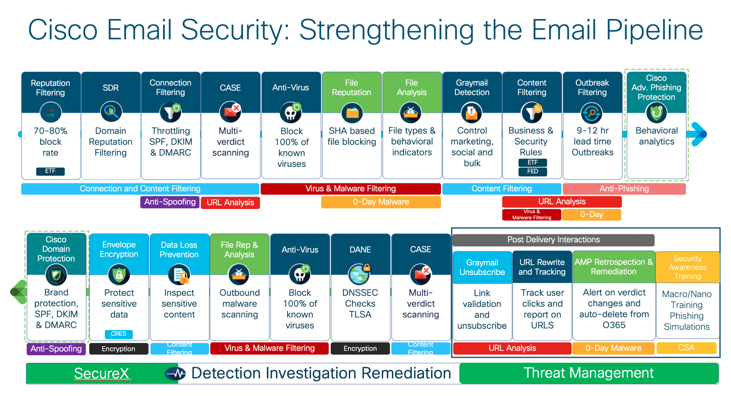
The graphic above illustrates just how comprehensive Cisco’s gateway offering is. In the top left, we can see connection-time protections that are only possible with SEG products. Administrators have long accepted that essential mail server hardening was not sufficient to protect their environments from attacks like directory harvesting. With the move to O365 administrators no longer have to perform infrastructure maintenance like patching, but well-resourced security organizations still value granular connection time controls to defeat complex attacks that target the infrastructure rather than user’s mailboxes. The Connection and Content Filtering engines referenced in the graphic above when correctly configured are well-positioned to mitigate this kind of attack.
This is just one example of the kind of protection that Cisco’s Cloud Email Security (CES) allows customers to bring with them when they migrate away from on-premises email servers. Experienced CES administrators are adept at crafting message filters to deal with targeted campaigns and emerging threats that have not yet been identified up by research groups or content scanning engines. The ability to narrow these rules to groups and individual users is powerful in the hands of security operations engineers who require scalpels to meet the varying demands of their departments. These often require specialized policies that address particular needs while maintaining the integrity of their email communications. The availability of multiple quarantines addresses shortcoming of the junk folder-centric Microsoft approach for those who need a more nuanced set of tools.
These examples do not cover all of the use-cases and benefits of CES for cloud email customers (for that, you can explore the user guides and product video), but they do illustrate a key message. The SEG space offers granular, customizable controls that are incredibly powerful in the hands of well-trained administrators and engineers.
If yours is one of the organizations who don’t require the granular controls and customization of SEG and simplicity is the most appealing aspect of moving to the cloud, then follow us as we continue this series by examining emerging cloud email security technologies.
In the meantime, read more about the layered approach to email security that makes Cisco Email Security an industry leader.





