This post was authored by Earl Carter & Jaeson Schultz.
Talos is always fascinated by the endless creativity of those who send spam. Miscreants who automate sending spam using botnets are of particular interest. Talos has been tracking a spam botnet that over the past several months that has been spamming weight loss products, male erectile dysfunction medication, and dating/casual sex websites. These are all typical products one would expect to be purveyed through spam. What interests us about this spam are some of the ways the spam is constructed to try and evade detection (a.k.a. spam filters).
Beginning in March, Talos noted an absolute explosion in the usage of link shortening services in spam. After looking into the cause we found botnet ‘unknown2250’, as it is called by the Composite Block List (CBL), to be one of the primary parties responsible for this massive increase.
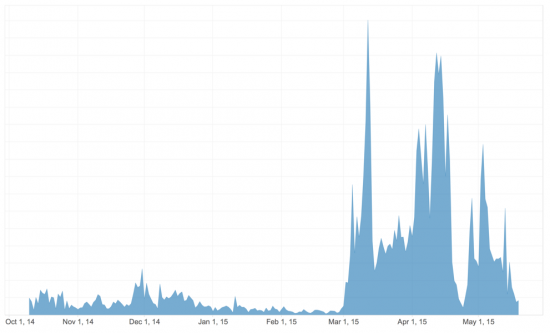
The use of link shorteners to disguise URLs in spam is not new. In August 2014, Andrew Conway of Cloudmark published a blog on the use of link shorteners in spam. According to the data from Cloudmark taken from July 2014, Twitter’s t.co shortener was the most abused link shortener in spam. Since that time, spammers have evolved to use other shorteners that don’t have the same resources to fight abuse as Twitter does. Below is a breakdown of the number of shortened links found in spam messages by link shortening services. To keep the chart from getting too cluttered, we have only included link shorteners that exhibited interesting or significant changes in activity over the past six months.
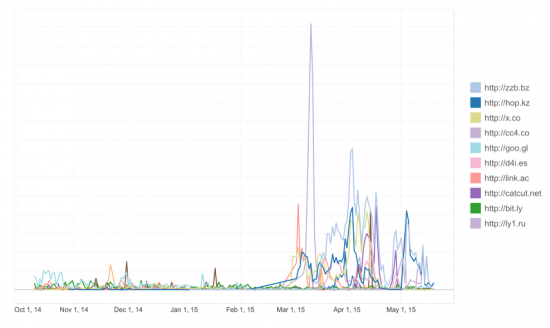
The botnet Talos has been tracking continues to use URL shorteners to disguise their spam links. It is interesting to note that with the d4i.es shortener, the threat actors are actually using subdomains, such as 5rkd.d4i.es for each shortened URL to further obscure the requests. In our graph, we consolidated all of the d4i.es requests so that we could get an accurate summation of the data. Because the botnet is somewhat indiscriminate in the recipient addresses to which it sends email, Talos has received copies of this spam campaign via our spam trap network.
In addition to using shortened links, the same group of miscreants has begun using compromised third party websites to host HTML pages that perform redirection. After successfully compromising a victim’s web hosting account, the attackers create a subdirectory consisting of random letters and numbers. An HTML page is placed inside the new directory, and functions to redirect users to various types of landing pages. For example, see the link below:
This is quite similar in spirit to the domain shadowing attacks previously reported by Talos. However, in this instance new subdirectories are being created instead of new hostnames. In both instances, criminals are taking advantage of the fact that many small websites are not very well maintained, and those administrators who are charged with their upkeep often will not log in very often, or may not notice new subdirectories that show up in their web hosting folders.
The spam messages all seem to take the minimalist approach, sending as little content as possible to give anti-spam scanners as little text as possible to write filters against. The messages are also all clearly generated by a program, as evidenced by spam that has been sent after a malfunction of some kind in the spammers’ ratware. Note the variable ‘%INTRO’ which should have been replaced by a short, random introductory text.
Laziness Strikes Again
For as much trouble as these spammers have gone to in order to create a botnet, compromise third party websites, create shortened links at many different link shortening services, and so on, you would think this group would do more to secure their destination domains from discovery/blocking. But spammers are also notoriously lazy. For example, expanding many of the shortened links from the casual sex spam leads to the non-whois-privacy-protected domain ‘dating-magic-laid2.com’. The whois information for the domain appears below.
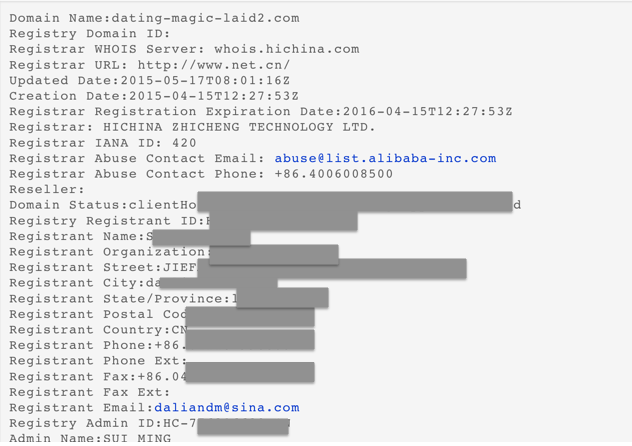
It turns out that the email address used to register this domain, ‘daliandm@sina.com’ is also responsible for over 60 other domain registrations with some gems such as ‘fastpillshipper.com’, and ‘time-2getlucky.com’. The ‘daliandm@sina.com’ email address registered its first domain over a year ago, and the same email address was used to register new domains just in the past week. This author can only conclude that the botnet’s spam campaigns must generate enough income that it melts away any concern over reusing the same email address in malicious domain registration after malicious domain registration.
Conclusion
This is yet another example of threat actors evolving to succeed in reaching end users to deliver malicious content. Other recent examples include the use of dynamic DNS (DDNS), domain shadowing, and fast flux DNS. The one thing these examples have in common is that they are trying to obfuscate where the payload is being hosted and the domains being used. By hiding in URL shorteners attackers hope to hide the actual domains and hosts that contain the content. As the actors evolve so does the detection and the importance for covering multiple layers of the network to ensure they are blocked. In the example discussed here, the attack technique failed as it was properly detected as soon as the spam began.
Protecting Users
ESA can block spam and phishing message sent by threat actors as part of their campaigns.
can block spam and phishing message sent by threat actors as part of their campaigns.
CWS or WSA web scanning prevents access to malicious websites with a negative reputation.
Advanced Malware Protection (AMP) and Network Security products (such as IPS and NGFW) are not applicable in this case as there’s no malware directly involved.