Our data shows that there are 5 to 10 breaches per 1000 seats every week. That number is staggering and exemplifies the limits of traditional prevention. Most of these attacks will be done using repackaged malware distributed by known threat actors. We also see that such attacks not only remain undetected for a very long time, but tend to escalate with further malware. A typical scenario starts as a seemingly innocent download of a free tool bundled with adware that later on injects malicious advertisements through the web browser. Only later, when more data is collected, we see other malware ranging from info stealers and banking Trojans to ransomware. And finally, any stolen data will be used against you – in a targeted attack. How do we effectively respond to this?
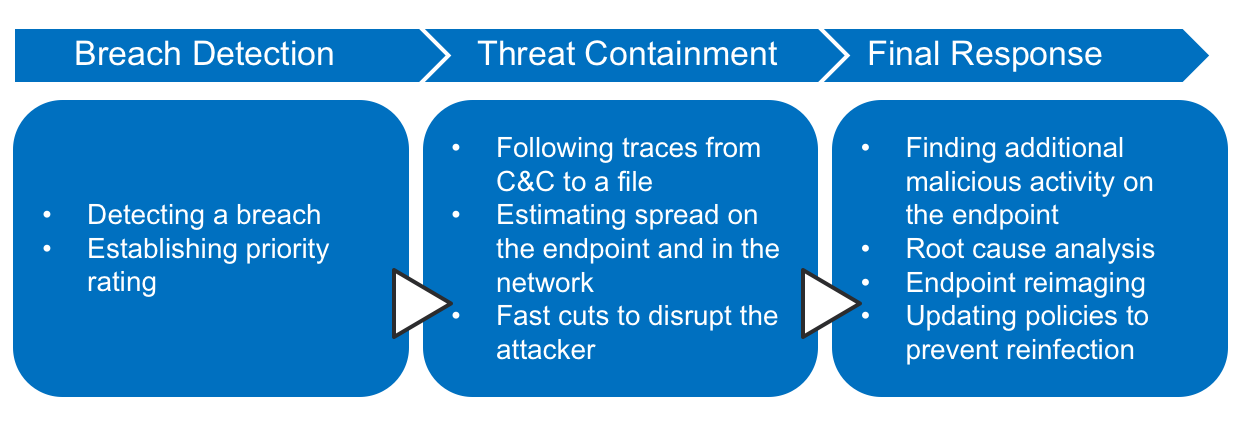
Let’s use Cisco’s advanced security portfolio for breach detection and mitigation to address these problems. I will show you how we can take an unknown infection or a full-scale breach (that passed the perimeter defenses), figure out how it happened, and walk back from it faster than ever before. To successfully do so, let’s focus on a 3-step process:
- Breach Detection and Prioritization – reveal the presence of a breach and its objectives
- Threat Containment – swift action is required to prevent the acute risk of data leaks
- Final Response and Remediation – more thorough analysis of the root cause and proper cleaning
Breach Detection and Prioritization
Detecting a breach is the most challenging of the three steps. A breach indicates that the attacker has penetrated all defenses and is likely going to impersonate somebody else and use gathered information for further malicious actions. There are two types of attacks resulting in a breach. The first type represents established attackers using new or polymorphic variants of malware. The second is completely new attacks or attackers that do not have coverage in security databases and feeds, and thus require a generic analytics-based detection system.
Before we even get to investigate anything, the analyst has to decide how to prioritize. To be highly actionable we want the risk to be determined automatically and aggregated with as much context as possible. This is hard. Remember that we are likely dealing with malware that managed to infect the endpoint – chances are that nobody really knows the exact origin and purpose. Generating a unique sample, domain and communication pattern has become a commodity. Also, the actual malicious mission often varies – the attackers are opportunistic and might steer the malware after their initial foothold. While the actual malicious activity cannot be fully predicted, having a good estimate of the attacker’s intent helps tremendously. Here are the techniques used by Cisco to solve this:
- Campaign attribution by behavioral similarity of command and control communication – Cognitive Threat Analytics (CTA) provides risk rating natively based on observed behavior for every single detection. Moreover, whenever an attribution to a known malicious campaign can be made through behavioral similarity, the campaign description is given with details on the techniques, intents and recommended remediation steps
- Attack prediction by global sandboxing database correlation – Threat Grid estimates likelihood of a particular mission based on previously observed behavior from malware of the same origin or behavior. This corresponds to the arsenal that the adversary has and probability that it will be utilized
- Detecting executed malware and presence of IoCs with retrospection – AMP for Endpoints records file activity, regardless of the file’s disposition. If malicious behavior is spotted later on, AMP sends your security team a retrospective alert, that contains the complete history of the threat: where the malware came from, where it’s been, and what it’s doing
Threat Containment
Breaches can result in data loss within a matter of hours so the goal of this phase is to follow traces from command and control channels to individual processes and files so that they can be stopped and removed. The same traces are also used to estimate the spread. The key here is speed and automation – this is not a forensics exercise. The security architecture must help us reveal those traces and apply quick and dirty cuts that will disrupt an ongoing attack. We should also block malicious domains and IPs that correspond to the attack. This step includes:
- Following traces from C&C to a particular file on the endpoint – AMP for Endpoints integration with CTA makes it simple to tie C&C communication to a particular file or process on a host
- Estimating the spread on the endpoint and in the network – Device and File Trajectory features in AMP for Endpoints show device and file level details, as well as provide information about other machines where the file was seen
- Applying the policy to block malicious file and network communication across the entire environment – placing a file into quarantine and blocking communications with IP addresses and domains that represent C&C is a simple task in the AMP for Endpoints console using Outbreak Control features
Final Response and Remediation
Immediate reaction prevents the imminent risk of a data breach but is unlikely that the malware would be completely eradicated making the endpoint safe to use. First of all, there are likely other components and backup mechanisms of the attack. Second, we have not determined the root cause and we may still be vulnerable to reinfection. Finally, once malware is installed, it often hurts the security posture of the machine. As a result, the majority of breaches cannot be automatically cleaned and require a reimage of the endpoint. To prevent future attacks a policy update may also be required. This step includes:
- Finding additional malicious activity on the endpoint – use Device Trajectory feature for visual representation of processes and file execution on your endpoints to get a better understanding of what preceded the infection and which other components could be involved
- Analyzing the root cause – should be done before endpoint is reimaged to ensure the door is closed for attackers who try to get in using the same path. AMP for Endpoints helps determine the applications that were seen introducing malware into the network, as well as points out the vulnerabilities in those applications
- Cleaning up the affected endpoints – due to the complex nature of infections these days, it’s almost impossible to record or predict all modifications that were done to the endpoint as a result of an active infection. Therefore, the most effective way of cleaning a breached machine is to send it for reimage. For the low or medium risk infections, you might be able to clean the infection using endpoint cleaning tools, however be careful and watch for reinfections if you choose to do so
- Updating policies to prevent reinfection – after the cleaning is done, policies should be reviewed and updated accordingly
As we have seen, dealing with a breach takes several steps, that should be done very quickly, and requires that tools be used in a very orchestrated way. We need a powerful analytics platform to detect and prioritize the breach in the first place. After that, we collect contextual information about C2 communications and tie it back to malicious files or processes on the endpoint. We immediately block those files and communications in case the breach has a critical risk level (damaging to the organization, e.g. data exfiltration), and then automatically quarantine the endpoint. In our final response, we have more time to assess the endpoint, uncover other components of the attack, perform root cause analysis and clean up.
Remember, you only have hours before data stealing begins!
Review a practical example of how Incident Response can be done using Cisco’s Advanced Threat Solutions:
For more in-depth information on operationalizing Cisco’s Advanced Threat Solutions, review the Cisco Live session below:
https://www.ciscolive.com/us/learn/sessions/session-catalog/?search=brksec-2047&showEnrolled=false







Great post, very informative and useful.