You may think that cybercrime takes place in hidden corners of the Internet, where the malicious actors lurk in dark web forums and utilize heavily encrypted networks that require complicated software and extensive authorizations just to access.
Unfortunately, that’s not always the case. Sometimes such activity takes place in very public places, such as social networks.
Researchers at Cisco Talos have uncovered a vast collection of criminal groups with hundreds of thousands of members operating on Facebook. More than 70 groups have been found so far to be using the social media platform to connect with other criminals, share and sell tools, techniques and stolen data and, in some cases, to scam each other. Talos was able to establish, via additional research and analysis, that some of the tools being shared via the Facebook groups, can be connected to malicious activity from prior campaigns that Talos has monitored.
In all, Cisco Talos found 74 groups, with a total of 385,000 members, posting information that looked sketchy at best, illegal at worst. That’s the equivalent of the population of a city like Tampa, Florida. These groups are marketplaces and communities for criminals looking to buy and sell stolen information or cybercrime tools to launch phishing campaigns. From the Talos post: “We saw spammers offering access to large email lists, criminals offering assistance moving large amounts of cash, and sales of shell accounts at various organizations, including government.”
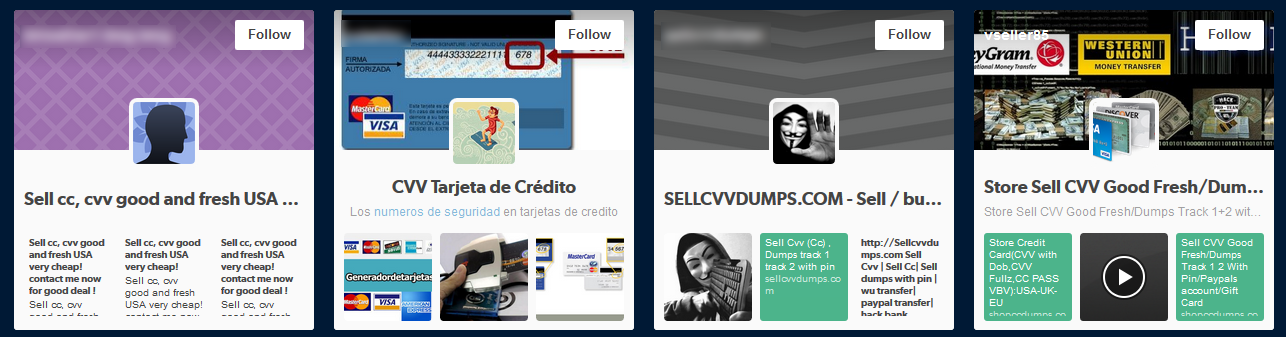
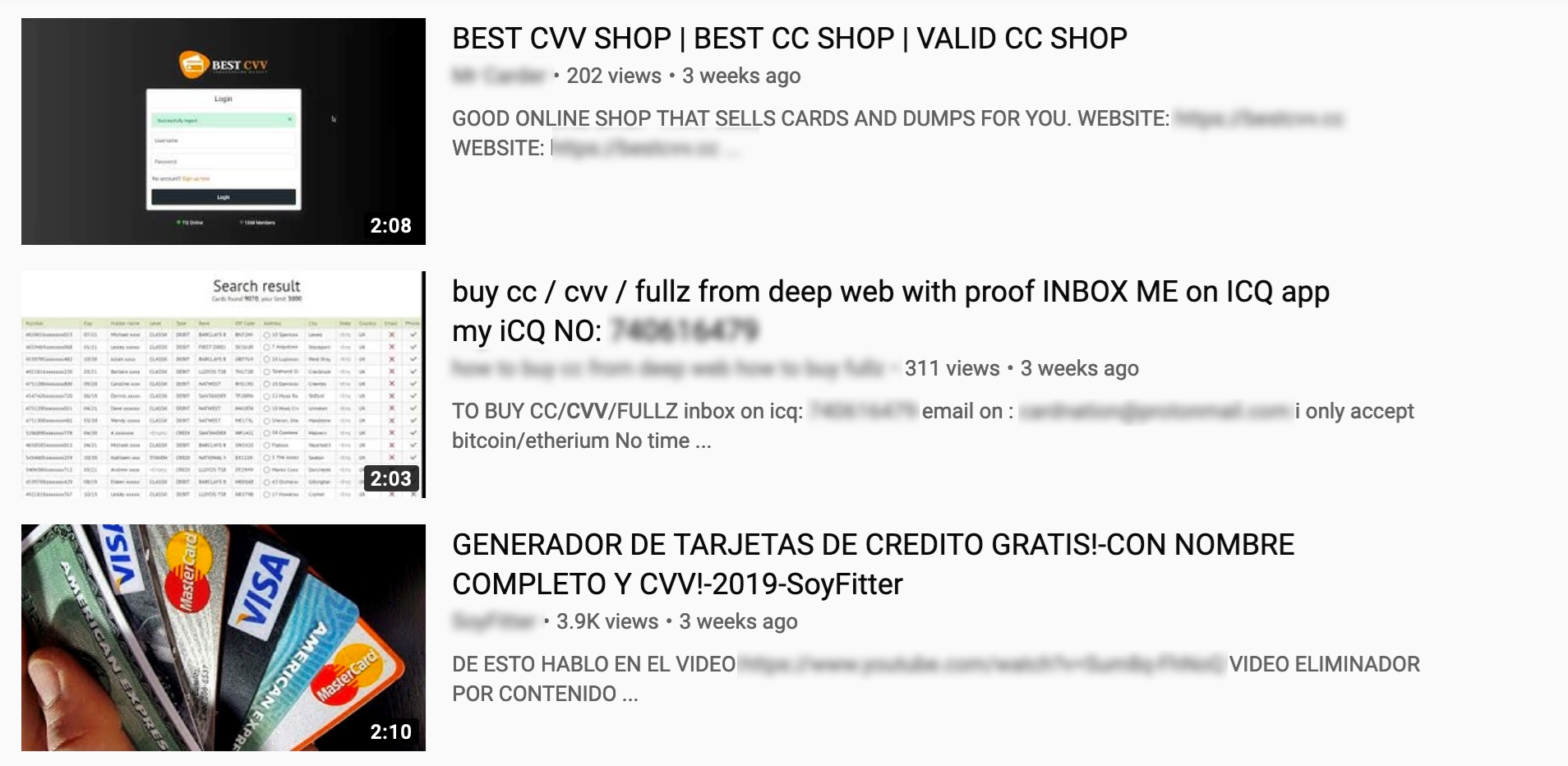
Finding this social media activity is quite simple. As stated in Talos’ blog, punching in keywords like “spam,” “carding,” or “CVV” will return multiple results. This activity isn’t limited to just Facebook either. Typing those same keywords into any number of social networks will return posts or groups advertising and advising on such activity.

It’s important to note that it doesn’t appear as though cybercriminals have only recently discovered social networks as a vehicle to assist in their illicit activity. Some of the Facebook groups discovered have been around for as long as eight years. Nor is this the first time that a light has been shined on their activity. In fact, almost exactly one year ago security research Brian Krebs exposed 120 similar such groups with approximately 300,000 members. These groups were reportedly shut down, but that appears to have done little to deter those involved with such activities.
So how does one protect him or herself from such activity? The silver lining here is that users are not being targeted directly through this social media activity. The scam or theft of the personal data being discussed by the actors has already occurred, likely through data breaches, point of sale compromises, phishing scams, or by keyloggers on compromised devices or web sites. This data has been organized into packages, or “dumps” of cards containing the card number, expiration date, and CVV number. In one post, we see 137 CVV details on sale for $300, or 5 for $25.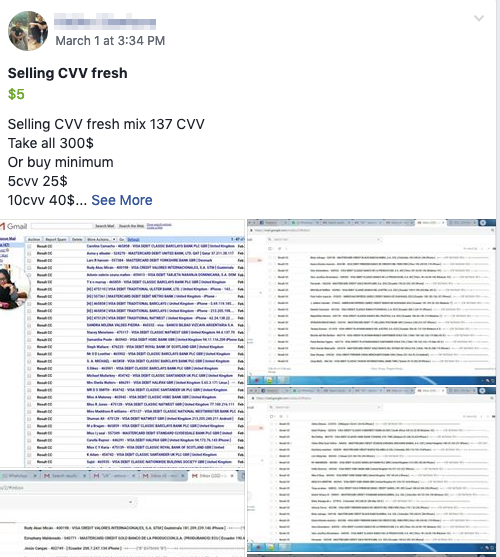
While the activity doesn’t target users directly, some of the actors involved are clearly participating in other malicious activity, such as phishing campaigns and malware distribution. While it is concerning to see the buying and selling of personal information out in the open, these groups are also an origin of spam and phishing services. And as we all know, email is the most common delivery vector for malicious activity.
Consider the following as part of a layered defense against the kinds of criminals that Talos has exposed:
- Cisco Email Security includes advanced threat defense and phishing capabilities that detect, block, and remediate threats in incoming email faster.
- Umbrella can be used to identify and block domains involved in malicious activity.
- Threat Grid helps identify malicious file behavior and automatically informs all Cisco Security products.
- Advanced Malware Protection (AMP) for Endpoints offers continuous monitoring and patented retrospective security capabilities that provides a last line of defense against malicious files targeting the endpoint.
- Cisco Threat Response can be leveraged to determine if threats identified as being distributed by malicious actors are present in your network.
Read all the information, including how Talos worked with Facebook to take down the groups we alerted them to.
Like this post? Subscribe to the Threat of the Month blog series and get alerted when the next blog post is released.





